Post Syndicated from Ashley Whittaker original https://www.raspberrypi.org/blog/building-a-business-with-vnc-connect-on-raspberry-pi/
Our friends over at RealVNC are having a whale of a time with Raspberry Pi, so they decided to write this guest blog for us. Here’s what they had to say about what their VNC Connect software can do, and how Raspberry Pi can be integrated into industry. Plus, hear about a real-life commercial example.
What is VNC Connect?
RealVNC’s VNC Connect is a secure way for you to control your Raspberry Pi from anywhere, as if you were sat in front of it. This is particularly useful for Raspberry Pis which are running ‘headless’ without monitor connected. The desktop can instead be presented in the VNC Connect Viewer app on, say, a wirelessly-connected iPad, from which you have full graphical control of the Raspberry Pi. The two devices do not even have to be on the same local network, so you can take remote control over the Internet. Which is great for roaming robots.
You can read more about RealVNC for Raspberry Pi here. It’s free to get started for non-commercial use.
Commercial potential
RealVNC have seen an increase in the use of Raspberry Pi in business, not just at home and in education. Raspberry Pi, combined with VNC Connect, is helping businesses both to charge for a service that they couldn’t previously provide, and to improve/automate a service they already offer.

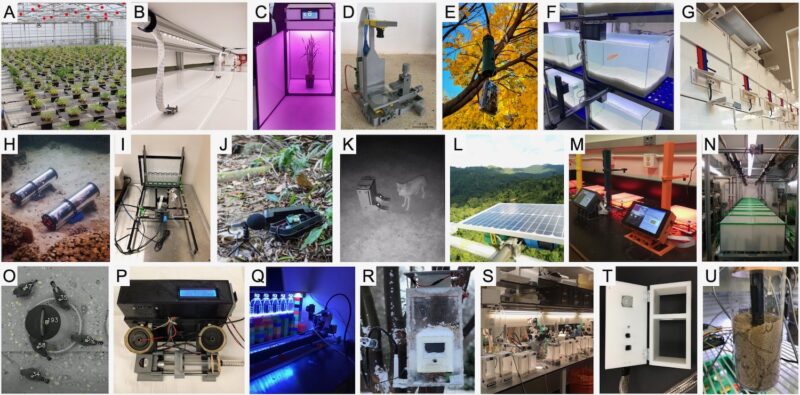
For example, Raspberry Pi is a useful, as well as a cost effective, “edge device” in complex hardware environments that require monitoring – a real IoT use case! Add VNC Connect, and the businesses which perform these hardware installations can provide monitoring and support services on a subscription basis to customers, building repeat revenue and adding value.
With VNC Connect being offered at an affordable price (less than the price of a cup of coffee per month for a single device), it doesn’t take these businesses long to make a healthy return.
A commercial example: monitoring solar panels
Centurion Solar provides monitoring software for home solar panels. Each installation is hooked up via USB to a Raspberry Pi-powered monitoring system, and access is provided both to the customer and to Centurion Solar, who run a paid monitoring and support service.

Having every new system leave the factory pre-installed with VNC Connect allows Centurion Solar to provide assistance quickly and easily for customers, no matter where they are, or how tech-savvy they are (or aren’t).
The software is currently being used in over 15,000 systems across 27 countries, with more new users every week.
“We’ve gone from being in limp mode to overdrive in one easy step, using RealVNC as the driving force to get us there.”
Johan Booysen, Founder at Centurion Solar
You can read more here.
Possibilities across many sectors
There are many more industry sectors which could be considering Raspberry Pi as a lightweight and convenient monitoring/edge compute solution, just like Centurion Solar do. For example:
- Energy
- Manufacturing
- Healthcare
- Transport
- Agriculture
- Critical National Infrastructure
The possibilities are only limited by imagination, and the folks down the road at RealVNC are happy to discuss how using Raspberry Pi in your environment could be transformative. You can reach us here.
From the engineers to the CEO, we’re all Raspberry Pi enthusiasts who love nothing more than sharing our experience and solving problems (our CEO, Adam, even publishes a popular bare-metal Raspberry Pi operating system tutorial on Github).
The post Building a business with VNC Connect on Raspberry Pi appeared first on Raspberry Pi.