Post Syndicated from Vesselin Tzvetkov original https://aws.amazon.com/blogs/security/integrating-aws-cloudformation-security-tests-with-aws-security-hub-and-aws-codebuild-reports/
The concept of infrastructure as code, by using pipelines for continuous integration and delivery, is fundamental for the development of cloud infrastructure. Including code quality and vulnerability scans in the pipeline is essential for the security of this infrastructure as code. In one of our previous posts, How to build a CI/CD pipeline for container vulnerability scanning with Trivy and AWS Security Hub, you learned how to scan containers to efficiently identify Common Vulnerabilities and Exposures (CVEs) and work with your developers to address them.
In this post, we’ll continue this topic, and also introduce a method for integrating open source tools that find potentially insecure patterns in your AWS CloudFormation templates with both AWS Security Hub and AWS CodeBuild reports. We’ll be using Stelligent’s open source tool CFN-Nag. We also show you how you can extend the solution to use AWS CloudFormation Guard (currently in preview).
One reason to use this integration is that it gives both security and development teams visibility into potential security risks, and resources that are insecure or non-compliant to your company policy, before they’re deployed.
Solution benefit and deliverables
In this solution, we provide you with a ready-to-use template for performing scanning of your AWS CloudFormation templates by using CFN-Nag. This tool has more than 140 predefined patterns, such as AWS Identity and Access Management (IAM) rules that are too permissive (wildcards), security group rules that are too permissive (wildcards), access logs that aren’t enabled, or encryption that isn’t enabled. You can additionally define your own rules to match your company policy as described in the section later in this post, by using custom profiles and exceptions, and suppressing false positives.
Our solution enables you to do the following:
- Integrate CFN-Nag in a CodeBuild project, scanning the infrastructure code for more than 140 possible insecure patterns, and classifying them as warnings or a failing test.
- Learn how to integrate AWS CloudFormation Guard (CFN-Guard). You need to define your scanning rules in this case.
- Generate CodeBuild reports, so that developers can easily identify failed security tests. In our sample, the build process fails if any critical findings are identified.
- Import to Security Hub the aggregated finding per code branch, so that security professionals can easily spot vulnerable code in repositories and branches. For every branch, we import one aggregated finding.
- Store the original scan report in an Amazon Simple Storage Service (Amazon S3) bucket for auditing purposes.
Note: in this solution, the AWS CloudFormation scanning tools won’t scan your application code that is running at AWS Lambda functions, Amazon Elastic Container Service (Amazon ECS), or Amazon Elastic Compute Cloud (Amazon EC2) instances.
Architecture
Figure 1 shows the architecture of the solution. The main steps are as follows:
- Your pipeline is triggered when new code is pushed to CodeCommit (which isn’t part of the template) to start a new build.
- The build process scans the AWS CloudFormation templates by using the cfn_nag_scan or cfn-guard command as defined by the build job.
- A Lambda function is invoked, and the scan report is sent to it.
- The scan report is published in an S3 bucket via the Lambda function.
- The Lambda function aggregates the findings report per repository and git branch and imports the report to Security Hub. The Lambda function also suppresses any previous findings related to this current repo and branch. The severity of the finding is calculated by the number of findings and a weight coefficient that depends on whether the finding is designated as warning or critical.
- Finally, the Lambda function generates the CodeBuild test report in JUnit format and returns it to CodeBuild. This report only includes information about any failed tests.
- CodeBuild creates a new test report from the new findings under the SecurityReports test group.
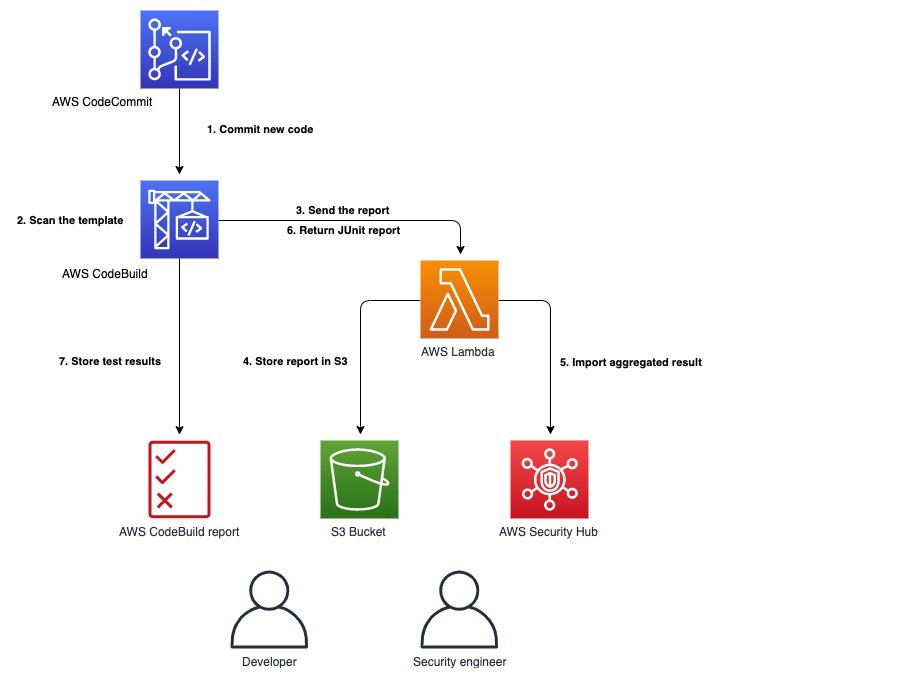
Figure 1: Solution architecture
Walkthrough
To get started, you need to set up the sample solution that scans one of your repositories by using CFN-Nag or CFN-Guard.
To set up the sample solution
- Log in to your AWS account if you haven’t done so already. Choose Launch Stack to launch the AWS CloudFormation console with the prepopulated AWS CloudFormation demo template. Choose Next.
 Additionally, you can find the latest code on GitHub.
Additionally, you can find the latest code on GitHub. - Fill in the stack parameters as shown in Figure 2:
- CodeCommitBranch: The name of the branch to be monitored, for example refs/heads/master.
- CodeCommitUrl: The clone URL of the CodeCommit repo that you want to monitor. It must be in the same Region as the stack being launched.
- TemplateFolder: The folder in your repo that contains the AWS CloudFormation templates.
- Weight coefficient for failing: The weight coefficient for a failing violation in the template.
- Weight coefficient for warning: The weight coefficient for a warning in the template.
- Security tool: The static analysis tool that is used to analyze the templates (CFN-Nag or CFN-Guard).
- Fail build: Whether to fail the build when security findings are detected.
- S3 bucket with sources: This bucket contains all sources, such as the Lambda function and templates. You can keep the default text if you’re not customizing the sources.
- Prefix for S3 bucket with sources: The prefix for all objects. You can keep the default if you’re not customizing the sources.
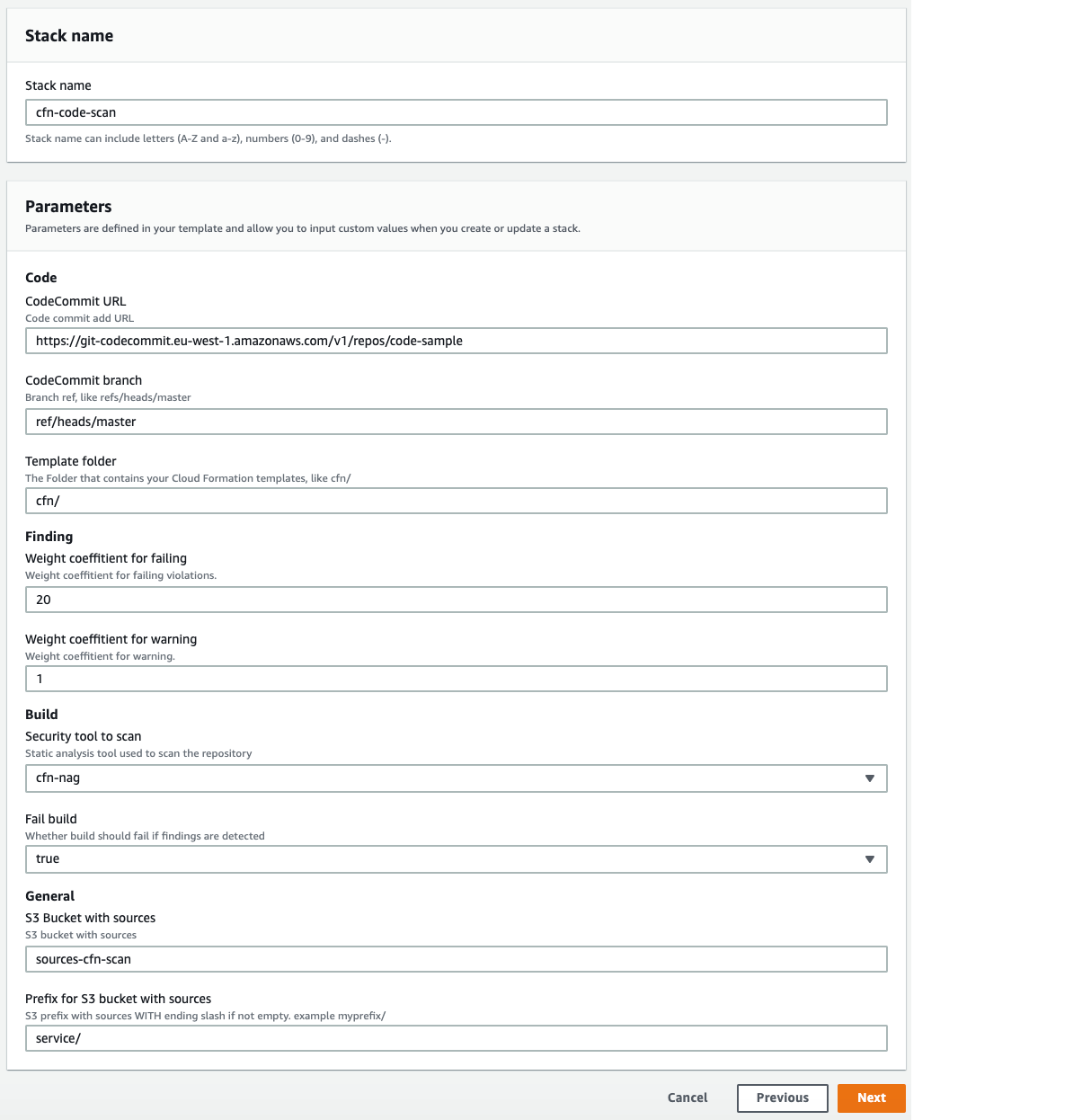
Figure 2: AWS CloudFormation stack
View the scan results
After you execute the CodeBuild project, you can view the results in three different ways depending on your preferences: CodeBuild report, Security Hub, or the original CFN-Nag or CFN-Guard report.
CodeBuild report
In the AWS Management Console, go to CodeBuild and choose Report Groups. You can find the report you are interested in under SecurityReports. Both failures and warnings are represented as failed tests and are prefixed with W(Warning) or F(Failure), respectively, as shown in Figure 3. Successful tests aren’t part of the report because they aren’t provided by CFN-Nag reports.
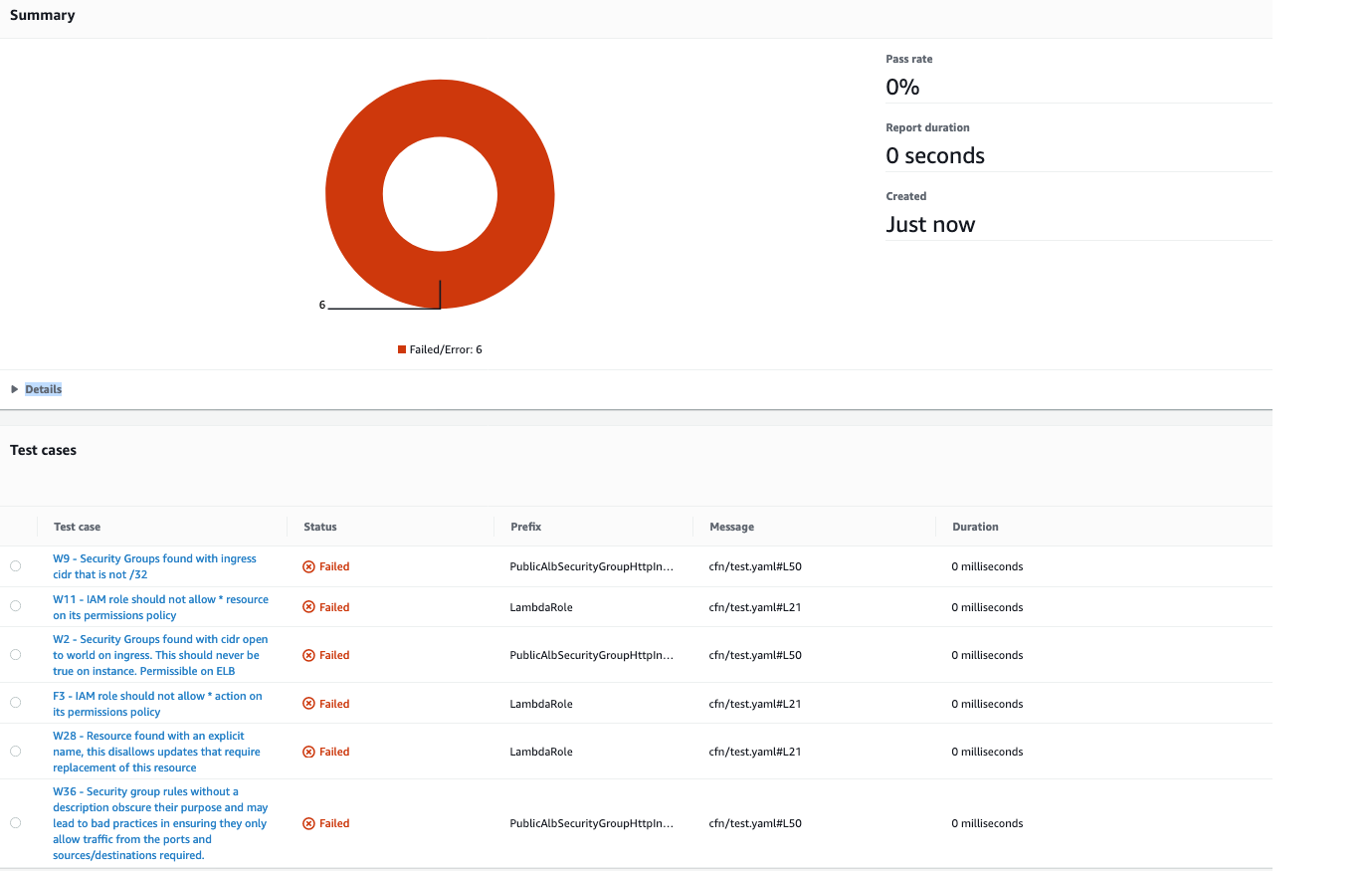
Figure 3: AWS CodeBuild report
In the CodeBuild navigation menu, under Report groups, you can see an aggregated view of all scans. There you can see a historical view of the pass rate of your tests, as shown in Figure 4.
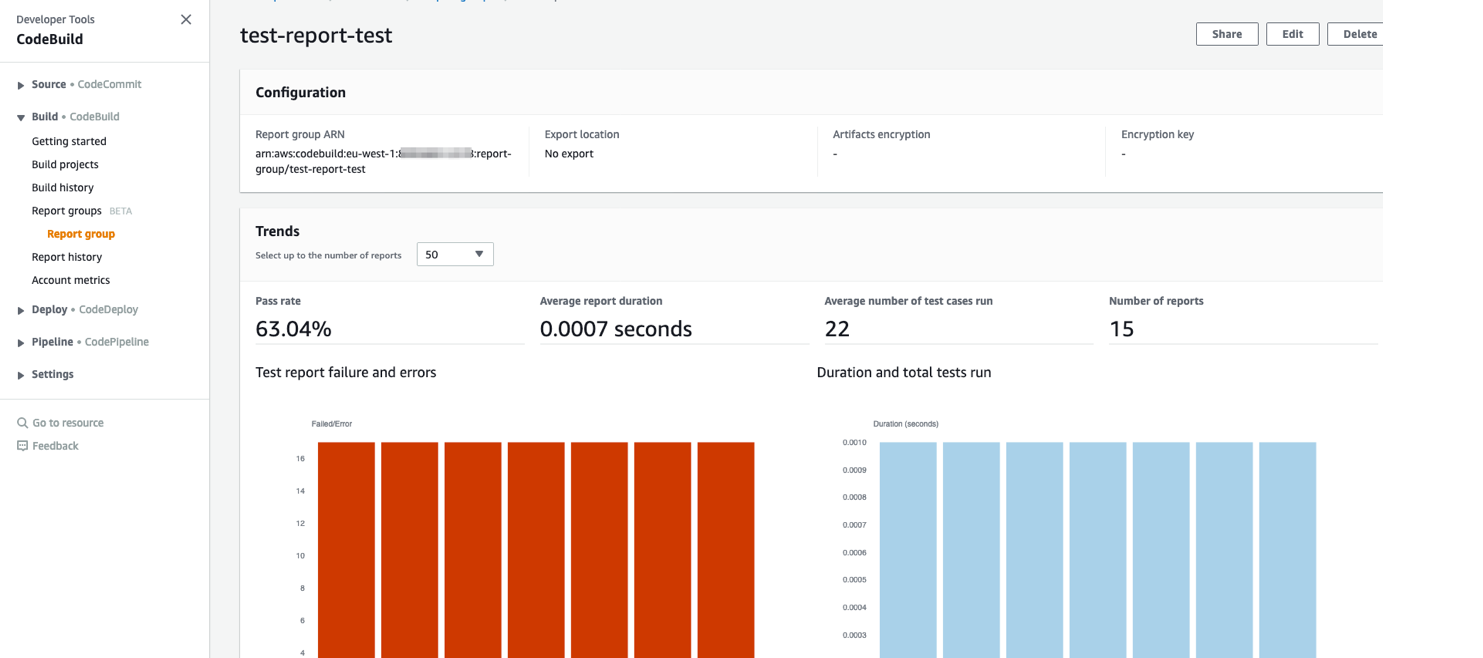
Figure 4: AWS CodeBuild Group
Security Hub findings
In the AWS Management Console, go to Security Hub and select the Findings view. The aggregated finding per branch has the title CFN scan repo:name:branch with Company Personal and Product Default. The name and branch are placeholders for the repo and branch name. There is one active finding per repo and branch. All previous reports for this repo and branch are suppressed, so that by default you see only the last ones. If necessary, you can see the previous reports by removing the selection filter in the Security Hub finding console. Figure 5 shows an example of the Security Hub findings.
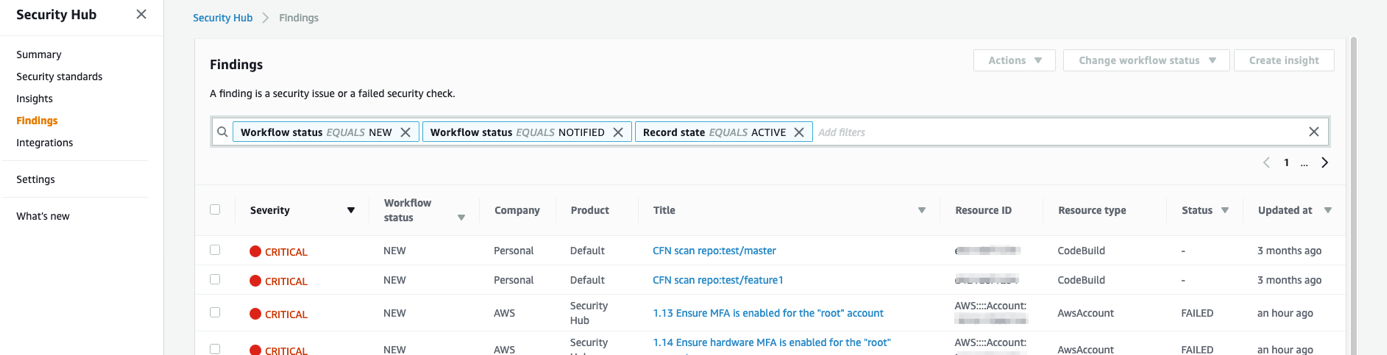
Figure 5: Security Hub findings
Original scan report
Lastly, you can find the original scan report in the S3 bucket aws-sec-build-reports-hash. You can also find a reference to this object in the associated Security Hub finding source URL. The S3 object key is constructed as follows.
where source_repository is the name of the repository, branch_short is the name of the branch, and createdAt is the report date.
The following screen capture shows a sample view of the content.
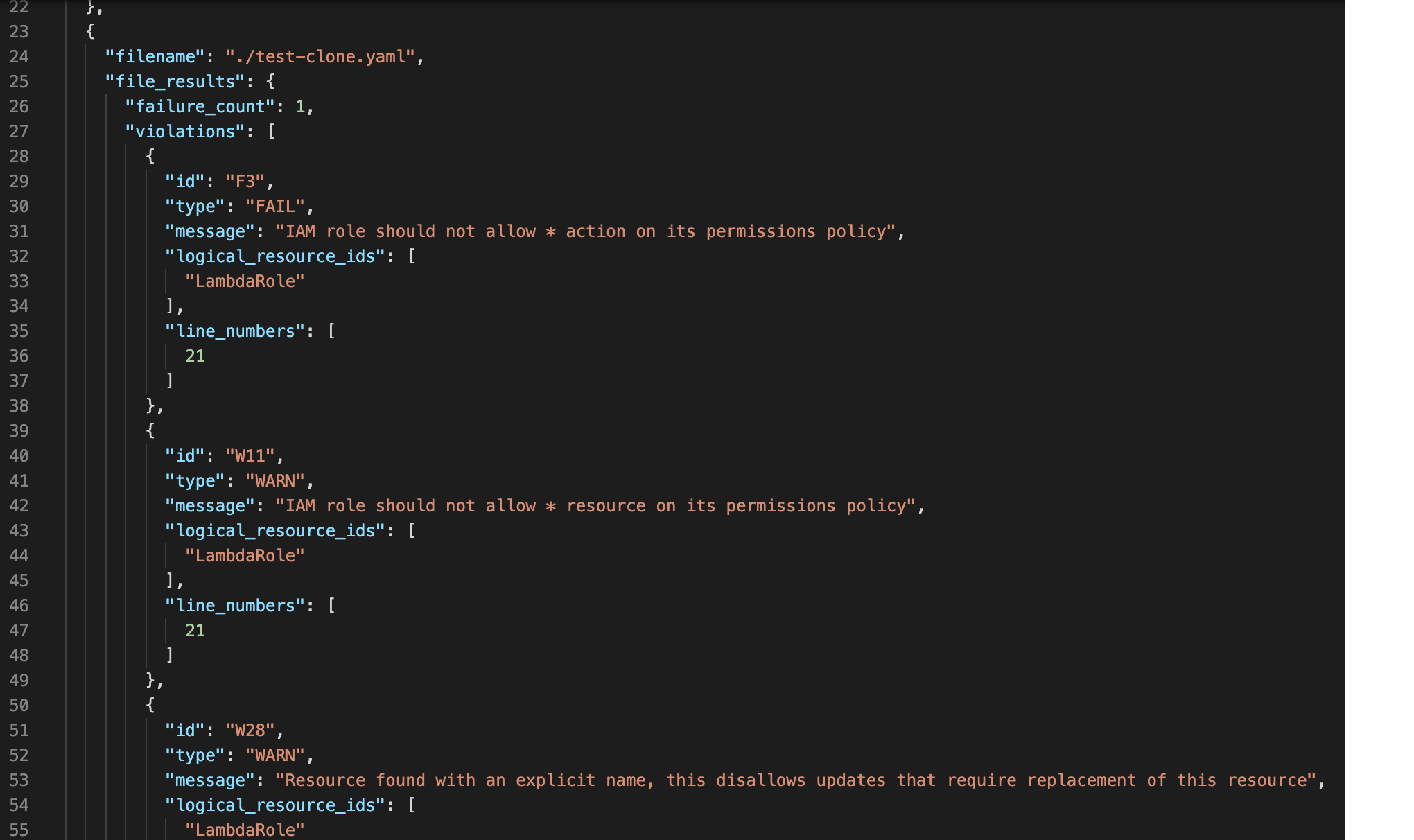
Figure 6: CFN_NAG report sample
Security Hub severity and weight coefficients
The Lambda function aggregates CFN-Nag findings to one Security Hub finding per branch and repo. We consider that in this way you get the best visibility without losing orientation in too many findings if you have a large code base.
The Security Hub finding severity is calculated as follows:
- CFN-Nag critical findings are weighted (multiplied) by 20 and the warnings by 1.
- The sum of all CFN-Nag findings multiplied by their weighted coefficient results in the severity of the Security Hub finding.
The severity label or normalized severity (from 0 to 100) (see AWS Security Finding Format (ASFF) for more information) is calculated from the summed severity. We implemented the following convention:
- If the severity is more than 100 points, the label is set as CRITICAL (100).
- If the severity is lower than 100, the normalized severity and label are mapped as described in AWS Security Finding Format (ASFF).
Your company might have a different way to calculate the severity. If you want to adjust the weight coefficients, change the stack parameter. If you want to adjust the mapping of the CFN-Nag findings to Security hub severity, then you’ll need to adapt the Lambda’s calculateSeverity Python function.
Using custom profiles and exceptions, and suppressing false positives
You can customize CFN-Nag to use a certain rule set by including the specific list of rules to apply (called a profile) within the repository. Customizing rule sets is useful because developers or applications might have different security considerations or risk profiles in specific applications. Additionally the operator might prefer to exclude rules that are prone to introducing false positives.
To add a custom profile, you can modify the cfn_nag_scan command specified in the CodeBuild buildspec.yml file. Use the –profile-path command argument to point to the file that contains the list of rules to use, as shown in the following code sample.
Where .cfn_nag.profile file contains one rule identifier per line:
You can find the full list of available rules using cfn_nag_rules command.
You can also choose instead to use a global deny list of rules, or directly suppress findings per resource by using Metadata tags in each AWS CloudFormation resource. For more information, see the CFN-Nag GitHub repository.
Integrating with AWS CloudFormation Guard
The integration with AWS CloudFormation Guard (CFN-Guard) follows the same architecture pattern as CFN-Nag. The ImportToSecurityHub Lambda function can process both CFN-Nag and CFN-Guard results to import to Security Hub and generate a CodeBuild report.
To deploy the CFN-Guard tool
- In the AWS Management Console, go to CloudFormation, and then choose Update the previous stack deployed.
- Choose Next, and then change the SecurityTool parameter to cfn-guard.
- Continue to navigate through the console and deploy the stack.
This creates a new buildspec.yml file that uses the cfn-guard command line interface (CLI) to scan all AWS CloudFormation templates in the source repository. The scans use an example rule set found in the CFN-Guard repository.
You can choose to generate the rule set for the AWS CloudFormation templates that are required by the scanning engine and add the rule set to your repository as described on the GitHub page for AWS CloudFormation Guard. The rule set must reflect your company security policy. This can be one set for all templates, or dependent on the security profile of the application.
You can use your own rule set by modifying the cfn-guard –rule_path parameter to point to a file from within your repository, as follows.
Troubleshooting
If the build report fails, you can find the CloudBuild run logs in the CodeBuild Build history. The build will fail if critical security findings are detected in the templates.
Additionally, the Lambda function execution logs can be found in the CloudWatch Log group aws/lambda/ImportToSecurityHub.
Summary
In this post, you learned how to scan the AWS CloudFormation templates for resources that are potentially insecure or not compliant to your company policy in a CodeBuild project, import the findings to Security Hub, and generate CodeBuild test reports. Integrating this solution to your pipelines can help multiple teams within your organization detect potential security risks in your infrastructure code before its deployed to your AWS environments. If you would like to extend the solution further and need support, contact AWS professional services or an Amazon Partner Network (APN) Partner. If you have technical questions, please use the AWS Security Hub or AWS CodeBuild forums.
If you have feedback about this post, submit comments in the Comments section below.
Want more AWS Security how-to content, news, and feature announcements? Follow us on Twitter.
