Post Syndicated from Dina Kozlov original https://blog.cloudflare.com/introducing-custom-hostname-analytics/
In our last blog, we talked about how Cloudflare can help SaaS providers extend the benefits of our network to their customers. Today, we’re excited to announce that SaaS providers will now be able to give their customers visibility into what happens to their traffic when the customer onboards onto the SaaS provider, and inherently, onto the Cloudflare network.
As a SaaS provider, you want to see the analytics about the traffic bound for your service. Use it to see the global distribution of your customers, or to measure the success of your business. In addition to that, you want to provide the same insights to your individual customers. That’s exactly what Custom Hostname Analytics allows you to do!
The SaaS Setup
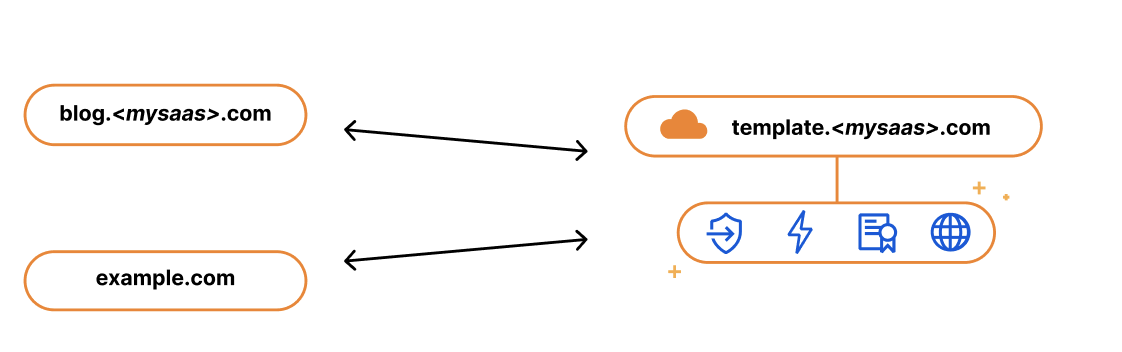
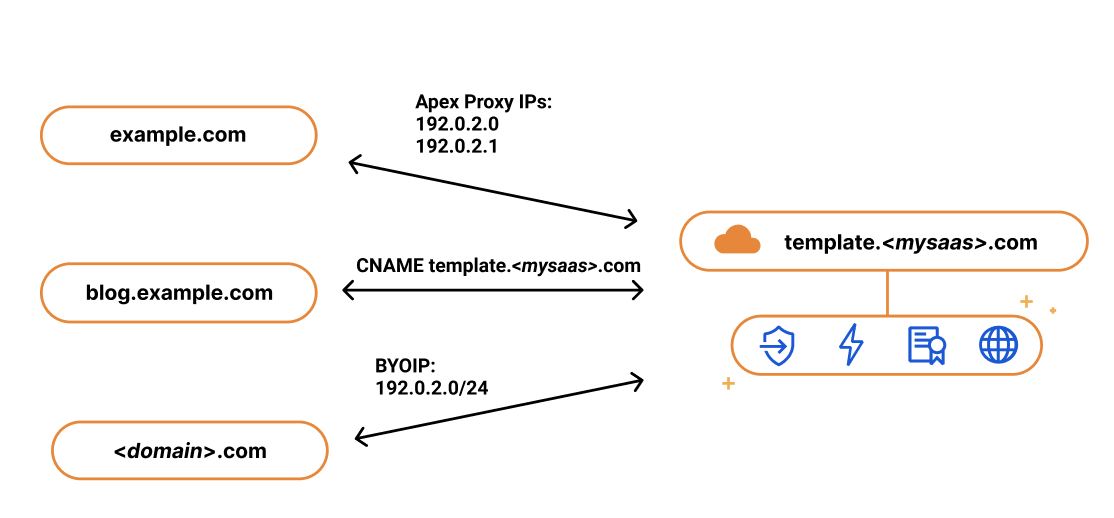
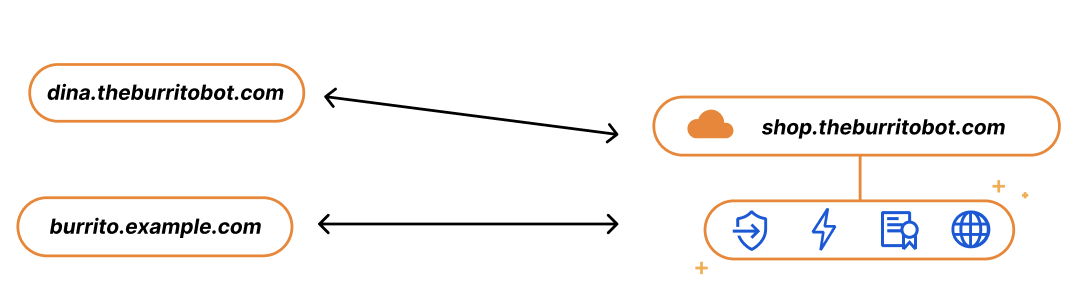
Imagine you run a SaaS service for burrito shops, called The Burrito Bot. You have your burrito service set up on shop.theburritobot.com and your customers can use your service either through a subdomain of your zone, i.e. dina.theburritobot.com, or through their own website e.g. burrito.example.com.
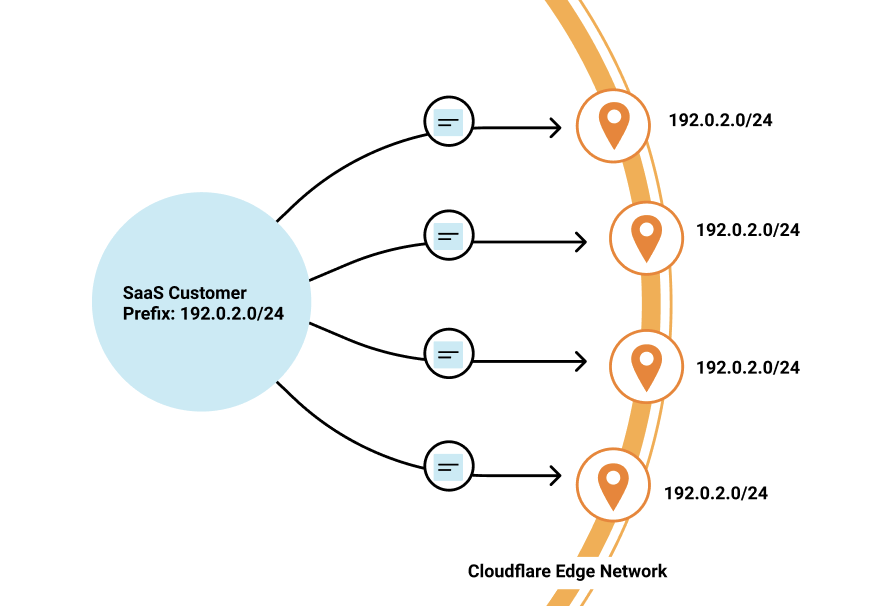
When customers onboard to your burrito service, they become fully reliant on you to provide their website with the fastest load time, the best protection, and the highest uptime. Similarly, when SaaS providers onboard to Cloudflare, they expect the same — and we deliver. The easiest way that we show this to our customers is through analytics. We put ourselves in front of their website, blocking attacks and accelerating traffic. Then, through dashboards like Bot Analytics or Cache Analytics, we show insights about bad bots and low latency in real time.
In the same way that it’s our responsibility to show SaaS providers all the benefits we’re providing for their traffic, we think SaaS providers should be able to provide the same information to their customers.
Analytics for the SaaS Provider
As a SaaS provider, your infrastructure is your customers’ infrastructure, so you need to have visibility into the traffic of your service to be able to make business decisions. Being able to answer questions like “how many total requests am I getting on my service?”, “Which customer is transferring the most data?”, or “How many global customers do I have?” can help you figure out how to bill your customers or how and where to scale your infrastructure. With custom hostname analytics, you can get the full view of how customers are using your services through our Dashboard or API.
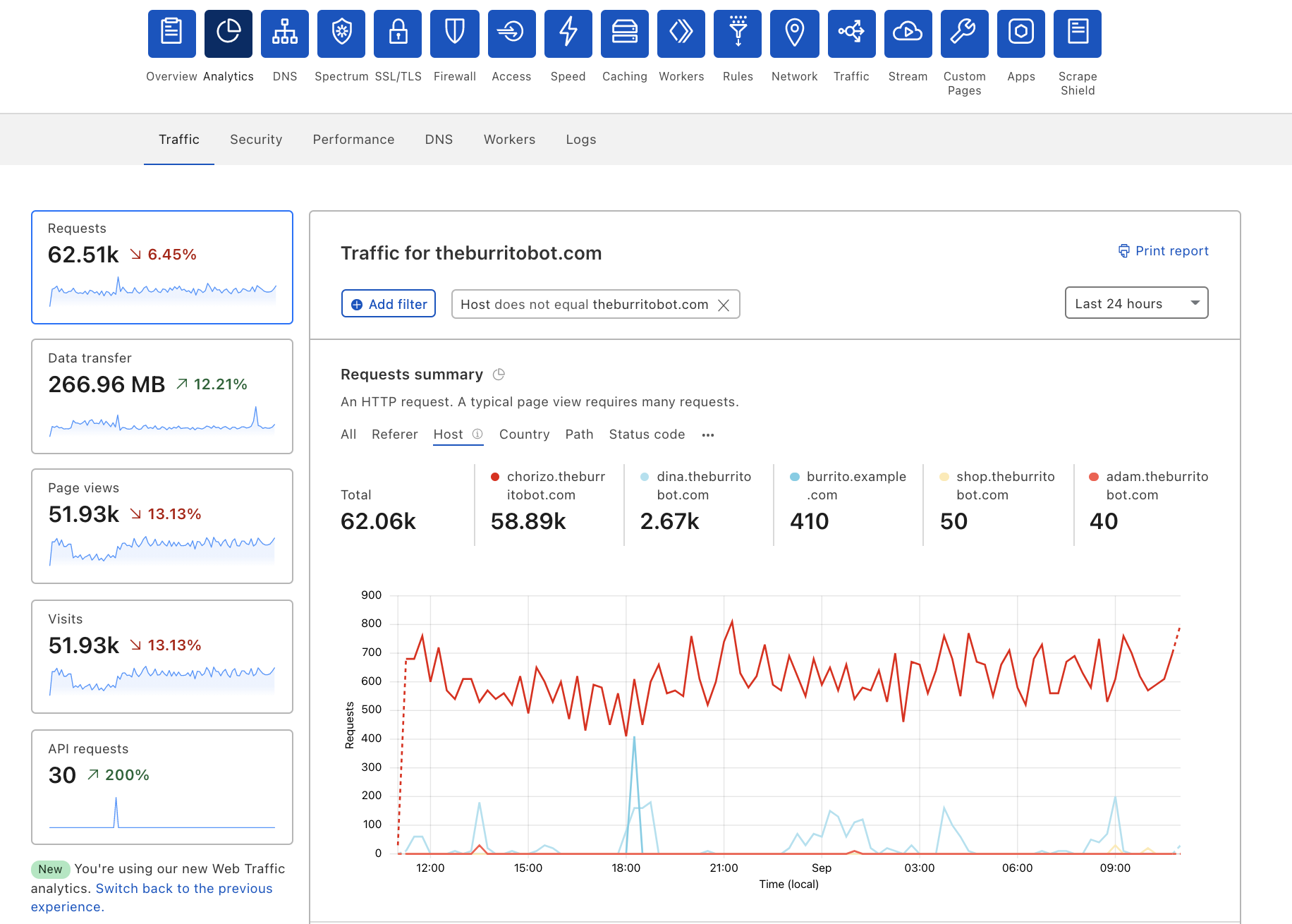
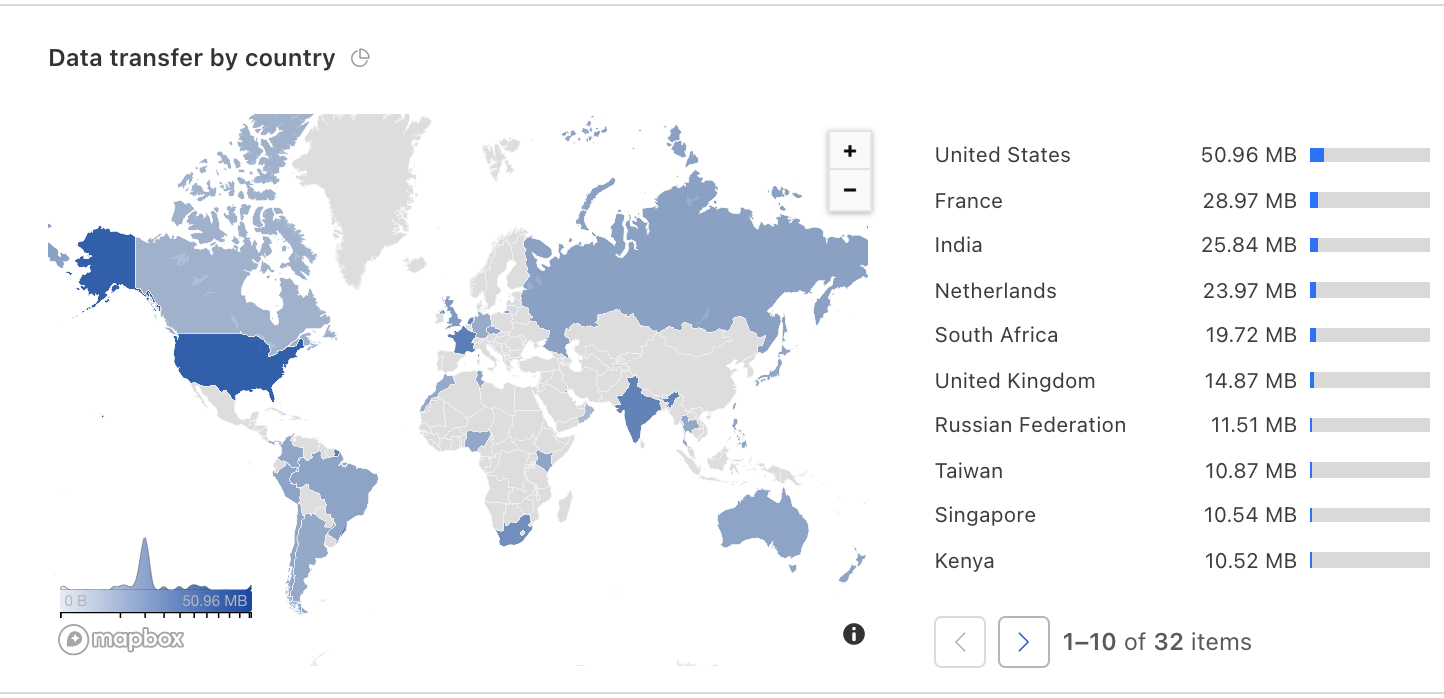
Here you can see that one custom hostname is using significantly more data transfer than the others, and you might want to charge them accordingly. Alternatively, you can look at the geographic breakdown of your customers. If it looks like burrito shops are growing in Europe, you might want to think about expanding your business there and adding new origins to serve that traffic.
Analytics for your customers
In the same way that you want to see the breakdown of traffic bound for your service, your customers want to see the same information about their website. They want to know how many page views they’re getting, if they’re having any bots ordering fake burritos, or how fast their website is. With custom hostname analytics, we’re giving SaaS providers the resources they need to present this data to their customers.
Build your own dashboards!
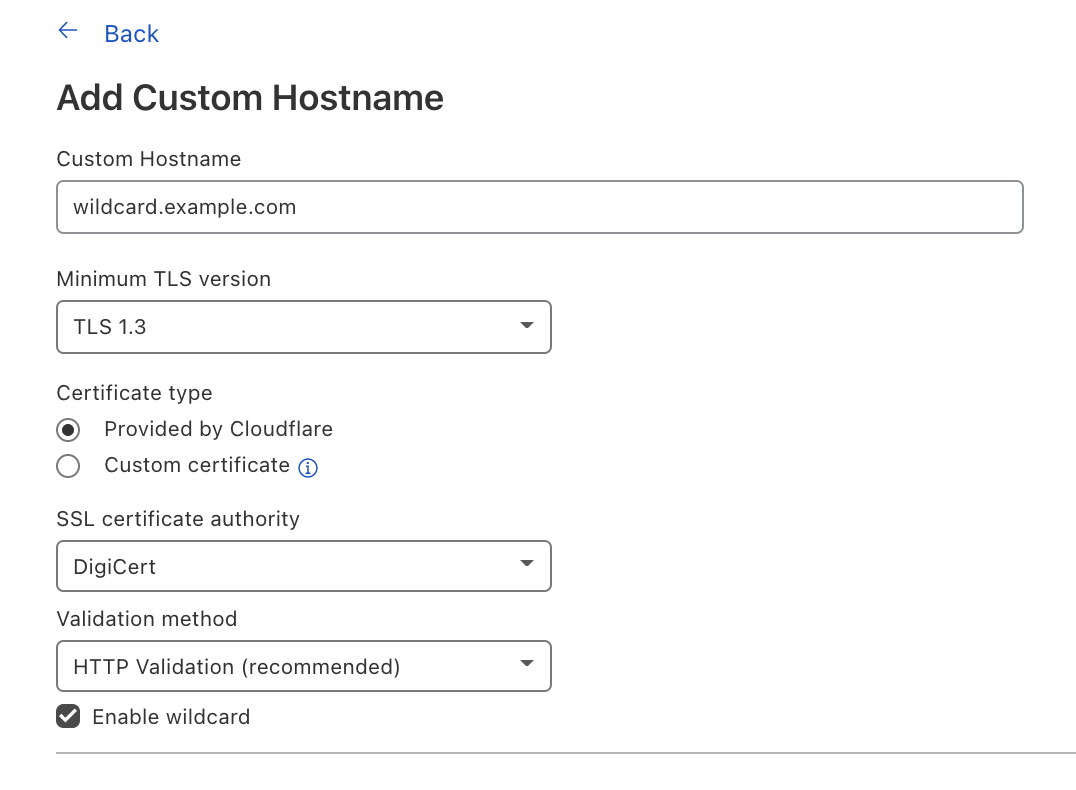
The most powerful way to use our technology would be to use our GraphQL Analytics API with the clientRequestHTTPHost field to get analytics for each of your customers’ domains. This will allow you to build your own dashboards and display the information that you feel is important to your customers.
Show your customer the bad traffic you’re blocking
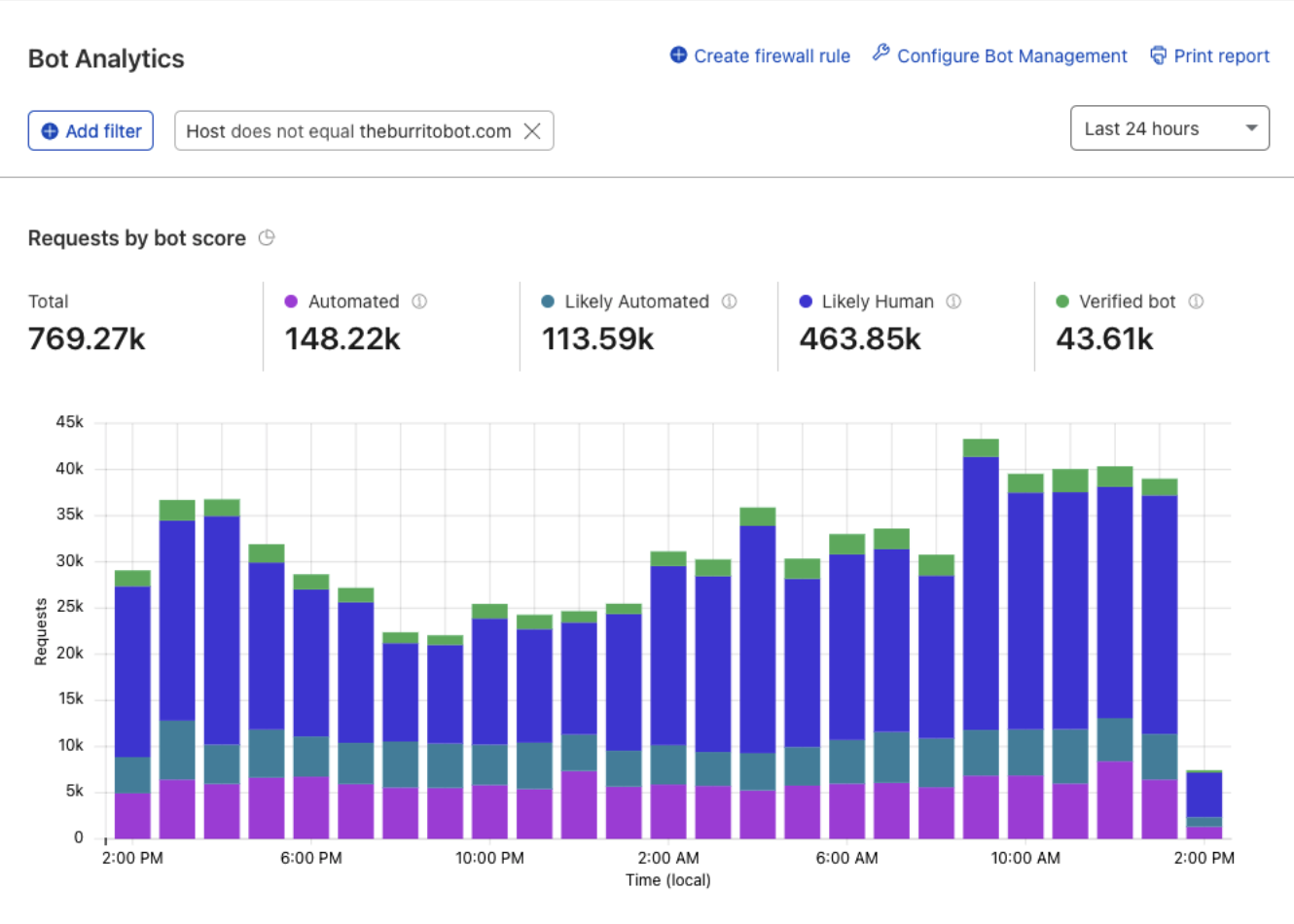
Let’s say you’re using Cloudflare for SaaS and are extending Bot Management to your thousands of customers — wouldn’t you want to show them how much malicious traffic you’re keeping away from them?
You can do that!
One way to see the analytics for your custom hostnames is in the Dashboard. You can either look up the total requests for an individual hostname or — by adding the filter Host does not equal theburritobot.com — total requests for all your custom hostnames.
What else can I see?
You can use Custom Hostname analytics for just about everything that you can see for your own domain. From your firewall to bot protection, you can use any dataset with a clientRequestHTTPHost field for your custom hostname analytics.
Interested in trying this out?
Sign up for our Cloudflare for SaaS Beta. We are continuing to accept applicants and are excited to announce that General Availability is not too far away.
Share what you build
We’d love to see what kind of dashboards you build with our Analytics API. If you want to share what you’ve built, tweet at @Cloudflare and send us a screenshot!