Post Syndicated from VassilKendov original http://kendov.com/bank-crises/
 Пиша тази статия поради многото запитвания на познати как да постъпят в конкретната ситуация с личните си финанси. Не мога да отделя на всички време по телефона, затова ще обясня на разбираем език какво се случва с банките, а по-надолу ще публикувам форма със заявка, за тези които искат да направим конкретна среща и да получат съвет или мнение, съобразени с техните лични финансови намерения.
Пиша тази статия поради многото запитвания на познати как да постъпят в конкретната ситуация с личните си финанси. Не мога да отделя на всички време по телефона, затова ще обясня на разбираем език какво се случва с банките, а по-надолу ще публикувам форма със заявка, за тези които искат да направим конкретна среща и да получат съвет или мнение, съобразени с техните лични финансови намерения.
За да разберем проблема и как ще ни засегне е нужно да познаваме малко от малко основните макроикономически принципи и как работи финансовата система.
Буквално в няколко реда ще обясня на достъпен език, някои от основните пазарни принципи, имащи отношение към сегашната ситуация.
Няй-силният лост за управлението на една икономика е ПАРИЧНАТА МАСА В ОБРАЩЕНИЕ! Тоест парите с които ние боравим. Трябва да знаете, че няма по-силен лост за влияние върху икономиката от този. Когато се развиваш и растеш, печаташ пари за да обслужиш или инициираш този ръст. Когато се появи инфлация от многото пазаруване, вдигаш лихвите за да вкараш парите в банките (на депозити или в ценни книги) и те да не участват в оборота. По този начин също така вдигаш стойността на парите и тушираш инфлацията.
За актуални финансови новини можете да използвате Telegram канала Kendov.com
Когато банките имат излишни пари и достатъчно депозити, с част от тях те купуват ценни книги. Много често това са държавни облигации. Тук ключовия момент е „ЧАСТ ОТ ТЯХ”. Никоя банка няма да допусне портфейла и да се състои само и единствено от ДЦК (държавни ценни книжа). Счита се че ДЦК са безрискови, понеже държавата не може да фалира. Най-малкото може винаги да напечата пари и да покрие задълженията си с цената на инфлация. Затова и инфлацията често се използва за „ликвидиране” на задълженията. Помните голямата инфлация в България през 90-те, когато с доживотните си спестявания си купихте един чифт дънки или обратното – когато с една заплата си погасихте жилищния кредит за следващите 15 години?
Това е един много опростен модел, но трябва да го споменем, за да сме сигурни, че ще разберем важността на случващото се в момента и връзката му с нашите лични финанси.
Какво се случи на практика
От 2008 година насам, централните банки по света пуснаха в обращение БЕЗПРЕЦЕДЕНТНО количество пари. Някой дори заговориха за „хеликоптерни пари”, но сега няма да се отклонявам за да обяснявам какво е това (в Гугъл има достатъчно информация).
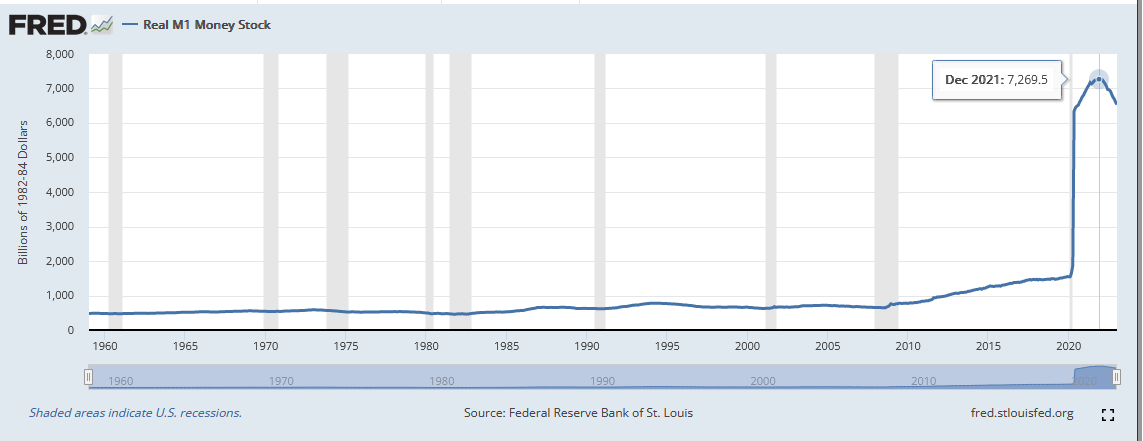
На тази графика Федералния резерв на САЩ са дали как се движи през годините паричната маса в обращение М1 (парите в обращение + кредитните карти+краткосрочните депозити).

От кризата през 2008 виждате, че тази маса нараства. През 2020 има една промяна в начина на отчитане и затова графиката изглежда така. Но като цяло виждате, че преди САЩ да започнат да вдигат лихвите 2021-ва, паричната маса в обращение расте. И то расте добре. Мисля, че няма смисъл да се чудим откъде дойде инфлацията. Само да отбележа, че у нас дойде главно през валутния борд и свързаноста на лева с еврото. Тоест дойде от инфлацията в ЕС, където от 2008 насам също се пуснаха в обращение безпрецедентно количество пари.
През всичките тези годни ливите бяха на исторически ниски нива. EURIBOR-a дори беше отрицателен. Имаше момент в който Германия пусна ДЦК с отрицателна доходност и те бяха изкупени. Тоест като ги купуваш си наясно, че ще си на загуба, но го правиш. Не ме питайте защо, и аз не знам но го правеха.
Като резултат банките се „набълбукаха” с такива дългосрочни и бездоходни ДЦК, но лихвите започнаха да се качват. Както в САЩ, така и в Европа. Този четвъртък ЕЦБ дори вдигна лихвата с още 0.5%.
По този начин купените вече ДЦК започват да губят стойност, защото новите са с 3-4% доходност, а старите с 0-0,5% доходност и то ако ги държиш до падежа. Но пък са част от активите на банката, за съжаление вече с по-ниска цена, защото никой не иска да ги купи. Тоест би ги купил с голяма отстъпка и това вече е загуба за банката.
За срещa моля използвайте посочената форма.
[contact-form-7]
За вида и качеството на активите има изисквания от страна на централните банки и точно в този момент те поискаха от търговските банки да направят преоценка на активите си, по новите пазарни цени.
Както сами се сещате, това доведе до отчитане на загуби и изисквания тези активи да бъдат заменени с други по-стойностни, за които се изискваше събиране на капитал от фондовите борси.
Това добре, но вие бихте ли си купили облигации или акции на губещо предприятие, защото след преоценката банките вече бяха на загуба?
Това комбинирано с действията на директорите на банките, които побързаха да продадат акциите си и да изтеглят депозитите си, доведе до така наречения “bank run” – всички теглят авоарите си от тази банка и продават ценните си книги.
Същото става и в Европа, но по традиция малко закъснение.
Горните са фактите, но интерпретацията им е важна за да сформирате очакванията си.
Доколкото сме в пазарна икономика, фалита би следвало да е нещо нормално. Виждаме обаче, че някои не е приемливо да фалират и затова им помагаме. На други обаче не.
В случая със SVB Bank, Федералния резерв на САЩ взе решение да гарантира депозитите без значение от размера им, защото това са парите на IТ компаниите. Как става това? С пускане на пазара на още пари.
Днес обявиха, че ще бъде спасена и другата закъсала регионална банка – First Republic. Тя щяла да бъде спасена чрез предоставянето на депозити от големите банки, членове на федералния резерв на САЩ.
За Credit Siusse вече знаете, че също ще бъде спасена с помощ от централната банка на Швейцария в размер на 50 млрд франка. Смятайте го като инжектиране на още 50 млрд в обращение. И инфлацията е гарантирана!

Без значение как ще бъдат спасени банките, това ще доведе до увеличение на паричната маса в обращение и то във времена на достатъчно голяма инфлация (около 9.2% средно за ЕС). Но и това не е най-голямият проблем.
Спасявайки големите банки, се случват няколко социални феномена
– Вече не е пазарно да фалираш! Влизаме в комунизма, където предприятията работеха на загуба и накрая държавата покриваше загубата. В сегашния социален строй обаче, загубите в крайна сметка ще се покрият от хората. А какво друго е инфлацията?
10% инфлация си е близо 10% спад в доходите или 10% данък. Разглеждайте го както ви харесва, но в крайна сметка плащат хората.
– Как очакваме малките да пораснат, ако всеки път спасяваме неефективните големи, за сметка на малките по-прогресивни? Представете си как това влияе на мотивацията на бизнеса. Посланието е – „Колкото и да работиш, голям няма да станеш ако не ти позволим.”
Най-големия проблем от финансова гледна точка е поставянето в подчинение на получилите помощ финансови институции. Разбрате, че няма как просто да им дадат парите, без да има условия. Но всяко условие си е вид подчинение.
Интересно ми е дали и други банки биха „симулирали” фалит за да получат и те помощи.
Наивно е да си мислим, че централните банки не са знаели какво ще се случи, ако вдигнат лихвите и накарат търговските банки да преоценят активите си. Те много добре знаят какъв е портфейла на всяка подотчетна банка и как би повлияло това.
Въпросът е защо го направиха и защо сега?

Лично моето очакване е за още по-висока инфлация и лихви, което да доведе до условия за въвеждане на CBDCs – дигитални пари. Но това е друга тема и за последствията от тяхното въвеждане тепърва ще четете, а аз тепърва ще пиша.
През това време е редно всеки да помисли за спестяванията си и въобще за личните си финанси. Ще помогна с каквото мога, но всеки сам трябва да вземе решение какво да прави в тези условия. В тази ситуация няма после. После е инфлацията!
Ако статията Ви е харесала, помогнете да развием този блог като го споделите на стената си във ФБ. Благодаря Ви предварително.
Можете да се включите в дискусията в Telegram канала Kendov.com
За контакт
[contact-form-7]
The post Какво се случва с банките в момента, преведено на достъпен език appeared first on Kendov.com.
 Пиша тази статия поради многото запитвания на познати как да постъпят в конкретната ситуация с личните си финанси. Не мога да отделя на всички време по телефона, затова ще обясня на разбираем език какво се случва с банките, а по-надолу ще публикувам форма със заявка, за тези които искат да направим конкретна среща и да получат съвет или мнение, съобразени с техните лични финансови намерения.
Пиша тази статия поради многото запитвания на познати как да постъпят в конкретната ситуация с личните си финанси. Не мога да отделя на всички време по телефона, затова ще обясня на разбираем език какво се случва с банките, а по-надолу ще публикувам форма със заявка, за тези които искат да направим конкретна среща и да получат съвет или мнение, съобразени с техните лични финансови намерения.