Post Syndicated from Adam Cerini original https://aws.amazon.com/blogs/security/automatically-updating-aws-waf-rule-in-real-time-using-amazon-eventbridge/
In this post, I demonstrate a method for collecting and sharing threat intelligence between Amazon Web Services (AWS) accounts by using AWS WAF, Amazon Kinesis Data Analytics, and Amazon EventBridge. AWS WAF helps protect against common web exploits and gives you control over which traffic can reach your application.
Attempted exploitation blocked by AWS WAF provides a data source on potential attackers that can be shared proactively across AWS accounts. This solution can be an effective way to block traffic known to be malicious across accounts and public endpoints. AWS WAF managed rules provide an easy way to mitigate and record the details of common web exploit attempts. This solution will use the Admin protection managed rule for demonstration purposes.
In this post you will see references to the Sender account and the Receiver account. There is only one receiver in this example, but the receiving process can be duplicated multiple times across multiple accounts. This post walks through how to set up the solution. You’ll notice there is also an AWS CloudFormation template that makes it easy to test the solution in your own AWS account. The diagram in figure 1 illustrates how this architecture fits together at a high level.
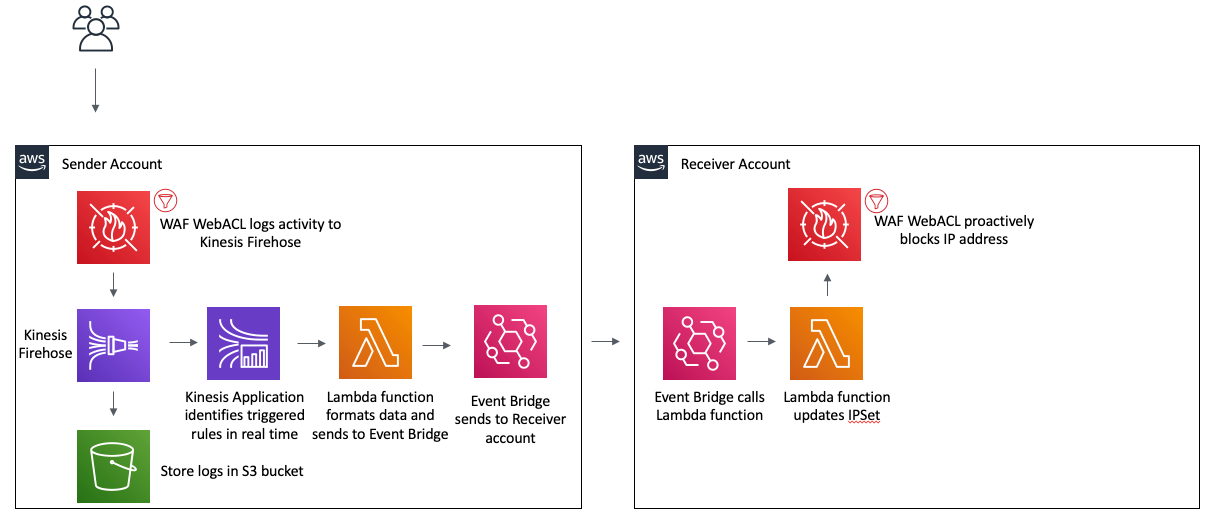
Figure 1: Architecture diagram showing the activity flow of traffic blocked on the Sender AWS WAF
Prerequisites
You should know how to do the following tasks:
- Create an AWS WAF web ACL and associate it to a resource. To understand this process in more detail, see the AWS WAF documentation.
- Create an Amazon Kinesis Data Firehose delivery stream. To understand this process in more detail, see the Kinesis Data Firehose documentation.
- Create an Amazon EventBridge event bus. To understand this process in more detail, see the EventBridge documentation.
- Create a Kinesis Data Analytics application. To understand this process in more detail, see the Kinesis Data Analytics documentation.
- Create and manage AWS Identity and Access Management (IAM) roles. To understand this process in more detail, see the IAM documentation.
Extracting threat intelligence
AWS WAF logs using a Kinesis Data Firehose delivery stream. This allows you to not only log to a destination S3 bucket, but also act on the stream in real time using a Kinesis Data Analytics Application. The following SQL code demonstrates how to extract any unique IP addresses that have been blocked by AWS WAF. While this example returns all blocked IPs, more complex SQL could be used for a more granular result. The full list of log fields is included in the documentation.
Proactively blocking unwanted traffic
After extracting the IP addresses involved in the abnormal traffic, you will want to proactively block those IPs on your other web facing resources. You can accomplish this in a scalable way using Amazon EventBridge. After the Kinesis Application extracts the IP address, it will use an AWS Lambda function to call PutEvents on an EventBridge event bus. This process will create the event pattern, which is used to determine when to trigger an event bus rule. This example uses a simple pattern, which acts on any event with a source of “custom.waflogs” as shown in Figure 2. A more complex pattern could be used to for finer grain control of when a rule triggers.
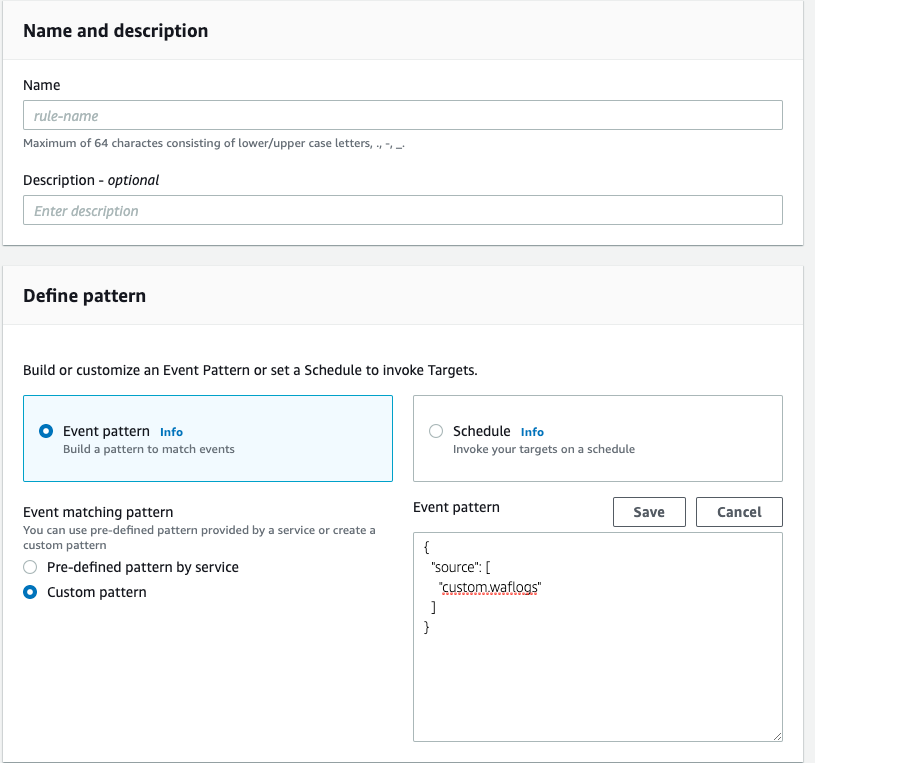
Figure 2: EventBridge Rule creation
Once the event reaches the event bus, the rule will forward the event to an event bus in “Receiver” account, where a second rule will trigger to call a Lambda function to update a WAF IPSet. A Web ACL rule is used to block all traffic sourcing from an IP address contained in the IPSet.
Test the solution by using AWS CloudFormation
Now that you’ve walked through the design of this solution, you can follow these instructions to test it in your own AWS account by using CloudFormation stacks.
To deploy using CloudFormation
- Launch the stack to provision resources in the Receiver account.
- Provide the account ID of the Sender account. This will correctly configure the permissions for the EventBridge event bus.
- Wait for the stack to complete, and then capture the event bus ARN from the output tab.
This stack creates the following resources:
- An AWS WAF v2 web ACL
- An IPSet which will be used to contain the IP addresses to block
- An AWS WAF rule that will block IP addresses contained in the IPSet
- A Lambda function to update the IPSet
- An IAM policy and execution role for the Lambda function
- An event bus
- An event bus rule that will trigger the Lambda function
- Switch to the Sender account. This should be the account you used in step 2 of this procedure.
- Provide the ARN of the event bus that was captured in step 3. This stack will provision the following resources in your account:
- A virtual private cloud (VPC) with public and private subnets
- Route tables for the VPC resources
- An Application Load Balancer (ALB) with a fixed response rule
- A security group that allows ingress traffic on port 80 to the ALB
- A web ACL with the AWS Managed Rule for Admin Protection enabled
- An S3 bucket for AWS WAF logs
- A Kinesis Data Firehose delivery stream
- A Kinesis Data Analytics application
- An EventBridge event bus
- An event bus rule
- A Lambda function to send information to the Receiver account event bus
- A custom CloudFormation resource which enables WAF logging and starts the Kinesis Application
- An IAM policy and execution role that allows a Lamba function to put events into the event bus
- An IAM policy and role to allow the custom CloudFormation resource to enable WAF logging and start the Kinesis Application
- An IAM policy and role that allows the Kinesis Firehose to put logs into S3
- An IAM policy that allows the WAF Web ACL to put records into the Firehose
- An IAM policy and role that allows the Kinesis Application to invoke a Lambda function and log to CloudWatch
- An IAM policy and role that allows the “Sender” account to put events in the “Receiver” event bus
After the CloudFormation stack completes, you should test your environment. To test the solution, check the output tab for the DNS name of the Application Load Balancer and run the following command:
curl ALBDNSname/admin
You should be able to check the Receiver account’s AWS WAF IPSet named WAFBlockIPset and find your IP.
Conclusion
This example is intentionally simple to clearly demonstrate how each component works. You can take these principles and apply them to your own environment. Layering the Amazon managed rules with your own custom rules is the best way to get started with AWS WAF. This example shows how you can use automation to update your WAF rules without needing to rely on humans. A more complete solution would source log data from each Web ACL and update an active IP Set in each account to protect all resources. As seen in Figure 3, a more complete implementation would send all logs in a region to a centralized Kinesis Firehose to be processed by the Kinesis Analytics Application, EventBridge would be used to update a local IPset as well as forward the event to other accounts event buses for processing.
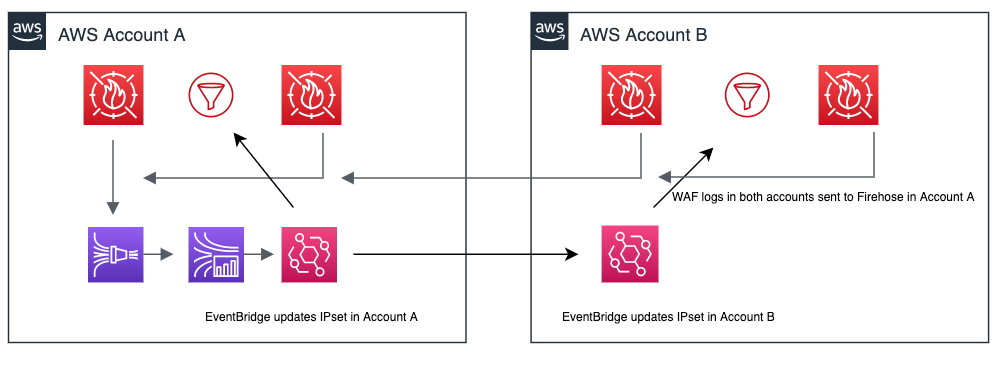
Figure 3: Updating across accounts
You can also add additional targets to the event bus to do things such as send to a Simple Notification Service topic for notifications, or run additional automation. To learn more about AWS WAF web ACLs, visit the AWS WAF Developer Guide. Using Amazon EventBridge opens up the possibility to send events to partner integrations. Customers or APN Partners like PagerDuty or Zendesk can enrich this solution by taking actions such as automatically opening a ticket or starting an incident. To learn more about the power of Amazon EventBridge, see the EventBridge User Guide.
If you have feedback about this post, submit comments in the Comments section below. If you have questions about this post, start a new thread on the AWS WAF forum or contact AWS Support.
Want more AWS Security how-to content, news, and feature announcements? Follow us on Twitter.