Post Syndicated from James Beswick original https://aws.amazon.com/blogs/compute/building-resilient-no-code-serverless-patterns-by-combining-messaging-services/
In “Choosing between messaging services for serverless applications”, I explain the features and differences between the core AWS messaging services. Amazon SQS, Amazon SNS, and Amazon EventBridge provide queues, publish/subscribe, and event bus functionality for your applications. Individually, these are robust, scalable services that are fundamental building blocks of serverless architectures.
However, you can also combine these services to solve specific challenges in distributed architectures. By doing this, you can use specific features of each service to build sophisticated patterns with little code. These combinations can make your applications more resilient and scalable, and reduce the amount of custom logic and architecture in your workload.
In this blog post, I highlight several important patterns for serverless developers. I also show how you use and deploy these integrations with the AWS Serverless Application Model (AWS SAM).
Examples in this post refer to code that can be downloaded from this GitHub repo. The README.md file explains how to deploy and run each example.
SNS to SQS: Adding resilience and throttling to message throughput
SNS has a robust retry policy that results in up to 100,010 delivery attempts over 23 days. If a downstream service is unavailable, it may be overwhelmed by retries when it comes back online. You can solve this issue by adding an SQS queue.

Adding an SQS queue between the SNS topic and its subscriber has two benefits. First, it adds resilience to message delivery, since the messages are durably stored in a queue. Second, it throttles the rate of messages to the consumer, helping smooth out traffic bursts caused by the service catching up with missed messages.
To build this in an AWS SAM template, you first define the two resources, and the SNS subscription:
MySqsQueue:
Type: AWS::SQS::Queue
MySnsTopic:
Type: AWS::SNS::Topic
Properties:
Subscription:
- Protocol: sqs
Endpoint: !GetAtt MySqsQueue.Arn
Finally, you provide permission to the SNS topic to publish to the queue, using the AWS::SQS::QueuePolicy resource:
SnsToSqsPolicy:
Type: AWS::SQS::QueuePolicy
Properties:
PolicyDocument:
Version: "2012-10-17"
Statement:
- Sid: "Allow SNS publish to SQS"
Effect: Allow
Principal: "*"
Resource: !GetAtt MySqsQueue.Arn
Action: SQS:SendMessage
Condition:
ArnEquals:
aws:SourceArn: !Ref MySnsTopic
Queues:
- Ref: MySqsQueue
To test this, you can publish a message to the SNS topic and then inspect the SQS queue length using the AWS CLI:
aws sns publish --topic-arn "arn:aws:sns:us-east-1:123456789012:sns-sqs-MySnsTopic-ABC123ABC" --message "Test message"
aws sqs get-queue-attributes --queue-url "https://sqs.us-east-1.amazonaws.com/123456789012/sns-sqs-MySqsQueue- ABC123ABC " --attribute-names ApproximateNumberOfMessages
This results in the following output:

Another usage of this pattern is when you want to filter messages in architectures using an SQS queue. By placing the SNS topic in front of the queue, you can use the message filtering capabilities of SNS. This ensures that only the messages you need are published to the queue. To use message filtering in AWS SAM, use the AWS:SNS:Subcription resource:
QueueSubcription:
Type: 'AWS::SNS::Subscription'
Properties:
TopicArn: !Ref MySnsTopic
Endpoint: !GetAtt MySqsQueue.Arn
Protocol: sqs
FilterPolicy:
type:
- orders
- payments
RawMessageDelivery: 'true'
EventBridge to SNS: combining features of both services
Both SNS and EventBridge have different characteristics in terms of targets, and integration with broader features. This table compares the major differences between the two services:
|
Amazon SNS |
Amazon EventBridge |
| Number of targets |
10 million (soft) |
5 |
| Limits |
100,000 topics. 12,500,000 subscriptions per topic. |
100 event buses. 300 rules per event bus. |
| Input transformation |
No |
Yes – see details. |
| Message filtering |
Yes – see details. |
Yes, including IP address matching – see details. |
| Format |
Raw or JSON |
JSON |
| Receive events from AWS CloudTrail |
No |
Yes |
| Targets |
HTTP(S), SMS, SNS Mobile Push, Email/Email-JSON, SQS, Lambda functions |
15 targets including AWS Lambda, Amazon SQS, Amazon SNS, AWS Step Functions, Amazon Kinesis Data Streams, Amazon Kinesis Data Firehose. |
| SaaS integration |
No |
Yes – see integration partners. |
| Schema Registry integration |
No |
Yes – see details. |
| Dead-letter queues supported |
Yes |
No |
| Public visibility |
Can create public topics |
Cannot create public buses |
| Cross-Region |
You can subscribe your AWS Lambda functions to an Amazon SNS topic in any Region. |
Targets must be same Region. You can publish across Region to another event bus. |
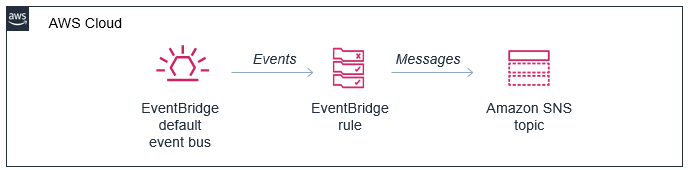
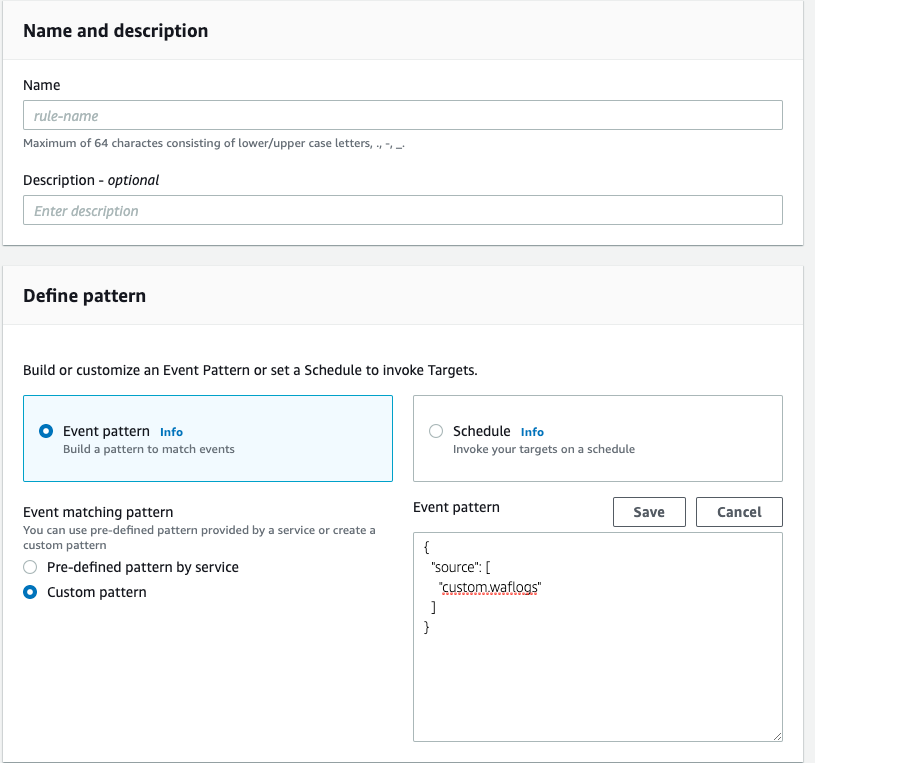
In this pattern, you configure an SNS topic as a target of an EventBridge rule:

In the AWS SAM template, you declare the resources in the preceding diagram as follows:
Resources:
MySnsTopic:
Type: AWS::SNS::Topic
EventRule:
Type: AWS::Events::Rule
Properties:
Description: "EventRule"
EventPattern:
account:
- !Sub '${AWS::AccountId}'
source:
- "demo.cli"
Targets:
- Arn: !Ref MySnsTopic
Id: "SNStopic"
The default bus already exists in every AWS account, so there is no need to declare it. For the event bus to publish matching events to the SNS topic, you define permissions using the AWS::SNS::TopicPolicy resource:
EventBridgeToToSnsPolicy:
Type: AWS::SNS::TopicPolicy
Properties:
PolicyDocument:
Statement:
- Effect: Allow
Principal:
Service: events.amazonaws.com
Action: sns:Publish
Resource: !Ref MySnsTopic
Topics:
- !Ref MySnsTopic
EventBridge has a limit of five targets per rule. In cases where you must send events to hundreds or thousands of targets, publishing to SNS first and then subscribing those targets to the topic works around this limit. Both services have different targets, and this pattern allows you to deliver EventBridge events to SMS, HTTP(s), email and SNS mobile push.
You can transform and filter the message using these services, often without needing an AWS Lambda function. SNS does not support input transformation but you can do this in an EventBridge rule. Message filtering is possible in both services but EventBridge provides richer content filtering capabilities.
AWS CloudTrail can log and monitor activity across services in your AWS account. It can be a useful source for events, allowing you to respond dynamically to objects in Amazon S3 or react to changes in your environment, for example. This natively integrates with EventBridge, allowing you to ingest events at scale from dozens of services.
Using EventBridge enables you to source events from outside your AWS account, offering integrations with a list of software as a service (SaaS) providers. This capability allows you to receive events from your accounts with SaaS providers like Zendesk, PagerDuty, and Auth0. These events are delivered to a partner event bus in your account, and can then be filtered and routed to an SNS topic.
Additionally, this pattern allows you to deliver events to Lambda functions in other AWS accounts and in other AWS Regions. You can invoke Lambda from SNS topics in other Regions and accounts. It’s also possible to make SNS topics publicly read-only, making them extensible endpoints that other third parties can consume from. SNS has comprehensive access control, which you can incorporate into this pattern.

EventBridge to SQS: Building fault-tolerant microservices
EventBridge can route events to targets such as microservices. In the case of downstream failures, the service retries events for up to 24 hours. For workloads where you need a longer period of time to store and retry messages, you can deliver the events to an SQS queue in each microservice. This durably stores those events until the downstream service recovers. Additionally, this pattern protects the microservice from large bursts of traffic by throttling the delivery of messages.

The resources declared in the AWS SAM template are similar to the previous examples, but it uses the AWS::SQS::QueuePolicy resource to grant the appropriate permission to EventBridge:
EventBridgeToToSqsPolicy:
Type: AWS::SQS::QueuePolicy
Properties:
PolicyDocument:
Statement:
- Effect: Allow
Principal:
Service: events.amazonaws.com
Action: SQS:SendMessage
Resource: !GetAtt MySqsQueue.Arn
Queues:
- Ref: MySqsQueue
Conclusion
You can combine these services in your architectures to implement patterns that solve complex challenges, often with little code required. This blog post shows three examples that implement message throttling and queueing, integrating SNS and EventBridge, and building fault tolerant microservices.
To learn more building decoupled architectures, see this Learning Path series on EventBridge. For more serverless learning resources, visit https://serverlessland.com.