Post Syndicated from Margaret Zonay original https://blog.rapid7.com/2021/07/08/whats-new-in-insightidr-q2-2021-in-review/

This year, we’re focusing on providing customers with more extensibility and customization in InsightIDR — from adding new event sources to completely refreshing our Dashboard and Reporting experience, we’ve made some strides over the last few months.
This post offers a closer look at some of the recent updates and releases in InsightIDR, our SaaS SIEM, from Q2 2021.
Rapid7 Named a Leader in the Gartner Magic Quadrant for SIEM for the Second Year in a Row
We are thrilled to announce that Rapid7 has been named a Leader in the 2021 Gartner Magic Quadrant for SIEM. As the detection and response market becomes more competitive, we are honored to be recognized as one of the six 2021 Magic Quadrant Leaders named in this report.
We credit this achievement to our deep partnership with customers and our uncompromising commitment to delivering a solution that is intuitive and easy to execute for our users. You can read the full report for free here.
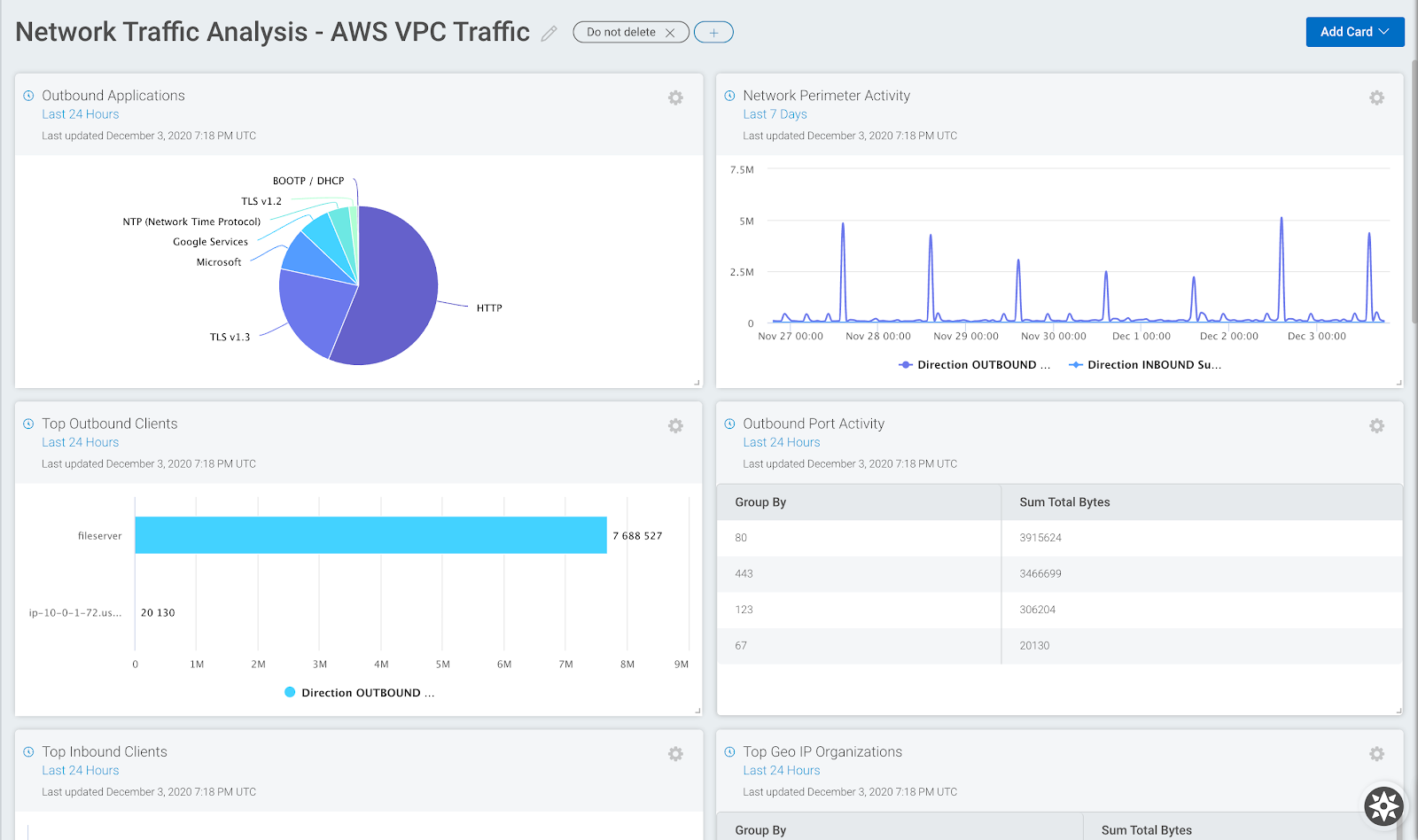
New and Improved Dashboards and Reporting Experience
We’re so excited to announce the release of our updated Dashboards and Reporting experience in InsightIDR! We’ve made some big improvements to our Card Library and Card Builder (including the addition of new visualizations), as well as a more customizable Reporting experience.
Card Library and Builder updates:
- Users can now set different time ranges or use different log sets across multiple queries
- Cards can be created from log sets, so you won’t need to manually update your dashboards if new logs get added
- More flexibility to create the visualizations that best capture the dynamics of your network with the new Stacked Area, Word Cloud, and Packed Bubble visualizations
Reporting updates:
- New functionality where users can now set multiple different reporting schedules, as well as email reports to any address for easier sharing
InsightIDR’s intuitive new Dashboard interface, featuring the new Word Cloud visualization.
Rapid7 and Velociraptor Join Forces
In April, Rapid7 acquired Velociraptor, an open-source technology and community used for endpoint monitoring, digital forensics, and incident response. We are committed to helping the Velociraptor community grow and thrive, and also plan to embed the Velociraptor Project into the Rapid7 Insight Platform, allowing our customers to benefit from this amazing technology and community.
Open source projects like Velociraptor enable the greater security community to move the industry forward. We have a track record of investing in, contributing to, and building on open source projects, dating as far back as 12 years ago with Metasploit, and in more recent years with Recog and AttackerKB. Supporting and learning from these open-source projects helps Rapid7 innovate, strengthen our product and service offerings, and bring greater value to our customers.
See more on our Velociraptor acquisition and what it means for Rapid7 customers in our blog post here.
Multi-Theme Support in InsightIDR
We’re excited to announce the release of the new dark theme in InsightIDR! This new theme will increase contrast and legibility, as well as reduce eye strain for users engaging with the screen for longer periods of time. It also provides more accessible options to those with color vision deficiency, enabling all users to have an optimal experience with our UI.
You can easily toggle between light and dark themes based on your needs for the task at hand by updating your Visual Preference within Profile Settings.
Switch between light and dark themes in InsightIDR in Profile Settings.
SCADAfence + InsightIDR for Broader OT Coverage
Joint customers of InsightIDR and SCADAfence can now configure SCADAfence to create and forward alerts to InsightIDR via syslog to generate third-party alerts.
For InsightIDR customers leveraging Enhanced Network Traffic Analysis, this integration will provide a broader picture of device activity. If a SCADAfence alert fires, Network Sensor data can show customers that not only is this device on their network, but also which network applications it’s associated with, as well as connections coming to and from that device.
For information on configuration, see our help documentation here.
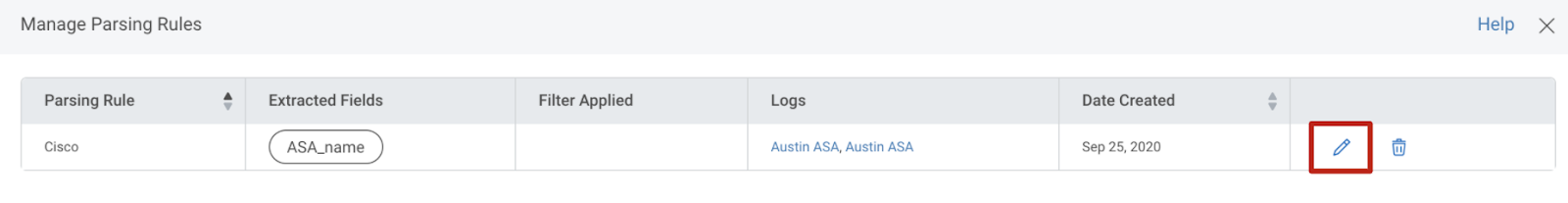
Custom Parsing Tool Introduces the New RegEx Editor
The new Regex Editor provides increased flexibility for customers to extract out fields and custom parse their logs by enabling them to write their own regular expression. Users can use the RegEx Editor from the start, or start out in guided mode and switch over at any time.
See details and step-by-step instructions on how to leverage the new RegEx Editor in our updated documentation here.
Extracting out fields with the new Regex Editor in InsightIDR.
Improvements for Better Visibility into the Health of Your Network Sensors
- View the number of deployed network sensors in your environment and related errors from the Data Collection Health page.
- Identify Network Sensor errors more easily within InsightIDR. Network Sensor errors are now rolled into the Data Collection Issues KPI on the InsightIDR Home page overview and in the Data Collection Health menu item in the top menu bar.
For more information on managing your Network Sensor, read our documentation.
Easily view Network Sensor health from the InsightIDR homepage via Data Collection Health.
Insight Agent Updates
Rapid7’s Threat Intelligence and Detection Engineering (TIDE) Team recently released a detection that identifies if Insight Agents are not properly sending data back to the InsightIDR Platform. For more information, see our help documentation here.
Stay Tuned for More!
As always, we’re continuing to work on exciting product enhancements and releases throughout the year. Keep an eye on our blog and release notes as we continue to highlight the latest in detection and response at Rapid7.