Post Syndicated from Louay Shaat original https://aws.amazon.com/blogs/security/build-an-end-to-end-attribute-based-access-control-strategy-with-aws-sso-and-okta/
This blog post discusses the benefits of using an attribute-based access control (ABAC) strategy and also describes how to use ABAC with AWS Single Sign-On (AWS SSO) when you’re using Okta as an identity provider (IdP).
Over the past two years, Amazon Web Services (AWS) has invested heavily in making ABAC available across the majority of our services. With ABAC, you can simplify your access control strategy by granting access to groups of resources, which are specified by tags, instead of managing long lists of individual resources. Each tag is a label that consists of a user-defined key and value, and you can use these to assign metadata to your AWS resources. Tags can help you manage, identify, organize, search for, and filter resources. You can create tags to categorize resources by purpose, owner, environment, or other criteria. To learn more about tags and AWS best practices for tagging, see Tagging AWS resources.
The ability to include tags in sessions—combined with the ability to tag AWS Identity and Access Management (IAM) users and roles—means that you can now incorporate user attributes from your identity provider as part of your tagging and authorization strategy. Additionally, user attributes help organizations to make permissions more intuitive, because the attributes are easier to relate to teams and functions. A tag that represents a team or a job function is easier to audit and understand.
For more information on ABAC in AWS, see our ABAC documentation.
Why use ABAC?
ABAC is a strategy that that can help organizations to innovate faster. Implementing a purely role-based access control (RBAC) strategy requires identity and security teams to define a large number of RBAC policies, which can lead to complexity and time delays. With ABAC, you can make use of attributes to build more dynamic policies that provide access based on matching the attribute conditions. AWS supports both RBAC and ABAC as co-existing strategies, so you can use ABAC alongside your existing RBAC strategy.
A good example that uses ABAC is the scenario where you have two teams that require similar access to their secrets in AWS Secrets Manager. By using ABAC, you can build a single role or policy with a condition based on the Department attribute from your IdP. When the user is authenticated, you can pass the Department attribute value and use a condition to provide access to resources that have the identical tag, as shown in the following code snippet. In this post, I show how to use ABAC for this example scenario.
"Condition": {
"StringEquals": {
"secretsmanager:ResourceTag/Department": "${aws:PrincipalTag/Department}"
ABAC provides organizations with a more dynamic way of working with permissions. There are four main benefits for organizations that use ABAC:
- Scale your permissions as you innovate: As developers create new project resources, administrators can require specific attributes to be applied when resources are created. This can include applying tags with attributes that give developers immediate access to the new resources they create, without requiring an update to their own permissions.
- Help your teams to change and grow quickly: Because permissions are based on user attributes from a corporate identity source such as an IdP, changing user attributes in the IdP that you use for access control in AWS automatically updates your permissions in AWS.
- Create fewer AWS SSO permission sets and IAM roles: With ABAC, multiple users who are using the same AWS SSO permission set and IAM role can still get unique permissions, because permissions are now based on user attributes. Administrators can author IAM policies that grant users access only to AWS resources that have matching attributes. This helps to reduce the number of IAM roles you need to create for various use cases in a single AWS account.
- Efficiently audit who performed an action: By using attributes that are logged in AWS CloudTrail next to every action that is performed in AWS by using an IAM role, you can make it easier for security administrators to determine the identity that takes actions in a role session.
Prerequisites
In this section, I describe some higher-level prerequisites for using ABAC effectively. ABAC in AWS relies on the use of tags for access-control decisions, so it’s important to have in place a tagging strategy for your resources. To help you develop an effective strategy, see the AWS Tagging Strategies whitepaper.
Organizations that implement ABAC can enhance the use of tags across their resources for the purpose of identity access. Making sure that tagging is enforced and secure is essential to an enterprise-wide strategy. For more information about enforcing a tagging policy, see the blog post Enforce Centralized Tag Compliance Using AWS Service Catalog, DynamoDB, Lambda, and CloudWatch Events.
You can use the service AWS Resource Groups to identify untagged resources and to find resources to tag. You can also use Resource Groups to remediate untagged resources.
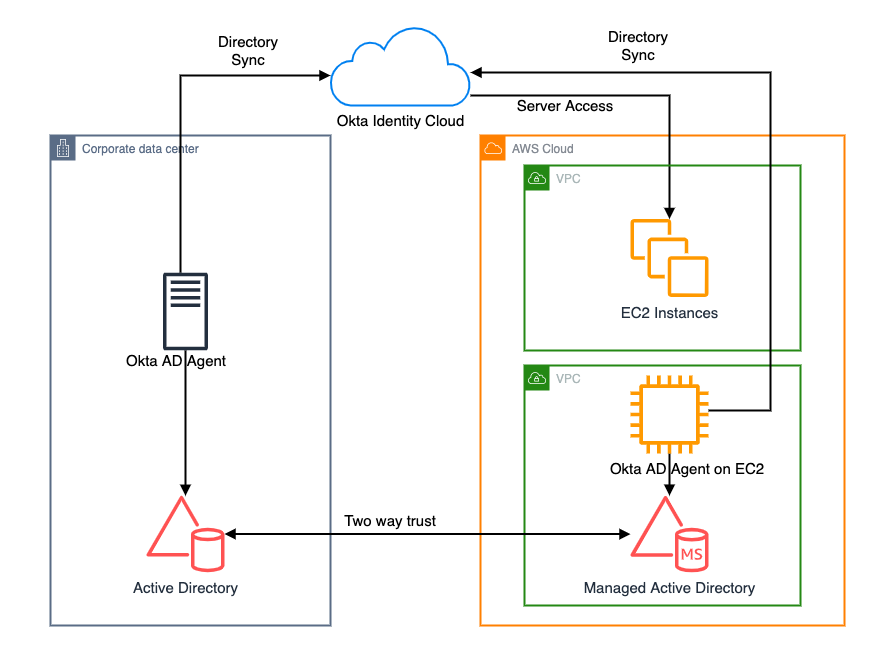
Use AWS SSO with Okta as an IdP
AWS SSO gives you an efficient way to centrally manage access to multiple AWS accounts and business applications, and to provide users with single sign-on access to all their assigned accounts and applications from one place. With AWS SSO, you can manage access and user permissions to all of your accounts in AWS Organizations centrally. AWS SSO configures and maintains all the necessary permissions for your accounts automatically, without requiring any additional setup in the individual accounts.
AWS SSO supports access control attributes from any IdP. This blog post focuses on how you can use ABAC attributes with AWS SSO when you’re using Okta as an external IdP.
Use other single sign-on services with ABAC
This post describes how to turn on ABAC in AWS SSO. To turn on ABAC with other federation services, see these links:
Implement the solution
Follow these steps to set up Okta as an IdP in AWS SSO and turn on ABAC.
To set up Okta and turn on ABAC
- Set up Okta as an IdP for AWS SSO. To do so, follow the instructions in the blog post Single Sign-On Between Okta Universal Directory and AWS. For more information on the supported actions in AWS SSO with Okta, see our documentation.
- Enable attributes for access control (in other words, turn on ABAC) in AWS SSO by using these steps:
- In the AWS Management Console, navigate to AWS SSO in the AWS Region you selected for your implementation.
- On the Dashboard tab, select Choose your identity source.
- Next to Attributes for access control, choose Enable.

Figure 1: Turn on ABAC in AWS SSO
You should see the message “Attributes for access control has been successfully enabled.”
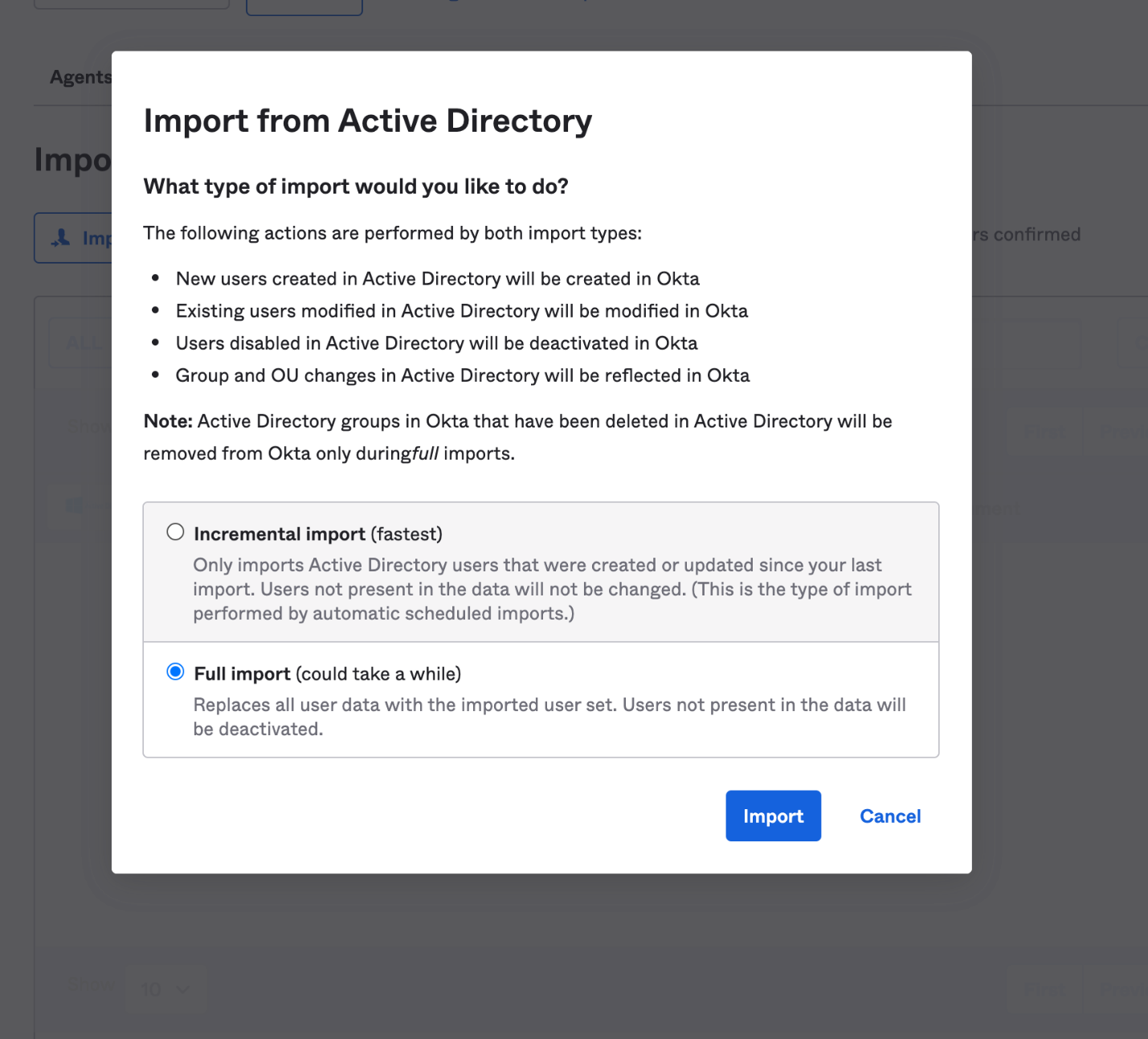
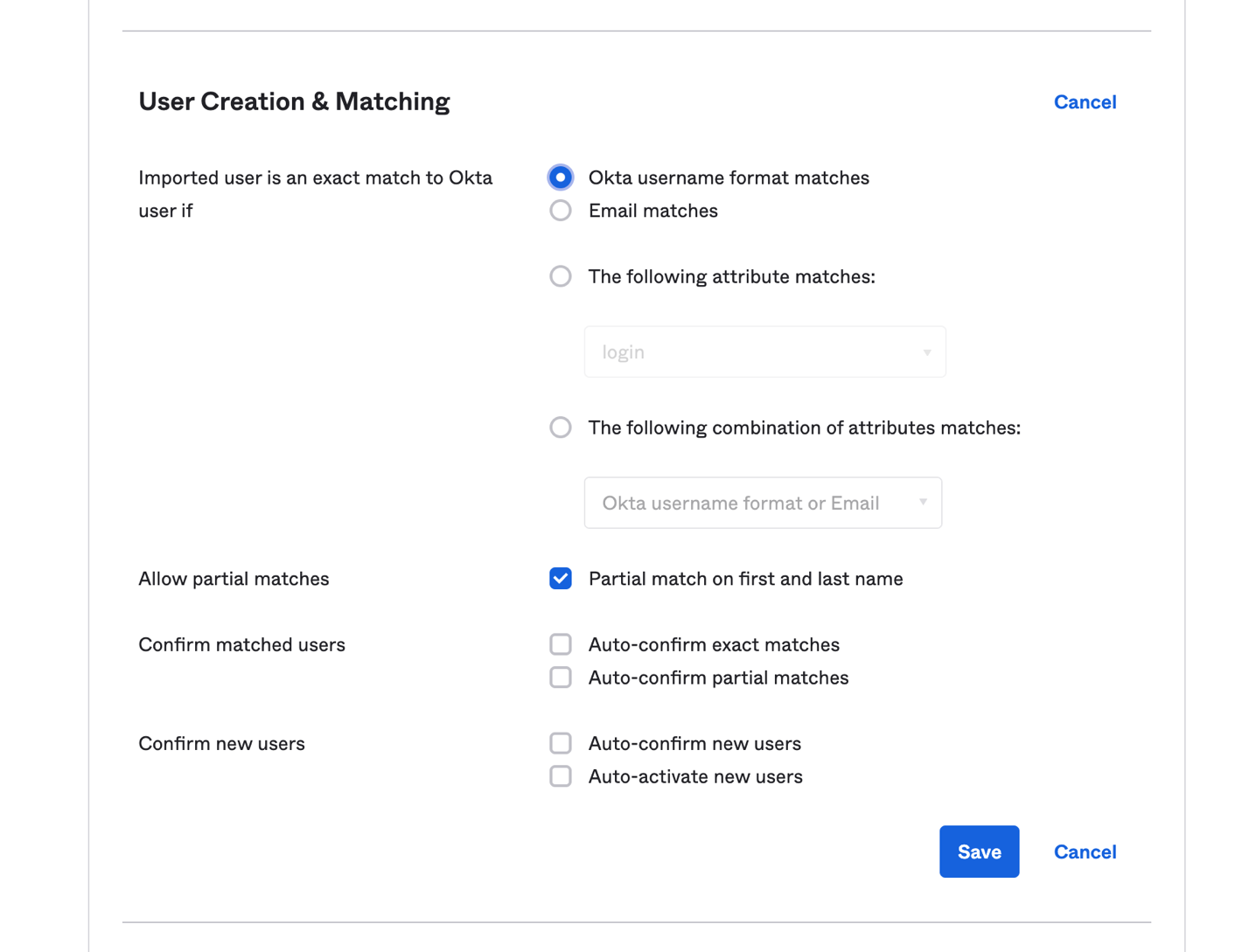
- Enable updates for user attributes in Okta provisioning. Now that you’ve turned on ABAC in AWS SSO, you need to verify that automatic provisioning for Okta has attribute updates enabled.Log in to Okta as an administrator and locate the application you created for AWS SSO. Navigate to the Provisioning tab, choose Edit, and verify that Update User Attributes is enabled.

Figure 2: Enable automatic provisioning for ABAC updates
- Configure user attributes in Okta for use in AWS SSO by following these steps:
- From the same application that you created earlier, navigate to the Sign On tab.
- Choose Edit, and then expand the Attributes (optional) section.
- In the Attribute Statements (optional) section, for each attribute that you will use for access control in AWS SSO, do the following:
- For Name, enter https://aws.amazon.com/SAML/Attributes/AccessControl:<AttributeName>. Replace <AttributeName> with the name of the attribute you’re expecting in AWS SSO, for example https://aws.amazon.com/SAML/Attributes/AccessControl:Department.
- For Name Format, choose URI reference.
- For Value, enter user.<AttributeName>. Replace <AttributeName> with the Okta default user profile variable name, for example user.department. To view the Okta default user profile, see these instructions.

Figure 3: Configure two attributes for users in Okta
In the example shown here, I added two attributes, Department and Division. The result should be similar to the configuration shown in Figure 3.
- Add attributes to your users by using these steps:
- In your Okta portal, log in as administrator. Navigate to Directory, and then choose People.
- Locate a user, navigate to the Profile tab, and then choose Edit.
- Add values to the attributes you selected.

Figure 4: Addition of user attributes in Okta
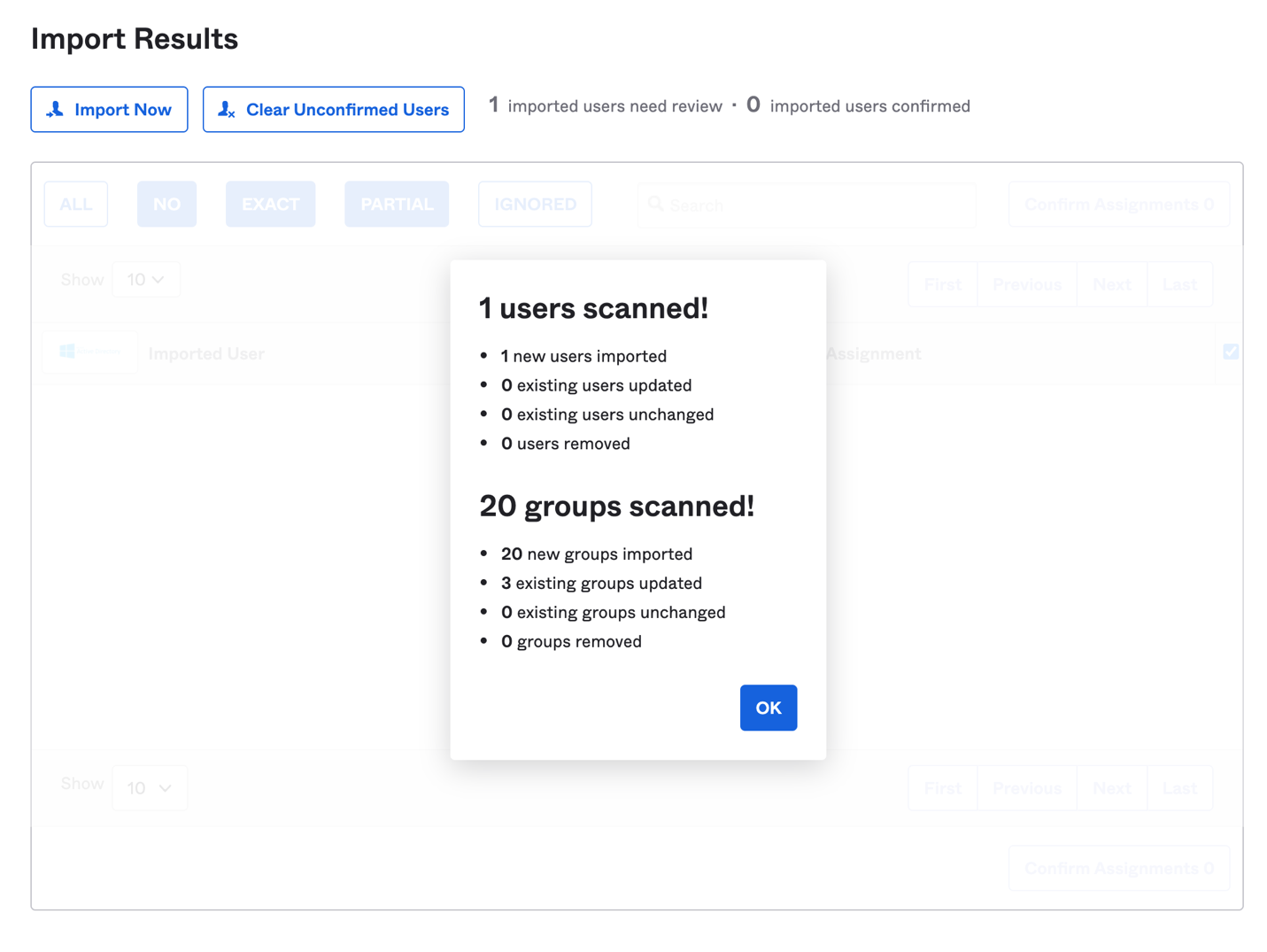
- Confirm that attributes are mapped. Because you’ve enabled automatic provisioning updates from Okta, you should be able to see the attributes for your user immediately in AWS SSO. To confirm this:
- In the console, navigate to AWS SSO in the Region you selected for your implementation.
- On the Users tab, select a user that has attributes from Okta, and select the user. You should be able to see the attributes that you mapped from Okta.

Figure 5: User attributes in Okta
Now that you have ABAC attributes for your users in AWS SSO, you can now create permission sets based on those attributes.
Note: Step 4 ensures that users will not be successfully authenticated unless the attributes configured are present. If you don’t want this enforcement, do not perform step 4.
Build an ABAC permission set in AWS SSO
For demonstration purposes, I’ll show how you can build a permission set that is based on ABAC attributes for AWS Secrets Manager. The permission set will match resource tags to user tags, in order to control which resources can be managed by Secrets Manager administrators. You can apply this single permission set to multiple teams.
To build the ABAC permission set
- In the console, navigate to AWS SSO, and choose AWS Accounts.
- Choose the Permission sets tab.
- Choose Create permission set, and then choose Create a custom permission set.
- Fill in the fields as follows.
- For Name, enter a name for your permission set that will be visible to your users, for example, SecretsManager-Profile.
- For Description, enter ABAC SecretsManager Profile.
- Select the appropriate session duration.
- For Relay State, for my example I will enter the URL for Secrets Manager: https://console.aws.amazon.com/secretsmanager/home. This will give a better user experience when the user signs in to AWS SSO, with an automatic redirect to the Secrets Manager console.
- For the field What policies do you want to include in your permission set?, choose Create a custom permissions policy.
- Under Create a custom permissions policy, paste the following policy.
{
"Version": "2012-10-17",
"Statement": [
{
"Sid": "SecretsManagerABAC",
"Effect": "Allow",
"Action": [
"secretsmanager:DescribeSecret",
"secretsmanager:PutSecretValue",
"secretsmanager:CreateSecret",
"secretsmanager:ListSecretVersionIds",
"secretsmanager:UpdateSecret",
"secretsmanager:GetResourcePolicy",
"secretsmanager:GetSecretValue",
"secretsmanager:ListSecrets",
"secretsmanager:TagResource"
],
"Resource": "*",
"Condition": {
"StringEquals": {
"secretsmanager:ResourceTag/Department": "${aws:PrincipalTag/Department}"
}
}
},
{
"Sid": "NeededPermissions",
"Effect": "Allow",
"Action": [
"kms:ListKeys",
"kms:ListAliases",
"rds:DescribeDBInstances",
"redshift:DescribeClusters",
"rds:DescribeDBClusters",
"secretsmanager:ListSecrets",
"tag:GetResources",
"lambda:ListFunctions"
],
"Resource": "*"
}
]
}
This policy grants users the ability to create and list secrets that belong to their department. The policy is configured to allow Secrets Manager users to manage only the resources that belong to their department. You can modify this policy to perform matching on more attributes, in order to have more granular permissions.
Note: The RDS permissions in the policy enable users to select an RDS instance for the secret and the Lambda Permissions are to enable custom key rotation.
If you look closely at the condition
“secretsmanager:ResourceTag/Department”: “${aws:PrincipalTag/Department}”
…the condition states that the user can only access Secrets Manager resources that have a Department tag, where the value of that tag is identical to the value of the Department tag from the user.
- Choose Next: Tags.
- Tag your permission set. For my example, I’ll add Key: Service and Value: SecretsManager.
- Choose Next: Review and create.
- Assign the permission set to a user or group and to the appropriate accounts that you have in AWS Organizations.
Test an ABAC permission set
Now you can test the ABAC permission set that you just created for Secrets Manager.
To test the ABAC permission set
- In the AWS SSO console, on the Dashboard page, navigate to the User Portal URL.
- Sign in as a user who has the attributes that you configured earlier in AWS SSO. You will assume the permission set that you just created.
- Choose Management console. This will take you to the console that you specified in the Relay State setting for the permission set, which in my example is the Secrets Manager console.

Figure 6: AWS SSO ABAC profile access
- Try to create a secret with no tags:
- Choose Store a new secret.
- Choose Other type of secrets.
- You can add any values you like for the other options, and then choose Next.
- Give your secret a name, but don’t add any tags. Choose Next.
- On the Configure automatic rotation page, choose Next, and then choose Store.
You should receive an error stating that the user failed to create the secret, because the user is not authorized to perform the secretsmanager:CreateSecret action.

Figure 7: Failure to create a secret (no attributes)
- Choose Previous twice, and then add the appropriate tag. For my example, I’ll add a tag with the key Department and the value Serverless.

Figure 8: Adding tags for a secret
- Choose Next twice, and then choose Store. You should see a message that your secret creation was successful.

Figure 9: Successful secret creation
Now administrators who assume this permission set can view, create, and manage only the secrets that belong to their team or department, based on the tags that you defined. You can reuse this permission set across a large number of teams, which can reduce the number of permission sets you need to create and manage.
Summary
In this post, I’ve talked about the benefits organizations can gain from embracing an ABAC strategy, and walked through how to turn on ABAC attributes in Okta and AWS SSO. I’ve also shown how you can create ABAC-driven permission sets to simplify your permission set management. For more information on AWS services that support ABAC—in other words, authorization based on tags—see our updated AWS services that work with IAM page.
If you have feedback about this blog post, submit comments in the Comments section below. If you have questions about this post, start a new thread on the AWS Single Sign-On forum.
Want more AWS Security how-to content, news, and feature announcements? Follow us on Twitter.