Post Syndicated from Adam Barnett original https://www.rapid7.com/blog/post/em-patch-tuesday-november-2025
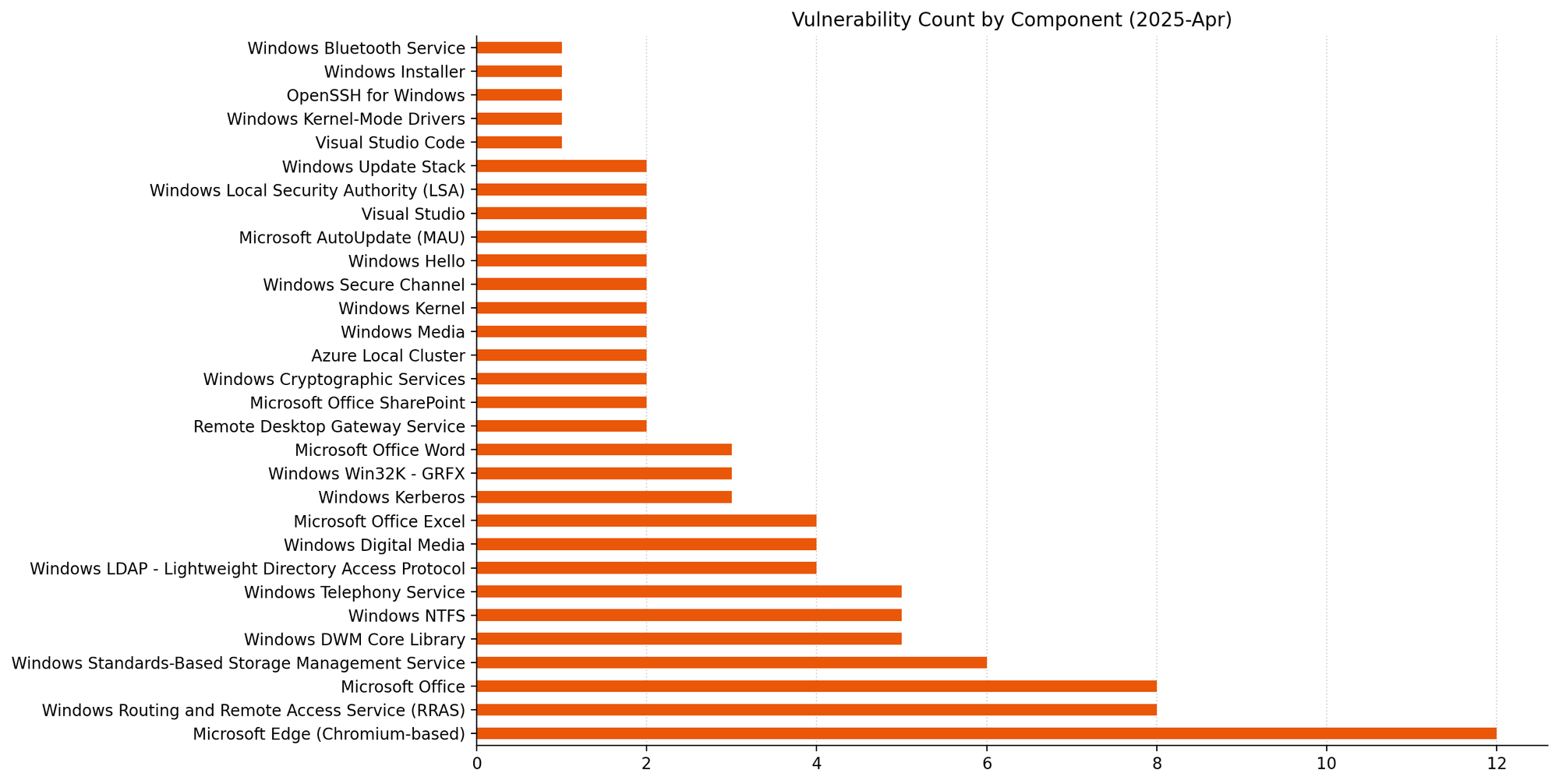
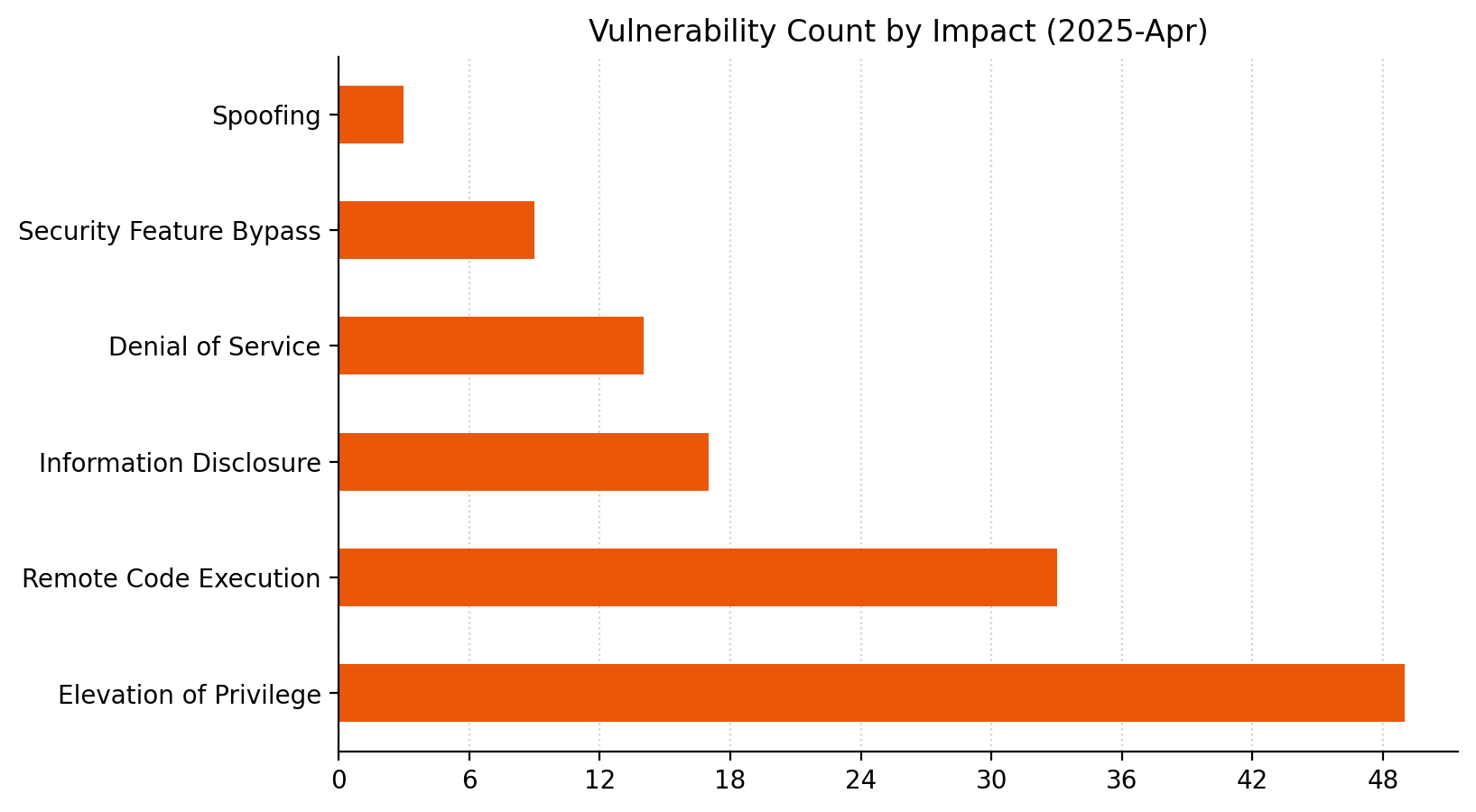
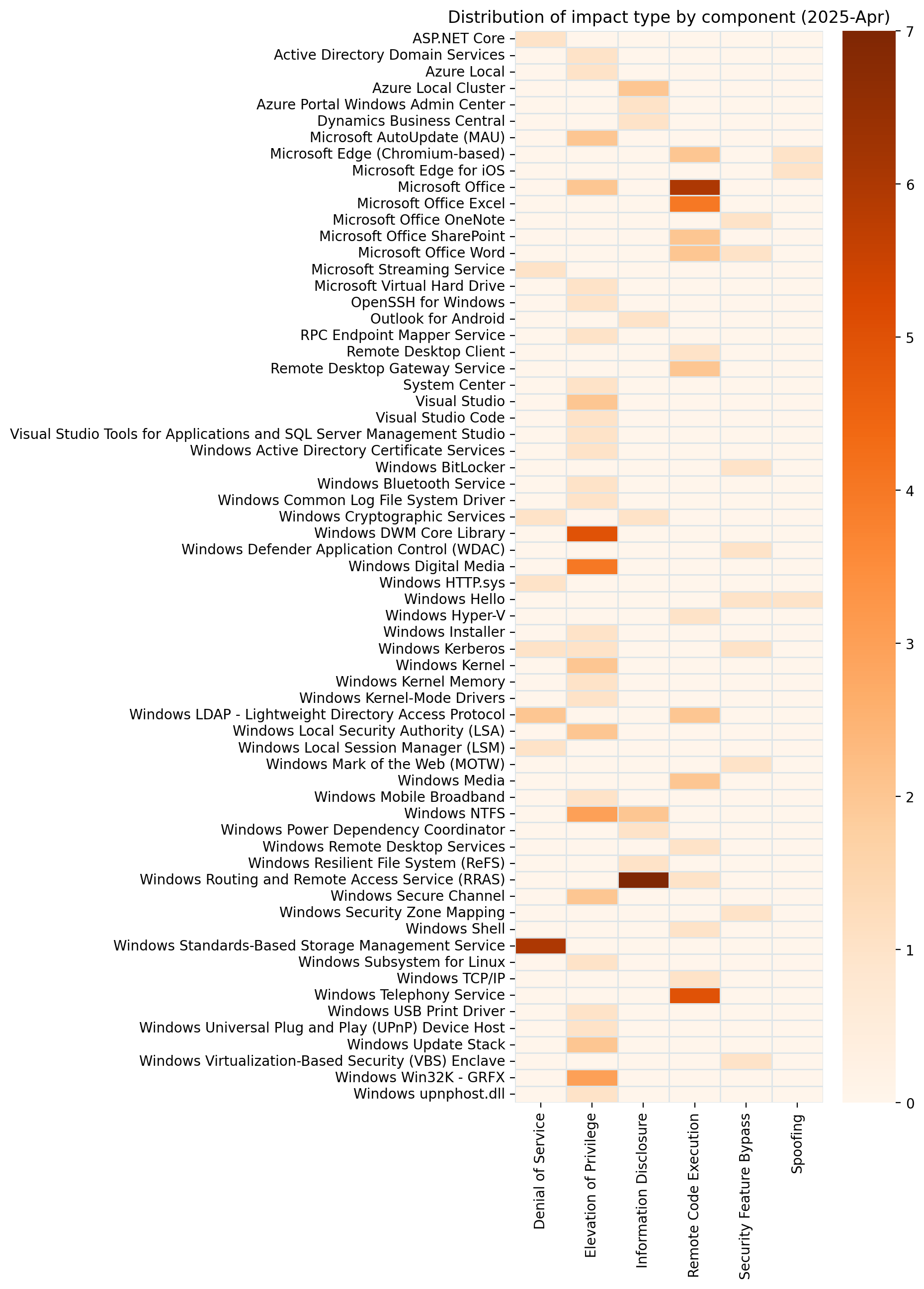
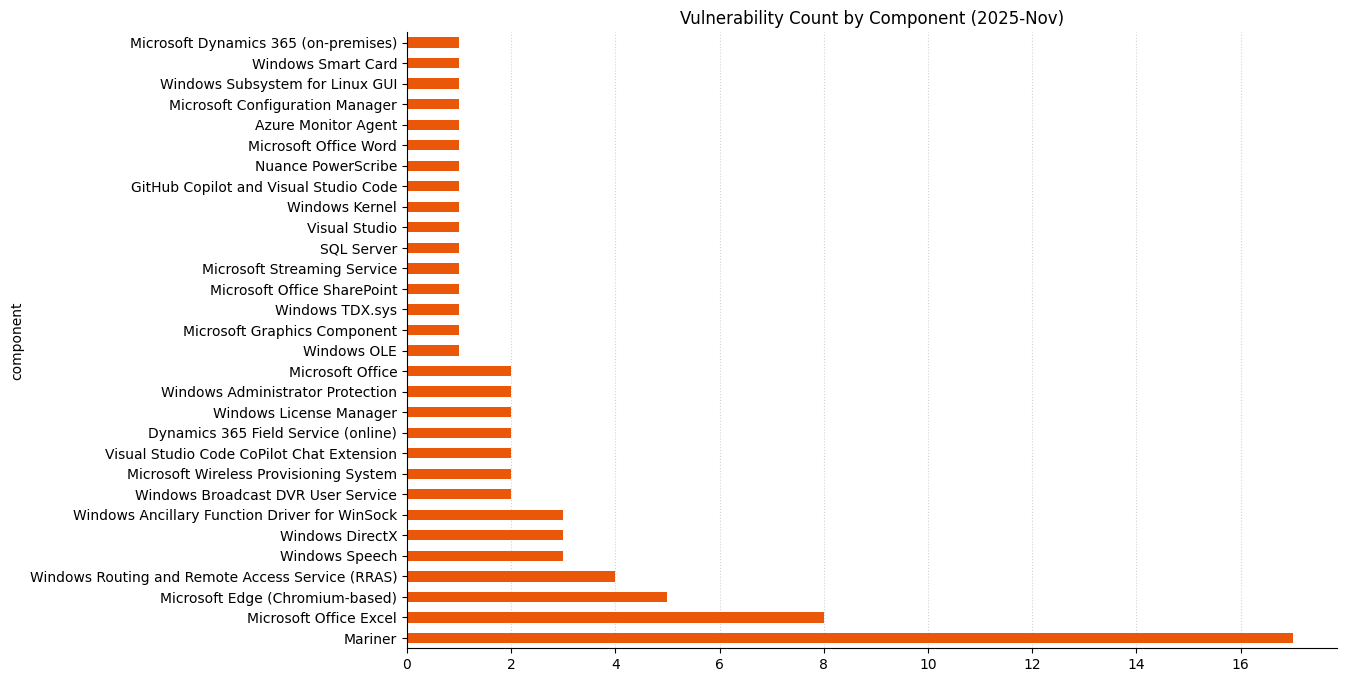
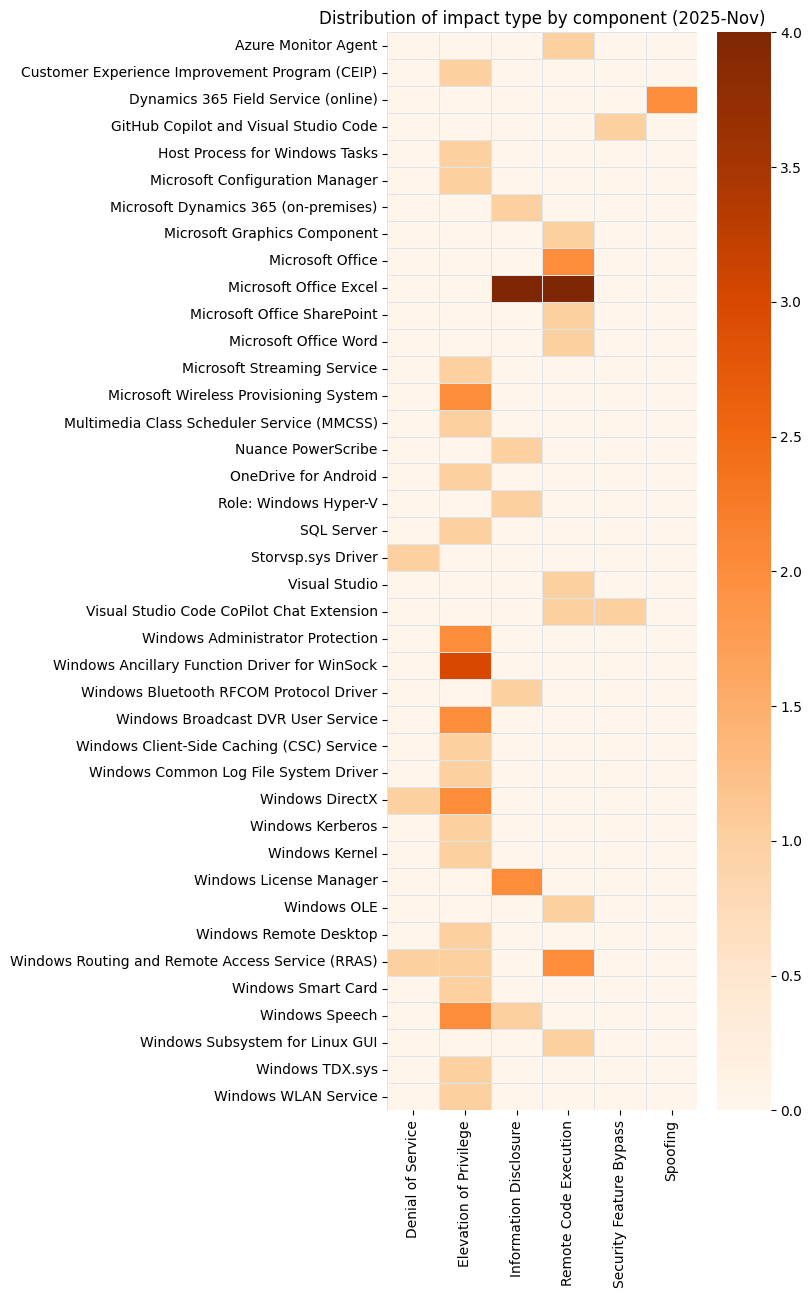
Microsoft is publishing 66 new vulnerabilities today, which is far fewer than we’ve come to expect in recent months. There’s a lone exploited-in-the-wild zero-day vulnerability, which Microsoft assesses as critical severity, although there’s apparently no public disclosure yet. Three critical remote code execution (RCE) vulnerabilities are patched today; happily, Microsoft currently assesses all three as less likely to see exploitation. Five browser vulnerabilities and a dozen or so fixes for Azure Linux (aka Mariner) have already been published separately this month, and are not included in the total.
Windows GDI+: critical 0-day RCE
Faced with a fresh stack of Patch Tuesday vulns, there are a few different ways to prioritize our analysis. Do we start with vulns exploited in the wild? Pre-authentication RCEs? The vuln with the highest CVSS base score? The vuln which is likely to affect just about every asset running Microsoft software? Any of these are sensible avenues of approach, and today, all roads lead to CVE-2025-60724. As the advisory notes, in the worst-case scenario, an attacker could exploit this vulnerability by uploading a malicious document to a vulnerable web service. The advisory doesn’t spell out the context of code execution, but if all the stars align for the attacker, the prize could be remote code execution as SYSTEM via the network without any need for an existing foothold. While this vuln almost certainly isn’t wormable, it’s clearly very serious and is surely a top priority for just about anyone considering how to approach this month’s patches.
The weakness underlying CVE-2025-60724 is CWE-122: Heap-based buffer overflow, a concept which celebrated its 50th birthday several years ago. As the authors of the original 1972 paper noted: “If the code makes use of an internal buffer, there is a possibility that a user could input enough data to overwrite other portions of the program’s private storage.” Regarding computer security in general, they opined that “this problem is neither hopeless nor solved. It is, however, perfectly clear […] that solutions to the problem will not occur spontaneously, nor will they come from the various well-intentioned attempts to provide security as an add-on to existing systems.”
Office: critical ACE
Once again, we find ourselves wondering: “when is remote code execution really remote?” CVE-2025-62199 describes a critical RCE vulnerability in Microsoft Office, where exploitation relies on the user downloading and opening a malicious file. The attacker is remote, and that’s enough to satisfy the definition, even if the action is taken on the local system by the unwitting user. Anyone hoping that the Preview Pane is not a vector will be sadly disappointed, and this certainly increases the probability of real-world exploitation, since there’s no need for the attacker to craft a way around those pesky warnings about enabling dangerous content. Just scrolling through a list of emails in Outlook could be enough.
Visual Studio: critical RCE
Some attacks are straightforward, with only a single step needed to reach the finish line. Others, like Visual Studio critical RCE CVE-2025-62214, require that the attacker execute a complex chain of events. In this case, exploitation demands multi-stage abuse of recent advances in Visual Studio AI development capabilities, including prompt injection, Agent interaction, and triggering a build. The advisory doesn’t describe the context of code execution. If the prize is simply code execution on an asset in the context of the user, there’s no obvious advancement for the attacker, since exploitation already requires code execution on the asset by the attacker or the targeted user. The brief description of the attack chain does mention that the attacker would need to trigger a build. On that basis, possible outcomes might include execution in an elevated context, or compromised build artifacts, although the advisory does not provide enough information to be certain either way.
SQL Server: critical EoP
SQL Server admins should take note of CVE-2025-59499, which describes an elevation of privilege (EoP) vulnerability. Although some level existing privileges are required, successful exploitation will permit an attacker to run arbitrary Transact-SQL (T-SQL) commands. T-SQL is the language which SQL Server databases and clients use to communicate with one another. Although the default configuration for SQL Server disables the xp_cmdshell functionality which allows direct callouts to the underlying OS, there’s more than one way to shine a penny, and the only safe assumption here is that exploitation will lead to code execution in the context of SQL Server itself. Patches are available for all supported versions of SQL Server.
Microsoft lifecycle update
Following the sweeping lifecycle changes seen in October 2025, Microsoft is taking it fairly easy this month. The only significant transition today is the end of support for Windows 11 Home and Pro 23H2. Unlike the demise of Windows 10, this much smaller change won’t affect most people; a small number of older CPUs might not make the cut, since Windows 11 24H2 introduces a requirement for a couple of newer CPU instruction sets. Microsoft provides lists of compatible Intel, AMD, and Qualcomm CPU series.
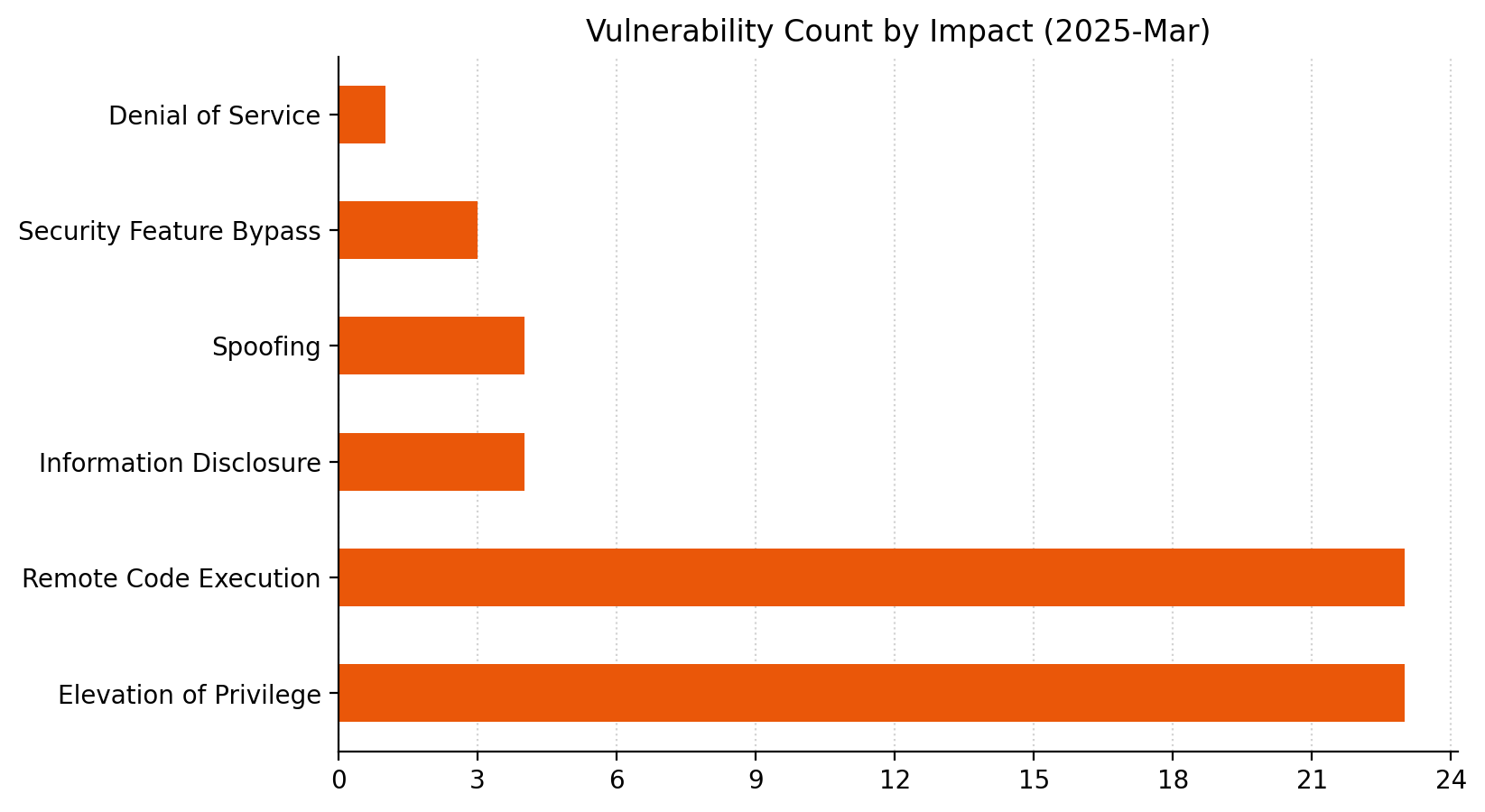
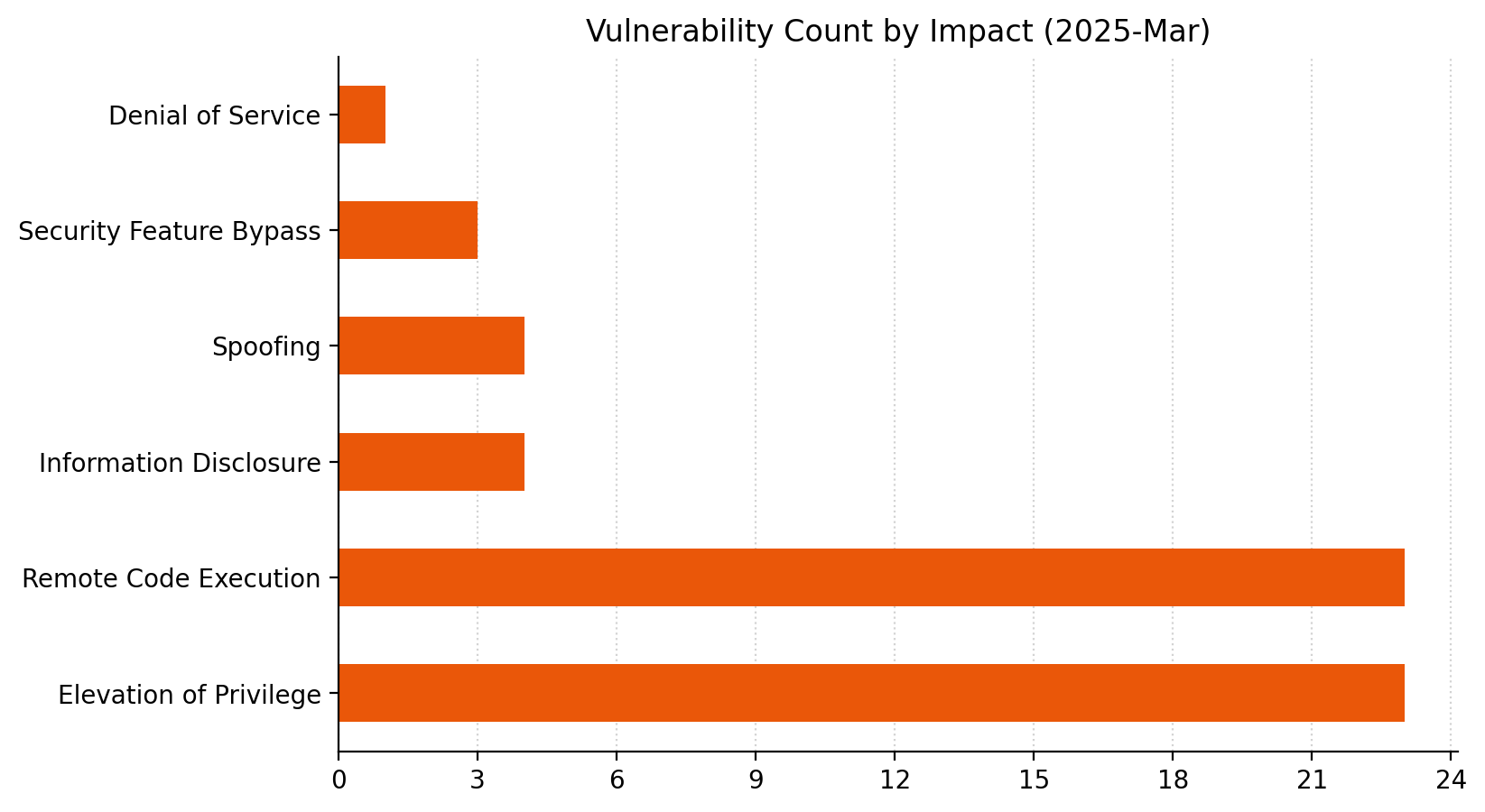
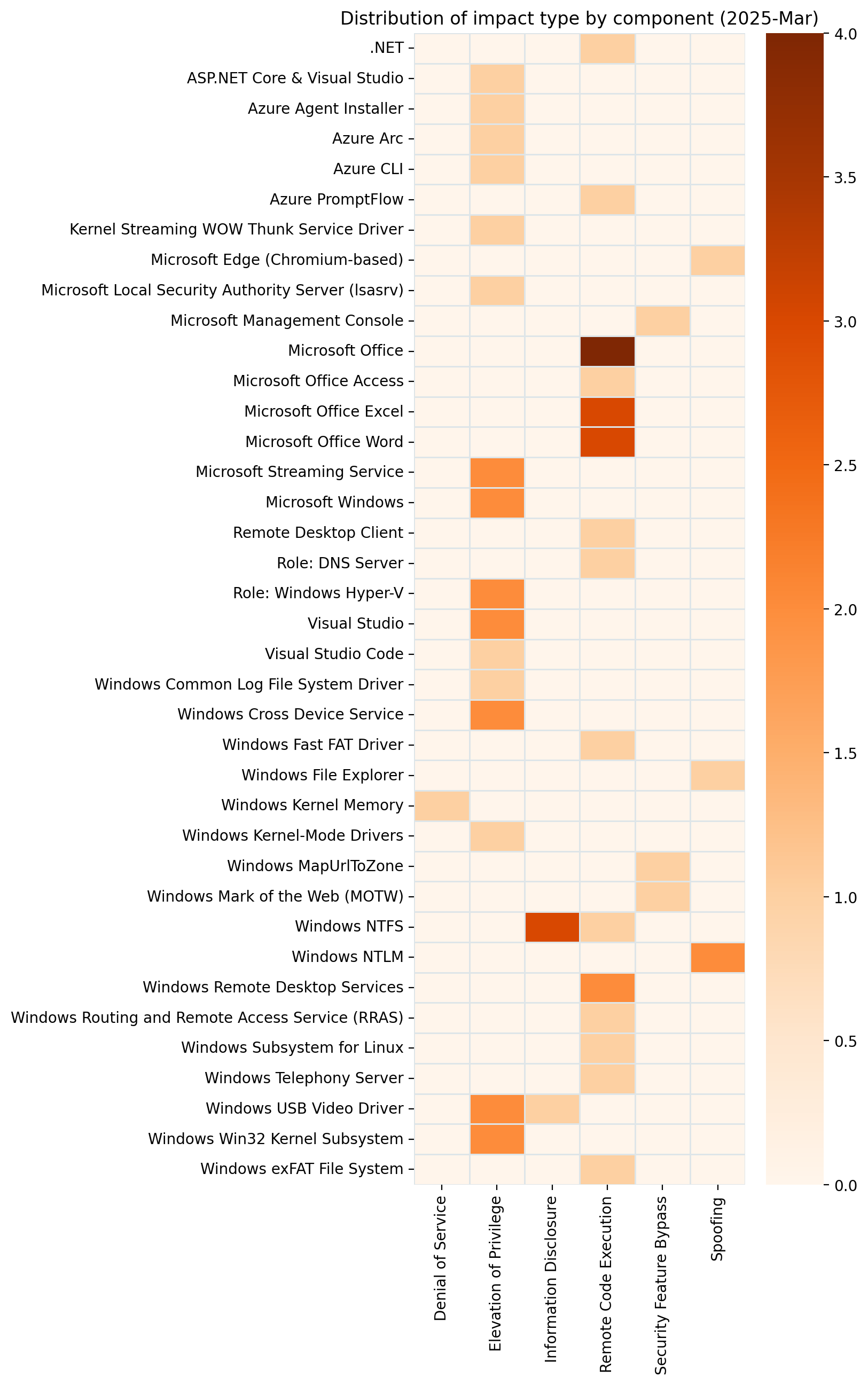
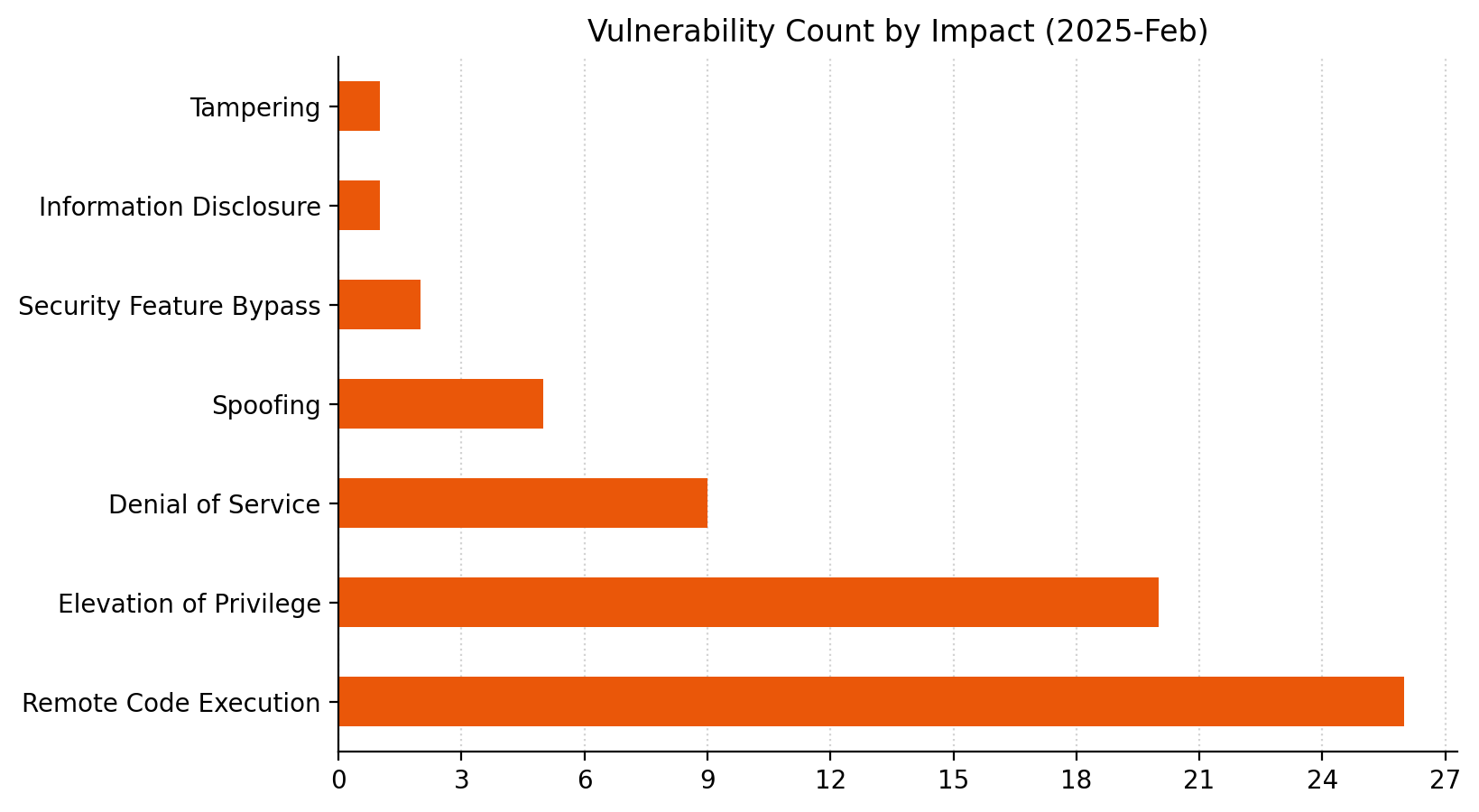
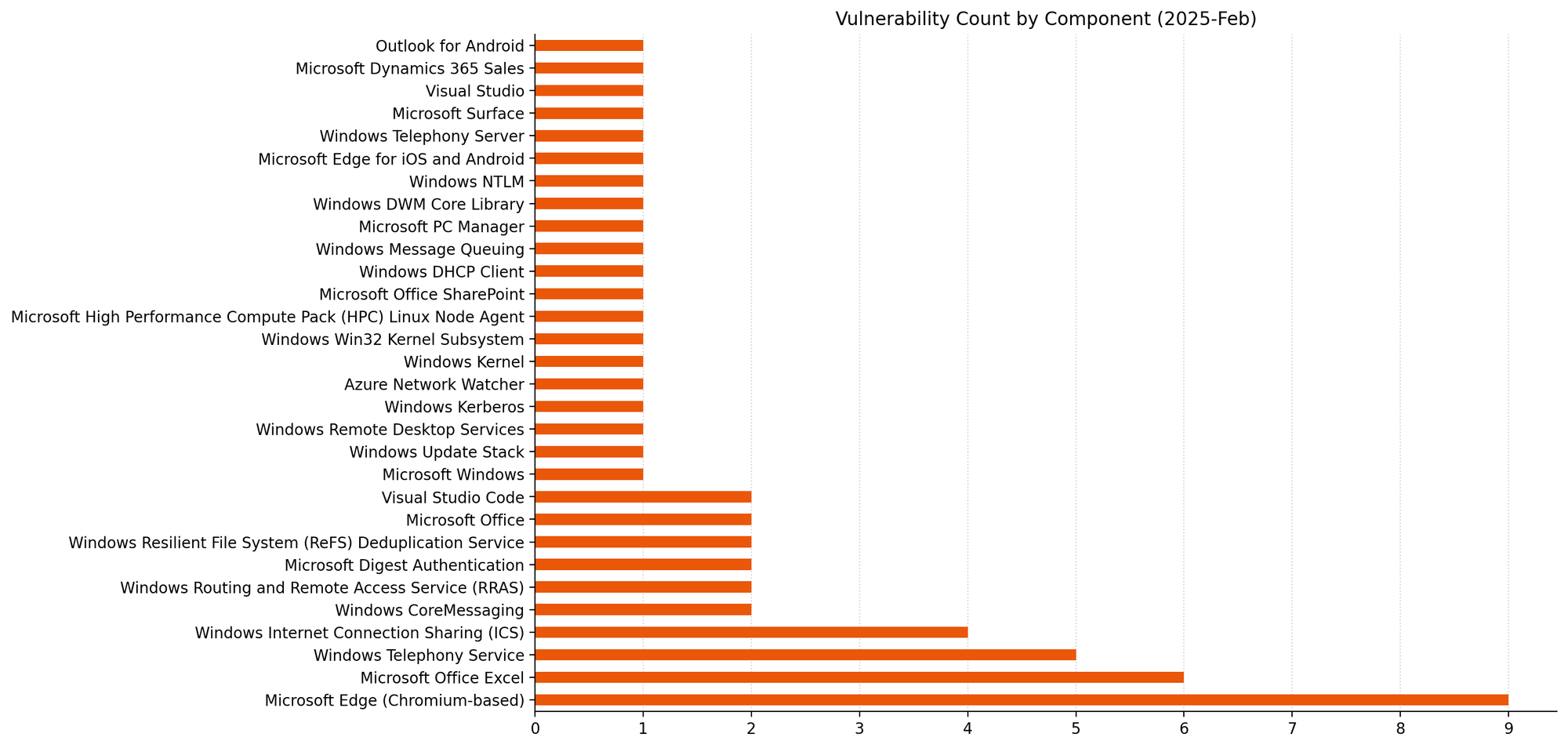
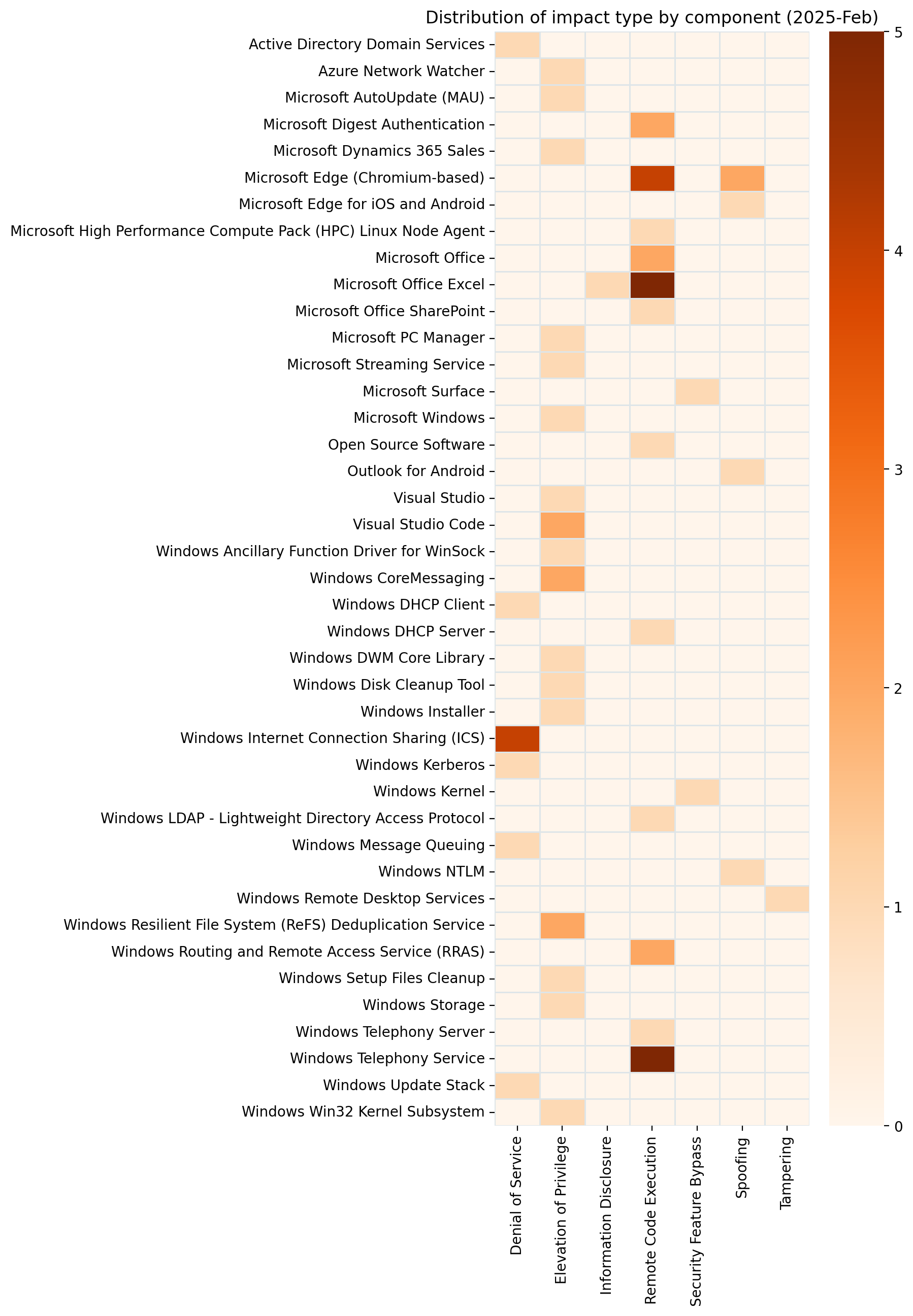
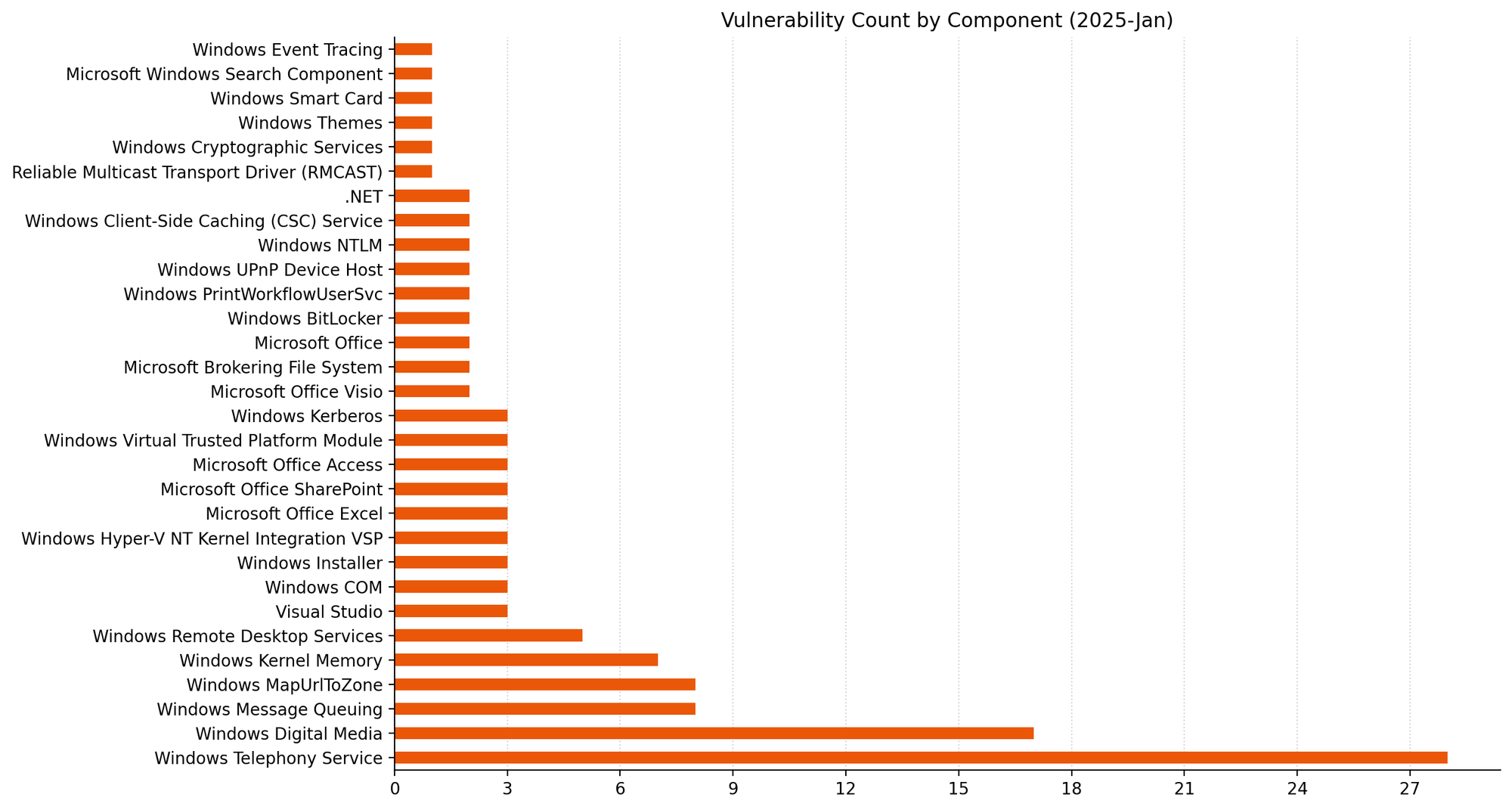
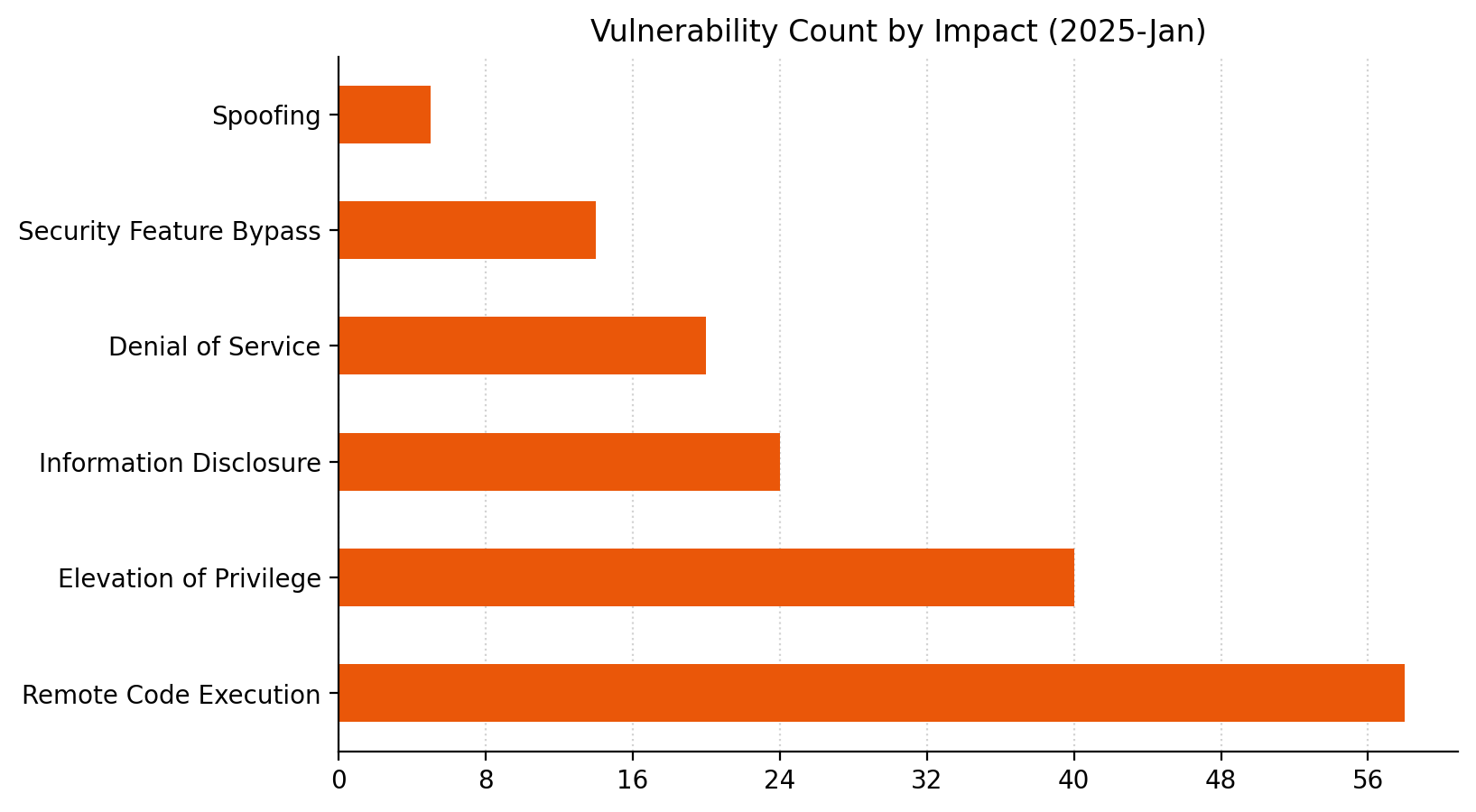
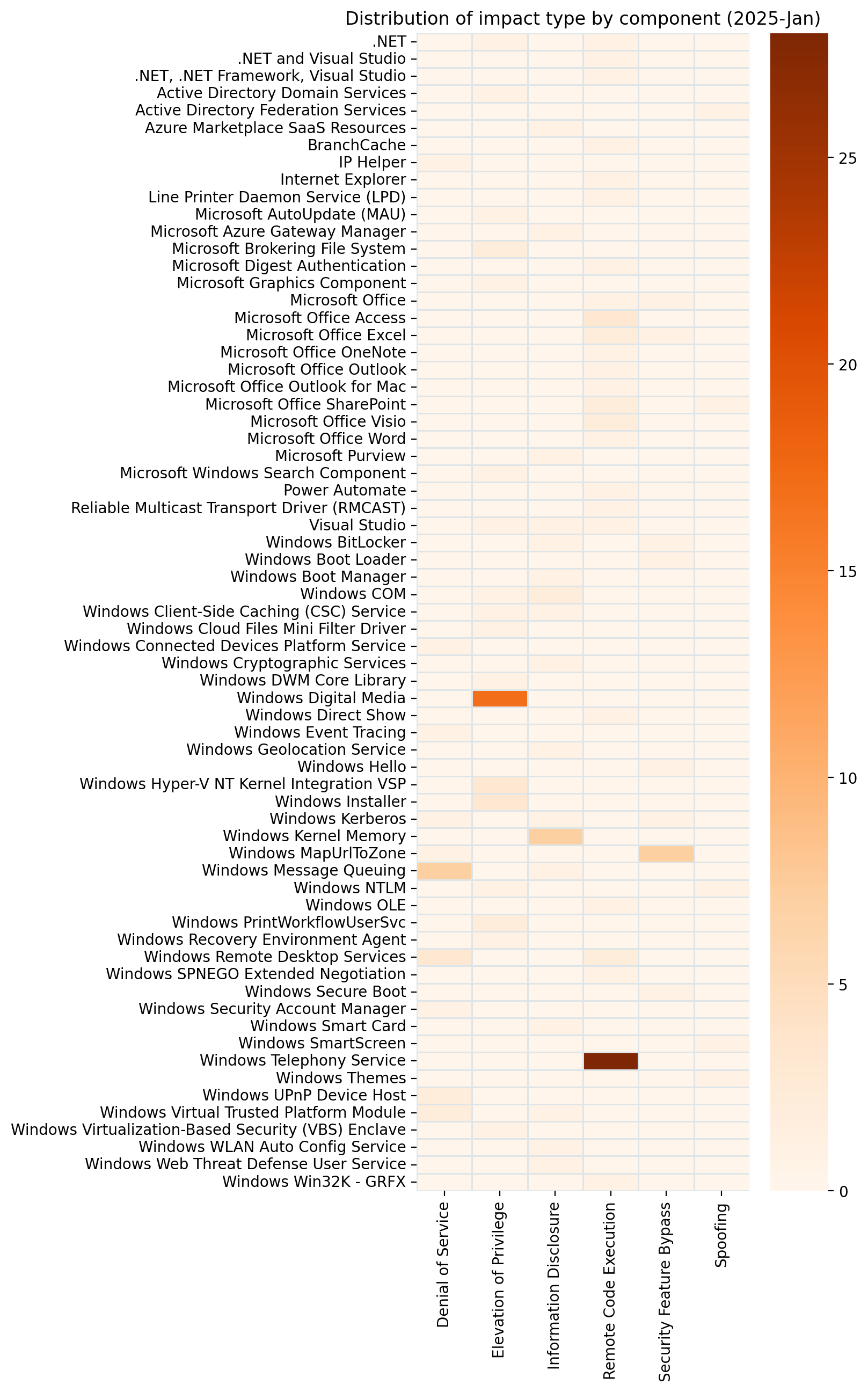
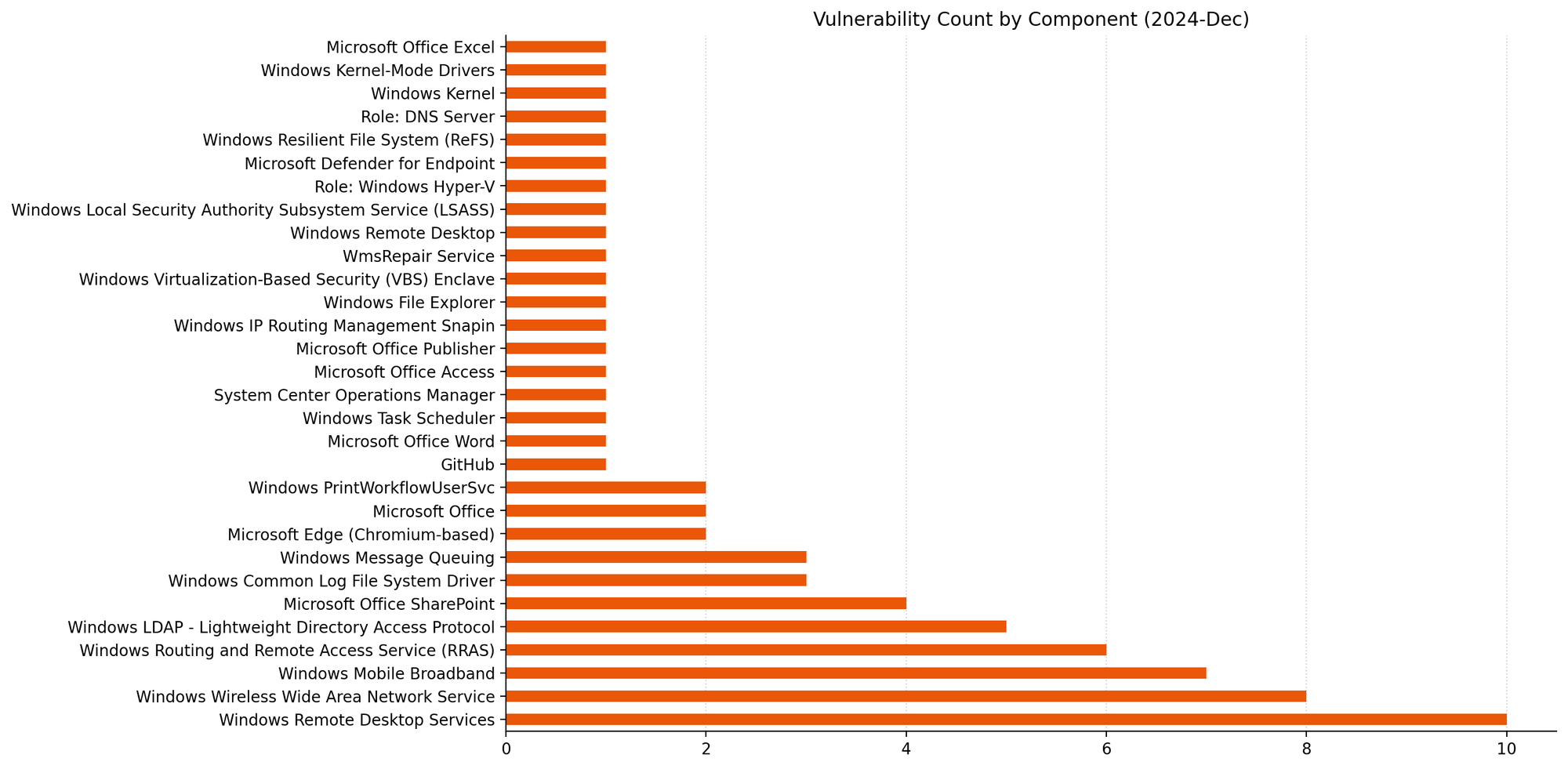
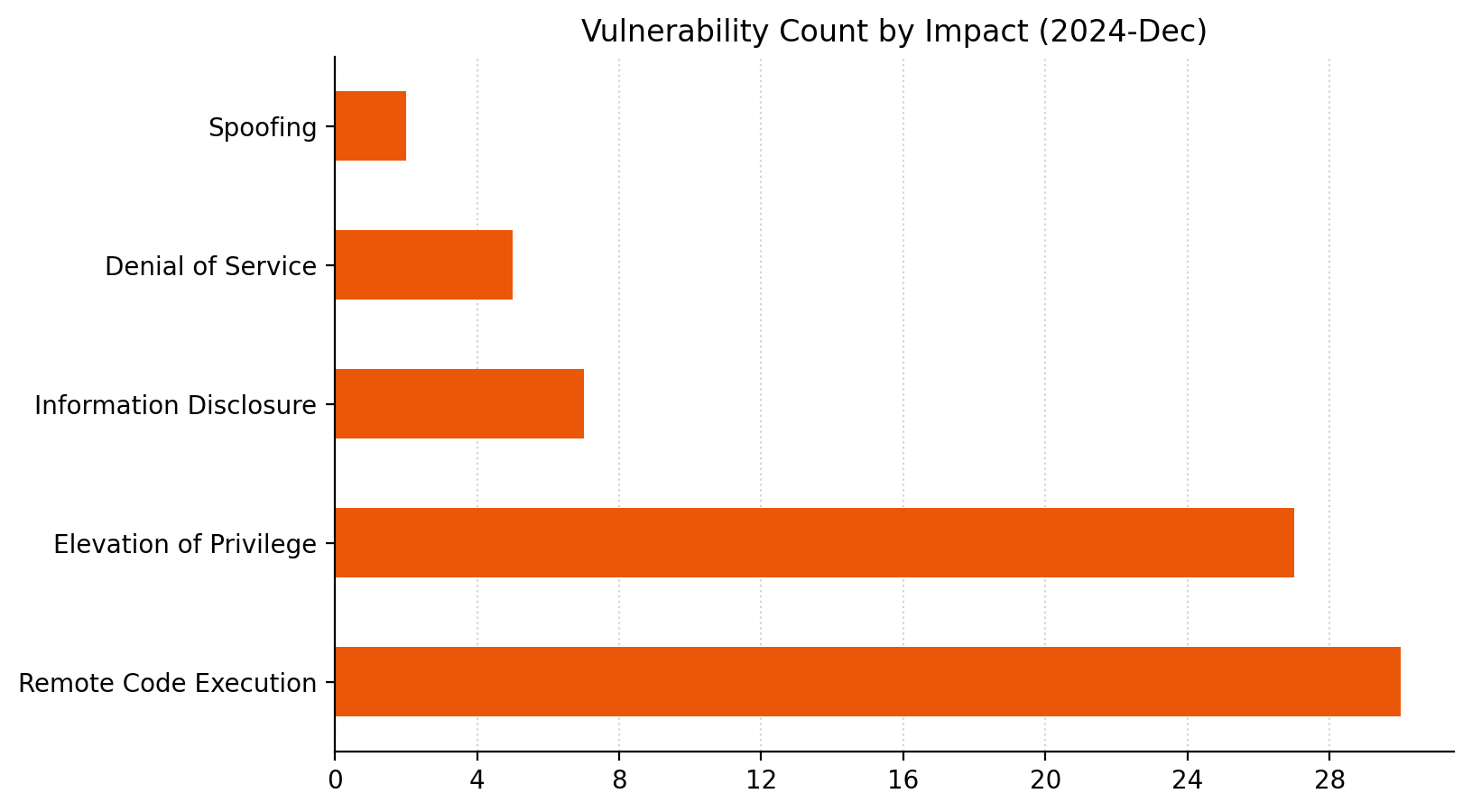
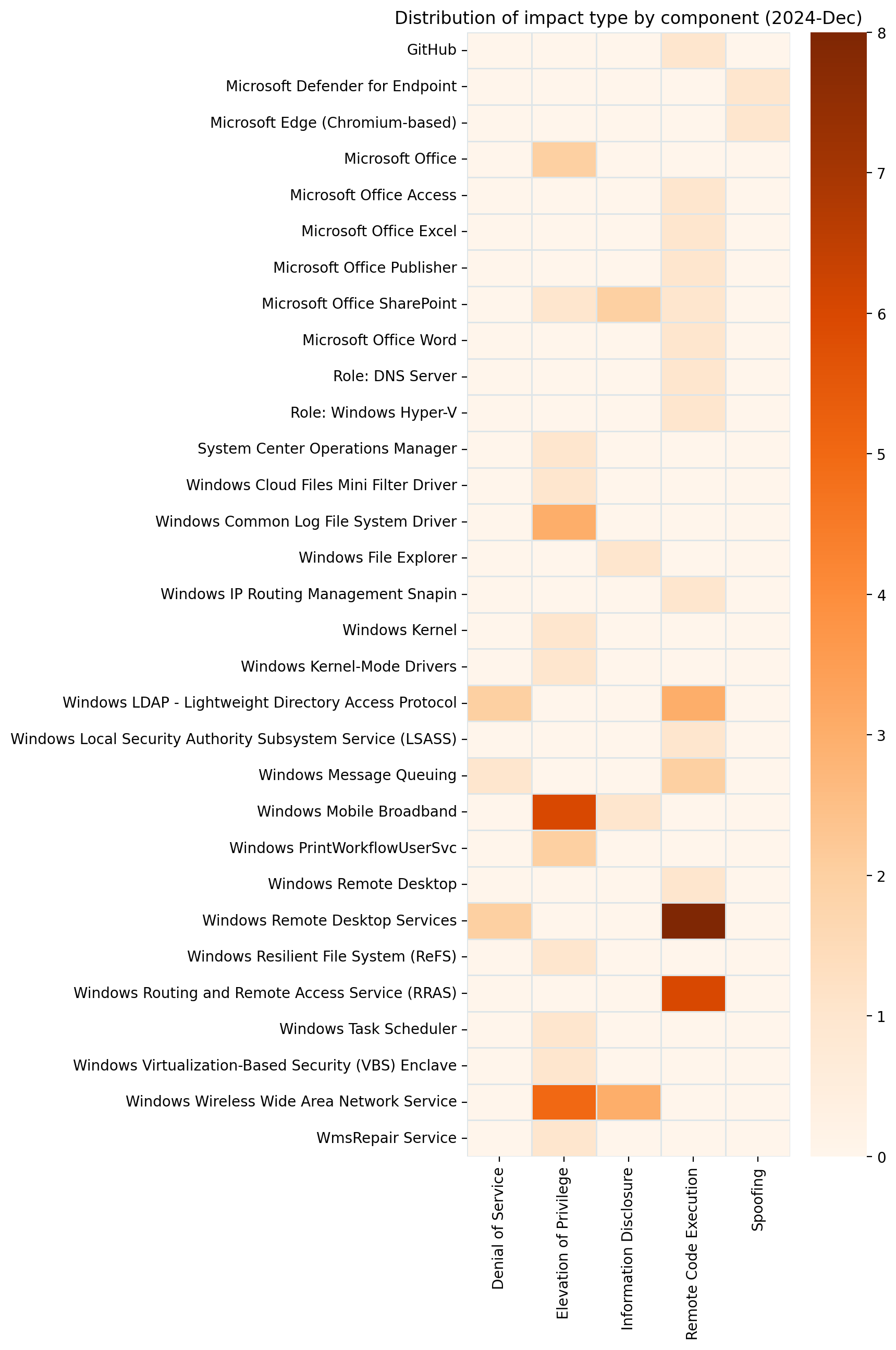
Summary charts

Summary tables
Azure vulnerabilities
|
CVE |
Title |
Exploited? |
Publicly disclosed? |
CVSSv3 base score |
|---|---|---|---|---|
| CVE-2025-59504 |
Azure Monitor Agent Remote Code Execution Vulnerability |
No |
No |
7.3 |
Browser vulnerabilities
|
CVE |
Title |
Exploited? |
Publicly disclosed? |
CVSSv3 base score |
|---|---|---|---|---|
| CVE-2025-12729 |
Chromium: CVE-2025-12729 Inappropriate implementation in Omnibox |
No |
No |
N/A |
| CVE-2025-12728 |
Chromium: CVE-2025-12728 Inappropriate implementation in Omnibox |
No |
No |
N/A |
| CVE-2025-12727 |
Chromium: CVE-2025-12727 Inappropriate implementation in V8 |
No |
No |
N/A |
| CVE-2025-12726 |
Chromium: CVE-2025-12726 Inappropriate implementation in Views. |
No |
No |
N/A |
| CVE-2025-12725 |
Chromium: CVE-2025-12725 Out of bounds write in WebGPU |
No |
No |
N/A |
Developer Tools vulnerabilities
|
CVE |
Title |
Exploited? |
Publicly disclosed? |
CVSSv3 base score |
|---|---|---|---|---|
| CVE-2025-62222 |
Agentic AI and Visual Studio Code Remote Code Execution Vulnerability |
No |
No |
8.8 |
| CVE-2025-62449 |
Microsoft Visual Studio Code CoPilot Chat Extension Security Feature Bypass Vulnerability |
No |
No |
6.8 |
| CVE-2025-62214 |
Visual Studio Remote Code Execution Vulnerability |
No |
No |
6.7 |
| CVE-2025-62453 |
GitHub Copilot and Visual Studio Code Security Feature Bypass Vulnerability |
No |
No |
5 |
Mariner Open Source Software vulnerabilities
|
CVE |
Title |
Exploited? |
Publicly disclosed? |
CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-25621 |
containerd affected by a local privilege escalation via wide permissions on CRI directory |
No |
No |
7.3 |
| CVE-2025-10966 |
missing SFTP host verification with wolfSSH |
No |
No |
6.8 |
| CVE-2025-64329 |
containerd CRI server: Host memory exhaustion through Attach goroutine leak |
No |
No |
N/A |
Microsoft Dynamics vulnerabilities
|
CVE |
Title |
Exploited? |
Publicly disclosed? |
CVSSv3 base score |
|---|---|---|---|---|
| CVE-2025-62210 |
Dynamics 365 Field Service (online) Spoofing Vulnerability |
No |
No |
8.7 |
| CVE-2025-62211 |
Dynamics 365 Field Service (online) Spoofing Vulnerability |
No |
No |
8.7 |
| CVE-2025-62206 |
Microsoft Dynamics 365 (On-Premises) Information Disclosure Vulnerability |
No |
No |
6.5 |
Microsoft Office vulnerabilities
|
CVE |
Title |
Exploited? |
Publicly disclosed? |
CVSSv3 base score |
|---|---|---|---|---|
| CVE-2025-62204 |
Microsoft SharePoint Remote Code Execution Vulnerability |
No |
No |
8 |
| CVE-2025-62199 |
Microsoft Office Remote Code Execution Vulnerability |
No |
No |
7.8 |
| CVE-2025-62216 |
Microsoft Office Remote Code Execution Vulnerability |
No |
No |
7.8 |
| CVE-2025-62205 |
Microsoft Office Remote Code Execution Vulnerability |
No |
No |
7.8 |
| CVE-2025-60727 |
Microsoft Excel Remote Code Execution Vulnerability |
No |
No |
7.8 |
| CVE-2025-62200 |
Microsoft Excel Remote Code Execution Vulnerability |
No |
No |
7.8 |
| CVE-2025-62201 |
Microsoft Excel Remote Code Execution Vulnerability |
No |
No |
7.8 |
| CVE-2025-62203 |
Microsoft Excel Remote Code Execution Vulnerability |
No |
No |
7.8 |
| CVE-2025-60726 |
Microsoft Excel Information Disclosure Vulnerability |
No |
No |
7.1 |
| CVE-2025-62202 |
Microsoft Excel Information Disclosure Vulnerability |
No |
No |
7.1 |
| CVE-2025-60722 |
Microsoft OneDrive for Android Elevation of Privilege Vulnerability |
No |
No |
6.5 |
| CVE-2025-59240 |
Microsoft Excel Information Disclosure Vulnerability |
No |
No |
5.5 |
| CVE-2025-60728 |
Microsoft Excel Information Disclosure Vulnerability |
No |
No |
4.3 |
Open Source Software vulnerabilities
|
CVE |
Title |
Exploited? |
Publicly disclosed? |
CVSSv3 base score |
|---|---|---|---|---|
| CVE-2025-62220 |
Windows Subsystem for Linux GUI Remote Code Execution Vulnerability |
No |
No |
8.8 |
| CVE-2025-12863 |
Libxml2: namespace use-after-free in xmlsettreedoc() function of libxml2 |
No |
No |
7.5 |
| CVE-2025-64433 |
KubeVirt Arbitrary Container File Read |
No |
No |
6.5 |
| CVE-2025-40107 |
can: hi311x: fix null pointer dereference when resuming from sleep before interface was enabled |
No |
No |
5.5 |
| CVE-2025-60753 |
An issue was discovered in libarchive bsdtar before version 3.8.1 in function apply_substitution in file tar/subst.c when processing crafted -s substitution rules. This can cause unbounded memory allocation and lead to denial of service (Out-of-Memory crash). |
No |
No |
5.5 |
| CVE-2025-12875 |
mruby array.c ary_fill_exec out-of-bounds write |
No |
No |
5.3 |
| CVE-2025-64435 |
KubeVirt VMI Denial-of-Service (DoS) Using Pod Impersonation |
No |
No |
5.3 |
| CVE-2025-64437 |
KubeVirt Isolation Detection Flaw Allows Arbitrary File Permission Changes |
No |
No |
5 |
| CVE-2025-64434 |
KubeVirt Improper TLS Certificate Management Handling Allows API Identity Spoofing |
No |
No |
4.7 |
| CVE-2025-64432 |
KubeVirt Affected by an Authentication Bypass in Kubernetes Aggregation Layer |
No |
No |
4.7 |
| CVE-2025-40109 |
crypto: rng – Ensure set_ent is always present |
No |
No |
4.2 |
| CVE-2025-52881 |
runc: LSM labels can be bypassed with malicious config using dummy procfs files |
No |
No |
N/A |
| CVE-2025-31133 |
runc container escape via “masked path” abuse due to mount race conditions |
No |
No |
N/A |
| CVE-2025-52565 |
container escape due to /dev/console mount and related races |
No |
No |
N/A |
| CVE-2025-64436 |
KubeVirt Excessive Role Permissions Could Enable Unauthorized VMI Migrations Between Nodes |
No |
No |
N/A |
Other vulnerabilities
|
CVE |
Title |
Exploited? |
Publicly disclosed? |
CVSSv3 base score |
|---|---|---|---|---|
| CVE-2025-30398 |
Nuance PowerScribe 360 Information Disclosure Vulnerability |
No |
No |
8.1 |
SQL Server vulnerabilities
|
CVE |
Title |
Exploited? |
Publicly disclosed? |
CVSSv3 base score |
|---|---|---|---|---|
| CVE-2025-59499 |
Microsoft SQL Server Elevation of Privilege Vulnerability |
No |
No |
8.8 |
System Center vulnerabilities
|
CVE |
Title |
Exploited? |
Publicly disclosed? |
CVSSv3 base score |
|---|---|---|---|---|
| CVE-2025-47179 |
Configuration Manager Elevation of Privilege Vulnerability |
No |
No |
6.7 |
Windows vulnerabilities
|
CVE |
Title |
Exploited? |
Publicly disclosed? |
CVSSv3 base score |
|---|---|---|---|---|
| CVE-2025-59511 |
Windows WLAN Service Elevation of Privilege Vulnerability |
No |
No |
7.8 |
| CVE-2025-60713 |
Windows Routing and Remote Access Service (RRAS) Elevation of Privilege Vulnerability |
No |
No |
7.8 |
| CVE-2025-60718 |
Windows Administrator Protection Elevation of Privilege Vulnerability |
No |
No |
7.8 |
| CVE-2025-60721 |
Windows Administrator Protection Elevation of Privilege Vulnerability |
No |
No |
7.8 |
| CVE-2025-60707 |
Multimedia Class Scheduler Service (MMCSS) Driver Elevation of Privilege Vulnerability |
No |
No |
7.8 |
| CVE-2025-60710 |
Host Process for Windows Tasks Elevation of Privilege Vulnerability |
No |
No |
7.8 |
| CVE-2025-59507 |
Windows Speech Runtime Elevation of Privilege Vulnerability |
No |
No |
7 |
| CVE-2025-59508 |
Windows Speech Recognition Elevation of Privilege Vulnerability |
No |
No |
7 |
| CVE-2025-62215 |
Windows Kernel Elevation of Privilege Vulnerability |
Yes |
No |
7 |
| CVE-2025-59515 |
Windows Broadcast DVR User Service Elevation of Privilege Vulnerability |
No |
No |
7 |
| CVE-2025-60717 |
Windows Broadcast DVR User Service Elevation of Privilege Vulnerability |
No |
No |
7 |
| CVE-2025-62218 |
Microsoft Wireless Provisioning System Elevation of Privilege Vulnerability |
No |
No |
7 |
| CVE-2025-62219 |
Microsoft Wireless Provisioning System Elevation of Privilege Vulnerability |
No |
No |
7 |
| CVE-2025-60716 |
DirectX Graphics Kernel Elevation of Privilege Vulnerability |
No |
No |
7 |
| CVE-2025-60708 |
Storvsp.sys Driver Denial of Service Vulnerability |
No |
No |
6.5 |
| CVE-2025-60723 |
DirectX Graphics Kernel Denial of Service Vulnerability |
No |
No |
6.3 |
| CVE-2025-59509 |
Windows Speech Recognition Information Disclosure Vulnerability |
No |
No |
5.5 |
| CVE-2025-62208 |
Windows License Manager Information Disclosure Vulnerability |
No |
No |
5.5 |
| CVE-2025-62209 |
Windows License Manager Information Disclosure Vulnerability |
No |
No |
5.5 |
| CVE-2025-60706 |
Windows Hyper-V Information Disclosure Vulnerability |
No |
No |
5.5 |
|
GDI+ Remote Code Execution Vulnerability |
Yes |
No |
9.8 |
Windows ESU vulnerabilities
|
CVE |
Title |
Exploited? |
Publicly disclosed? |
CVSSv3 base score |
|---|---|---|---|---|
| CVE-2025-62452 |
Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability |
No |
No |
8 |
| CVE-2025-60715 |
Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability |
No |
No |
8 |
| CVE-2025-60720 |
Windows Transport Driver Interface (TDI) Translation Driver Elevation of Privilege Vulnerability |
No |
No |
7.8 |
| CVE-2025-59505 |
Windows Smart Card Reader Elevation of Privilege Vulnerability |
No |
No |
7.8 |
| CVE-2025-60703 |
Windows Remote Desktop Services Elevation of Privilege Vulnerability |
No |
No |
7.8 |
| CVE-2025-60714 |
Windows OLE Remote Code Execution Vulnerability |
No |
No |
7.8 |
| CVE-2025-60709 |
Windows Common Log File System Driver Elevation of Privilege Vulnerability |
No |
No |
7.8 |
| CVE-2025-60705 |
Windows Client-Side Caching Elevation of Privilege Vulnerability |
No |
No |
7.8 |
| CVE-2025-59514 |
Microsoft Streaming Service Proxy Elevation of Privilege Vulnerability |
No |
No |
7.8 |
| CVE-2025-59512 |
Customer Experience Improvement Program (CEIP) Elevation of Privilege Vulnerability |
No |
No |
7.8 |
| CVE-2025-60704 |
Windows Kerberos Elevation of Privilege Vulnerability |
No |
No |
7.5 |
| CVE-2025-60719 |
Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability |
No |
No |
7 |
| CVE-2025-62217 |
Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability |
No |
No |
7 |
| CVE-2025-62213 |
Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability |
No |
No |
7 |
| CVE-2025-59506 |
DirectX Graphics Kernel Elevation of Privilege Vulnerability |
No |
No |
7 |
| CVE-2025-59510 |
Windows Routing and Remote Access Service (RRAS) Denial of Service Vulnerability |
No |
No |
5.5 |
| CVE-2025-59513 |
Windows Bluetooth RFCOM Protocol Driver Information Disclosure Vulnerability |
No |
No |
5.5 |
|
GDI+ Remote Code Execution Vulnerability |
Yes |
No |
9.8 |
Windows Microsoft Office ESU vulnerabilities
|
CVE |
Title |
Exploited? |
Publicly disclosed? |
CVSSv3 base score |
|---|---|---|---|---|
| CVE-2025-60724 |
GDI+ Remote Code Execution Vulnerability |
No |
No |
9.8 |
Updates
- 2025-11-11: clarified the description of CVE-2025-62214.