Post Syndicated from Михаил Ангелов original https://www.toest.bg/nauchni-novini-paleontologiya-ledeni-ribi/
Палеонтологични открития

Праисторията на планетата ни е изключително богата и вълнуваща. За съжаление, големи участъци от нея все още не са ни известни. Две скорошни открития запълват частици от този пъзел и ни позволяват да надникнем към отдавна отминали времена.
Креда е последният период на мезозойската ера и е с продължителност около 70 млн. години. Преходът между долна и горна креда преди 99 млн. години е период на големи промени в климата на планетата, което се отразява на популациите на динозаврите. Поради повишаването на нивата на въглероден диоксид в атмосферата, глобалната температура и нивата на световните океани се повишават, което води до намаляване на обитаемите области. В този период гигантските тревопасни завроподи с дълги шии в сегашна Северна Америка започват да изчезват, докато популациите на по-малките орнитоподи се увеличават.
Именно за ранен орнитопод е считан от откривателите си динозавърът Iani smithi, наречен на двуликия бог на промяната Янус. Добре запазеният скелет е открит в щата Юта. Особено ценно е наличието на почти пълен череп, което е помогнало на палеонтолозите да разберат повече за вида и да го причислят към подгрупата на орнитоподите Rhabdodontomorpha най-вече заради характерните за тях широки зъби и някои особености на челюстта. Това прави находката рядка за Северна Америка, тъй като подобни животни са се срещали предимно в Европа.
В най-южната част на Чили учените се натъкват на уникална находка под формата на фосили от първия по вида си тревопасен динозавър, открит в субантарктическия регион – Gonkoken nanoi. Името му е взето от езика на теуелче – коренните жители на Патагония: gon означава „сходен, подобен“, а koken – „дива патица“ или „лебед“. Дължината на динозавъра е била около четири метра и е можел да се изправя на задните си крака, за да се храни с по-висока растителност.
По останките учените са определили, че е бил много сходен с широко разпространената група на хадрозаврите (известни като динозаври с „патешки човки“), но не спада към нея. Засега хипотезата е, че за разлика от по-северните си роднини от Патагония, той е потомък на общ предшественик, от който са произлезли и хадрозаврите. Най-вероятно този прото-Gonkoken е мигрирал рано в Южна Америка, като е достигнал най-южните ѝ части, докъдето същинските хадрозаври не са успели. Откритието повдига въпроса дали не трябва да се преразгледат и другите фосили от района, защото може да се окаже, че не са типични хадрозаври, а са по-близки роднини на Gonkoken.
След средата на креда броят на тези тревопасни се увеличава бързо и те стават едни от най-усъвършенстваните машини за приемане на растителна храна със стотиците си зъби, способни да мачкат, накъсват и стриват най-различни растения. Хегемонията на гигантите приключва със събитието К–Т, причинено от сблъсъка на астероид със Земята. Глобалните климатични промени, произтекли от него, променят драстично видовия състав на планетата и откриват поле за еволюцията на видове, по-добре адаптирани към новия свят.
Оцеляване в студа
Животът намира своето място дори и в най-екстремните ареали. Около Антарктида живеят риби от разред Бодлоперки, наречени ледени риби заради способността си да оцеляват във вода с температура, достигаща -2°C. Освен че е една от причините за по-ниската температура на водата, Западноветровото течение, опасващо континента, ги е изолирало от останалите океански обитатели. Това им е позволило да запълнят много от свободните екологични ниши и да образуват значително количество отделни видове (предполага се, че са между 130 и 140).
За справяне с околната среда рибите са развили редица адаптации, сред които синтез на „антифризни“ белтъци и големи мускулни влакна. Но ниските температури са станали причина и за загубата на характеристики, които се смятат за общи за всички живи организми – от бактериите до човека. Една от тях е, че когато са изложени на по-високи температури, не отделят специфични протеини, които се синтезират при стрес от околната среда.
Още по-интересна е липсата на функционални червени кръвни телца, които снабдяват с кислород всички останали гръбначни животни. Загубен или драстично намален е и синтезът на хемоглобин, поради което тяхната кръв няма характерния червен цвят, а е безцветна. Тази адаптация е възможна благодарение на факта, че кислородът е много по-разтворим в студена вода и за да се възползват от повишената му концентрация, рибите са развили голямо, бавно биещо сърце и широки кръвоносни съдове.
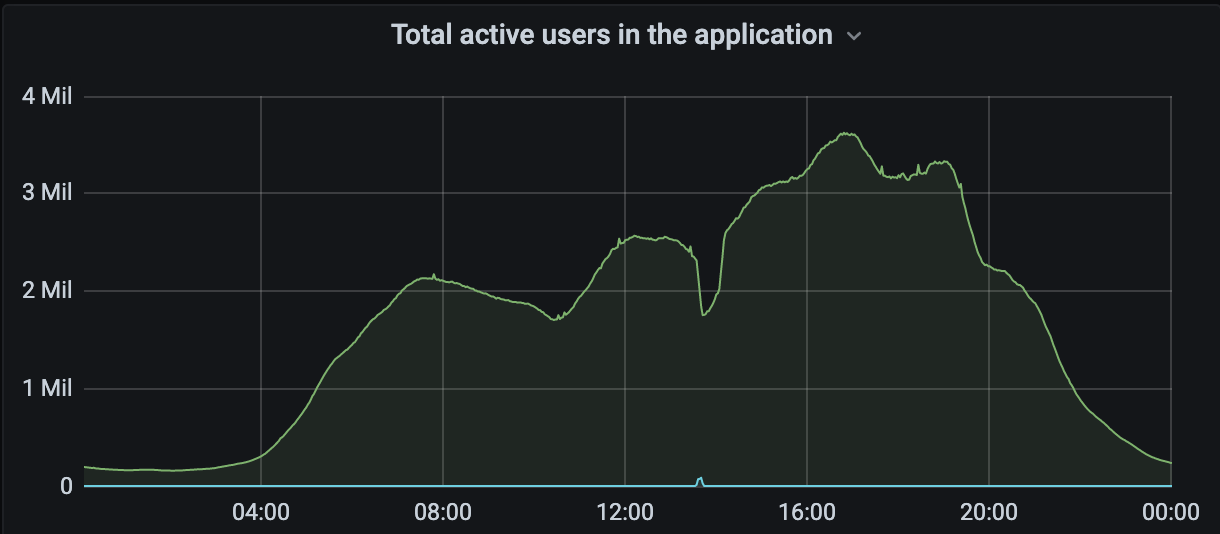
Секвенирането на геномите на 24 вида, част от които с помощта на по-нова технология, позволяваща прочитането на по-дълги участъци ДНК, дава възможност да се вникне във възникването на тези промени и да се определи техният еволюционен път. Според получените данни първите видове са започнали да се формират много по-скоро, отколкото се считаше до момента – около 10,7 млн. години вместо 22 млн., като преди около 5 млн. години е започнало интензивно видообразуване. Това е подкрепено и от климатични данни, сочещи, че в този период температурата в района е паднала, започнало е образуването на лед и са се повишили нивата на кислород.
Оказва се също, че геномът на някои от видовете, които живеят около Антарктида, е почти два пъти по-голям от този на роднините им, обитаващи южните брегове на Южна Америка. Това се дължи основно на намножаването на транспозони – подвижни генетични елементи, които имат свойството да се преместват или копират в генома. Те са основна причина и за промените в два участъка, отговорни за синтеза на хемоглобин при рибите. Възползвайки се от улеснената биоинформатична обработка на данните от новата технология за секвениране, учените са успели да получат информация за гените, намиращи се в тях – при ледените риби те са изчезнали, като са били заменени от транспозони.
Освен за непосредственото разкриване на механизмите на генетичните адаптации при изследваните видове, развитието на технологиите за секвениране ни дава възможност да вникнем много по-добре в еволюцията на обитателите на най-екстремните екологични ниши. Тъй като са тясноспециализирани за живот в такива условия, те са изключително застрашени от глобалните климатични промени, поради което подобни проекти ще са много ценни за проследяването на промените в биоразнообразието в тези региони.
Ново за COVID-19
Макар повечето хора да приемат, че тежките дни на пандемията са преминали, последствията от нея тепърва се разгръщат и ще бъдат оценявани. Научните изследвания продължават и ни дават все по-добро разбиране на самия вирус и на начина, по който взаимодейства с тялото ни.
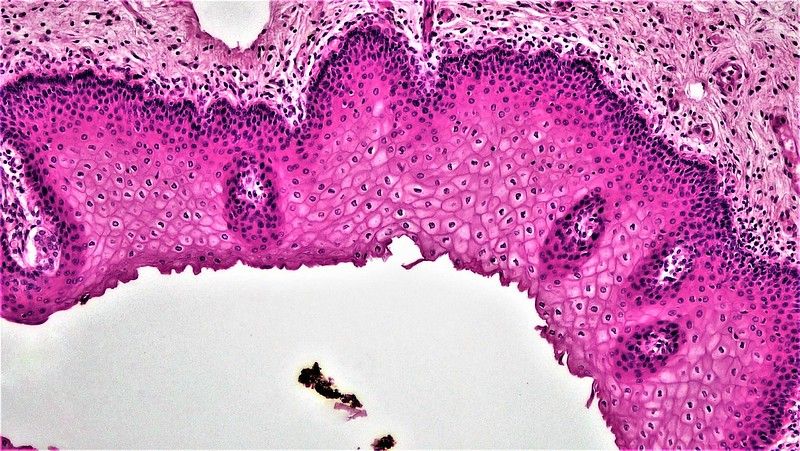
Точният механизъм на проникване на вирусните частици (вириони) на SARS-CoV-2 в клетките все още крие тайни и учените се опитват да разберат как протича този процес. На повърхността си всеки вирион носи между 20 и 40 шипчета (спайкпротеини), които са хомотримери – изградени от три идентични полипептида. С тяхна помощ той се свързва с ACE2 рецепторите, намиращи се по човешките клетки.
Една от хипотезите до момента беше, че поради гъвкавостта на спайкпротеините вирионът ще може да свърже няколко от тях с няколко рецептора по клетките. Друго предположение беше, че тъй като всяко шипче е изградено от три компонента, то ще е много по-ефективно да се свърже с полимер на ACE2 рецептора. По времето, когато тези хипотези бяха предложени, в тяхна подкрепа имаше достатъчно информация, но тя не беше получена по оптимален начин, тъй като наблюденията са правени с пречистени протеини, което не отразява реалното състояние в човешките клетки.
Ново изследване на германски екип дава повече яснота за случващото се по време на инфекция в условия, по-близки до естествените. Учените са използвали метод за микроскопия със суперрезолюция dSTORM (direct stochastic optical reconstruction microscopy), разработен от тях. Използвайки антитела, специфични за ACE2 рецепторите, свързани с багрило, те са определили броя и плътността на рецепторите в няколко линии клетки, стандартно използвани в изследванията с вируса.
Резултатите показват, че рецепторите са слабо разпространени, с плътност около един до два на всеки квадратен микрометър от повърхността на клетъчната мембрана, което се отнася към разстояние между тях от около 500 нанометра – около пет пъти повече от размера на вирусните частици. Това опровергава първата хипотеза, тъй като, щом се закачат за един рецептор, вирионите нямат възможност да стигнат до друг. Наред с това е установено, че ACE2 не образуват полимерни структури както при отсъствието на вириони, така и след свързване на спайкпротеина с тях. По този начин се отхвърля и втората хипотеза.
Комбинирани с откритието, че за инфекция е достатъчно свързването само на един спайкпротеин с един клетъчен рецептор, тези свойства на вируса най-вероятно са част от причините за високата му инфекциозност.
Авторите смятат, че все още няма пълно обяснение за процеса на инфекция със SARS-CoV-2, но се надяват, че откритията им ще помогнат за разработването на нови медикаменти. Във философски аспект резултат от изследването е, че показва колко динамичен процес е науката и колко трудно е да се постигне пълно разбиране, особено на биологични системи.
Наред с високата температура и болките в гърлото, загубата на обоняние и вкус бяха сред характерните черти на заболяването, причинено от първите варианти на вируса. Обикновено обонянието и вкусът се възстановяват след преминаване на по-тежките симптоми, но от ново изследване става ясно, че това може да не е така при немалък процент хора.
След обобщаване на данните от въпросници, попълнени от почти 30 000 възрастни през 2021 г. в САЩ, е установено, че около 60% от отговорилите са загубили обоняние и вкус. Една година по-късно около 24% от тях са имали само частично възстановяване на обонянието, а при 4% загубата е била трайна. Сходни са и данните за вкуса, съответно с 21% и 3%. Открита е и положителна корелация между това колко тежко протича заболяването, вероятността за загуба на обоняние и намаляването на шанса за възстановяването му.
Тъй като двата симптома са свързани, е възможно процентите да не са абсолютно точни поради некоректно съобщаване от анкетираните, но все пак данните са притеснителни. Въпреки че привидно не са сериозни, тези симптоми могат да имат силен ефект върху психическото здраве на пациентите. Не е изключено да доведат до загуба на апетит и тегло, което от своя страна да е причина за възникване на други проблеми.
Тъй като механизмът на загубата на обоняние не е изяснен, няма общоприети начини за терапия, които са клинично доказани. Един от обещаващите методи е трениране с аромати, при който пациентите трябва да подушват определени миризми по няколко пъти дневно. Най-често се използват аромати от различни групи, сред които роза, евкалипт, лимон и карамфил. Методът е много подходящ за прилагане в началото на терапията, защото не е инвазивен и изключително рядко може да доведе до странични реакции. За съжаление, не е универсален и невинаги дава резултат.
Друг експериментален подход е блокадата на ганглион стелатум (част от вегетативната нервна система и намиращ се в основата на врата) с помощта на локални анестетици. Досега процедурата е използвана с различен успех и при други заболявания – посттравматичен стрес, мигрени, невралгии. Нейното приложение е все още ограничено, тъй като ефективността ѝ не е напълно клинично доказана, има описани само отделни случаи и за момента липсва твърдо обяснение как може да повлияе на загубата на обонянието. Това повдига някои съмнения за въвеждането ѝ в рутинната практика поради липсата на клинични изпитвания в контролирани условия и на ясна връзка между терапията и начина ѝ на действие. Още повече, тъй като състоянието на пациентите може да се промени с времето и резултатите се оценяват от самите тях, установяването на ефективността е по-сложно.
Без значение какъв е видът на симптомите, с които се проявява, т.нар. дълъг ковид е факт. Освен преките последствия от него, той може да отключи и нови заболявания, често от неврологично или сърдечносъдово естество. Пациентите с такива симптоми или потенциал за появата им трябва да бъдат наблюдавани с повишено внимание и да получават по-тясно насочена медицинска помощ. Тепърва пред учени и лекари ще бъде поставена нелеката задача да помогнат на голям брой хора, които носят трайния отпечатък от вируса върху здравето си.