Post Syndicated from Sheila Busser original https://aws.amazon.com/blogs/compute/automating-your-workload-deployments-in-aws-local-zones/
This blog post is written by Enrico Liguori, SA – Solutions Builder , WWPS Solution Architecture.
AWS Local Zones are a type of infrastructure deployment that places compute, storage,and other select AWS services close to large population and industry centers.
We now have a total of 32 Local Zones; 15 outside of the US (Bangkok, Buenos Aires, Copenhagen, Delhi, Hamburg, Helsinki, Kolkata, Lagos, Lima, Muscat, Perth, Querétaro, Santiago, Taipei, and Warsaw) and 17 in the US. We will continue to launch Local Zones in 21 metro areas in 18 countries, including Australia, Austria, Belgium, Brazil, Canada, Colombia, Czech Republic, Germany, Greece, India, Kenya, Netherlands, New Zealand, Norway, Philippines, Portugal, South Africa, and Vietnam.
Customers using AWS Local Zones can provision the infrastructure and services needed to host their workloads with the same APIs and tools for automation that they use in the AWS Region, included the AWS Cloud Development Kit (AWS CDK).
The AWS CDK is an open source software development framework to model and provision your cloud application resources using familiar programming languages, including TypeScript, JavaScript, Python, C#, and Java. For the solution in this post, we use Python.
Overview
In this post we demonstrate how to:
- Programmatically enable the Local Zone of your interest.
- Explore the supported APIs to check the types of Amazon Elastic Compute Cloud (Amazon EC2) instances available in a specific Local Zone and get their associated price per hour;
- Deploy a simple WordPress application in the Local Zone through AWS CDK.
Prerequisites
To be able to try the examples provided in this post, you must configure:
Enabling a Local Zone programmatically
To get started with Local Zones, you must first enable the Local Zone that you plan to use in your AWS account. In this tutorial, you can learn how to select the Local Zone that provides the lowest latency to your site and understand how to opt into the Local Zone from the AWS Management Console.
If you prefer to interact with AWS APIs programmatically, then you can enable the Local Zone of your interest by calling the ModifyAvailabilityZoneGroup API through the AWS CLI or one of the supported AWS SDKs.
The following examples show how to opt into the Atlanta Local Zone through the AWS CLI and through the Python SDK:
AWS CLI:
aws ec2 modify-availability-zone-group \ --region us-east-1 \ --group-name us-east-1-atl-1 \ --opt-in-status opted-in
Python SDK:
ec2 = boto3.client('ec2', config=Config(region_name='us-east-1'))
response = ec2.modify_availability_zone_group(
GroupName='us-east-1-atl-1',
OptInStatus='opted-in'
)
The opt in process takes approximately five minutes to complete. After this time, you can confirm the opt in status using the DescribeAvailabilityZones API.
From the AWS CLI, you can check the enabled Local Zones with:
aws ec2 describe-availability-zones --region us-east-1
Or, once again, we can use one of the supported SDKs. Here is an example using Phyton:
ec2 = boto3.client('ec2', config=Config(region_name='us-east-1'))
response = ec2.describe_availability_zones()
In both cases, a JSON object similar to the following, will be returned:
{
"State": "available",
"OptInStatus": "opted-in",
"Messages": [],
"RegionName": "us-east-1",
"ZoneName": "us-east-1-atl-1a",
"ZoneId": "use1-atl1-az1",
"GroupName": "us-east-1-atl-1",
"NetworkBorderGroup": "us-east-1-atl-1",
"ZoneType": "local-zone",
"ParentZoneName": "us-east-1d",
"ParentZoneId": "use1-az4"
}
The OptInStatus confirms that we successful enabled the Atlanta Local Zone and that we can now deploy resources in it.
How to check available EC2 instances in Local Zones
The set of instance types available in a Local Zone might change from one Local Zone to another. This means that before starting deploying resources, it’s a good practice to check which instance types are supported in the Local Zone.
After enabling the Local Zone, we can programmatically check the instance types that are available by using DescribeInstanceTypeOfferings. To use the API with Local Zones, we must pass availability-zone as the value of the LocationType parameter and use a Filter object to select the correct Local Zone that we want to check. The resulting AWS CLI command will look like the following example:
aws ec2 describe-instance-type-offerings --location-type "availability-zone" --filters Name=location,Values=us-east-1-atl-1a --region us-east-1
Using Python SDK:
ec2 = boto3.client('ec2', config=Config(region_name='us-east-1'))
response = ec2.describe_instance_type_offerings(
LocationType='availability-zone',
Filters=[
{
'Name': 'location',
'Values': ['us-east-1-atl-1a']
}
]
)
How to check prices of EC2 instances in Local Zones
EC2 instances and other AWS resources in Local Zones will have different prices than in the parent Region. Check the pricing page for the complete list of pricing options and associated price-per-hour.
To access the pricing list programmatically, we can use the GetProducts API. The API returns the list of pricing options available for the AWS service specified in the ServiceCode parameter. We also recommend defining Filters to restrict the number of results returned. For example, to retrieve the On-Demand pricing list of a T3 Medium instance in Atlanta from the AWS CLI, we can use the following:
aws pricing get-products --format-version aws_v1 --service-code AmazonEC2 --region us-east-1 \ --filters 'Type=TERM_MATCH,Field=instanceType,Value=t3.medium' \ --filters 'Type=TERM_MATCH,Field=location,Value=US East (Atlanta)'
Similarly, with Python SDK we can use the following:
pricing = boto3.client('pricing',config=Config(region_name="us-east-1")) response = pricing.get_products(
ServiceCode='AmazonEC2',
Filters= [
{
"Type": "TERM_MATCH",
"Field": "instanceType",
"Value": "t3.medium"
},
{
"Type": "TERM_MATCH",
"Field": "regionCode",
"Value": "us-east-1-atl-1"
}
],
FormatVersion='aws_v1',
)
Note that the Region specified in the CLI command and in Boto3, is the location of the AWS Price List service API endpoint. This API is available only in us-east-1 and ap-south-1 Regions.
Deploying WordPress in Local Zones using AWS CDK
In this section, we see how to use the AWS CDK and Python to deploy a simple non-production WordPress installation in a Local Zone.
Architecture overview
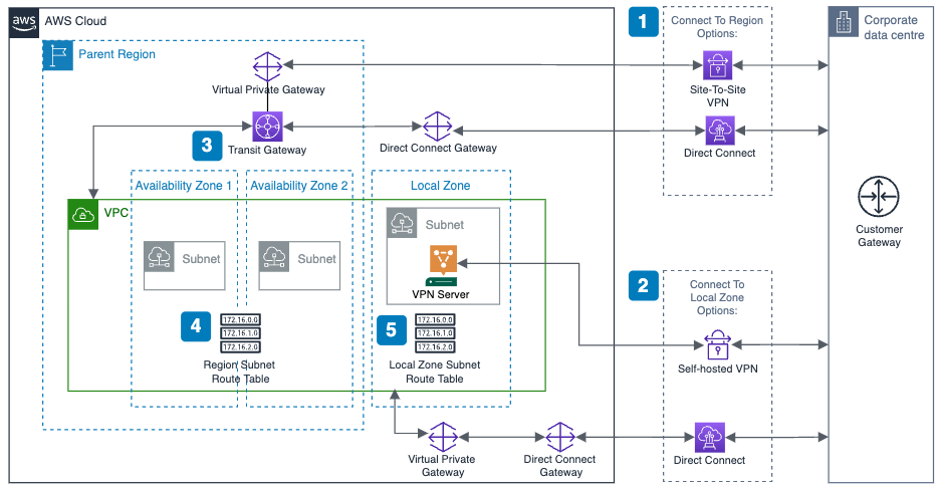
The AWS CDK stack will deploy a new standard Amazon Virtual Private Cloud (Amazon VPC) in the parent Region (us-east-1) that will be extended to the Local Zone. This creates two subnets associated with the Atlanta Local Zone: a public subnet to expose resources on the Internet, and a private subnet to host the application and database layers. Review the AWS public documentation for a definition of public and private subnets in a VPC.
The application architecture is made of the following:
- A front-end in the private subnet where a WordPress application is installed, through a User Data script, in a type T3 medium EC2 instance.
- A back-end in the private subnet where MySQL database is installed, through a User Data script, in a type T3 medium EC2 instance.
- An Application Load Balancer (ALB) in the public subnet that will act as the entry point for the application.
- A NAT instance to allow resources in the private subnet to initiate traffic to the Internet.
Clone the sample code from the AWS CDK examples repository
We can clone the AWS CDK code hosted on GitHub with:
$ git clone https://github.com/aws-samples/aws-cdk-examples.git
Then navigate to the directory aws-cdk-examples/python/vpc-ec2-local-zones using the following:
$ cd aws-cdk-examples/python/vpc-ec2-local-zones
Before starting the provisioning, let’s look at the code in the following sections.
Networking infrastructure
The networking infrastructure is usually the first building block that we must define. In AWS CDK, this can be done using the VPC construct:
import aws_cdk.aws_ec2 as ec2 vpc = ec2.Vpc( self, "Vpc", cidr=”172.31.100.0/24”, subnet_configuration=[ ec2.SubnetConfiguration( name = 'Public-Subnet', subnet_type = ec2.SubnetType.PUBLIC, cidr_mask = 26, ), ec2.SubnetConfiguration( name = 'Private-Subnet', subnet_type = ec2.SubnetType.PRIVATE_ISOLATED, cidr_mask = 26, ), ] )
Together with the VPC CIDR (i.e. 172.31.100.0/24), we define also the subnets configuration through the subnet_configuration parameter.
Note that in the subnet definitions above there is no specification of the Availability Zone or Local Zone that we want to associate them with. We can define this setting at the VPC level, overwriting the availability_zones method as shown here:
@property def availability_zones(self): return [“us-east-1-atl-1a”]
As an alternative, you can use a Local Zone Name as the value of the availability_zones parameter in each Subnet definition. For a complete list of Local Zone Names, check out the Zone Names on the Local Zones Locations page.
Specifying ec2.SubnetType.PUBLIC in the subnet_type parameter, AWS CDK automatically creates an Internet Gateway (IGW) associated with our VPC and a default route in its routing table pointing to the IGW. With this setup, the Internet traffic will go directly to the IGW in the Local Zone without going through the parent AWS Region. For other connectivity options, check the AWS Local Zone User Guide.
The last piece of our networking infrastructure is a self-managed NAT instance. This will allow instances in the private subnet to communicate with services outside of the VPC and simultaneously prevent them from receiving unsolicited connection requests.
We can implement the best practices for NAT instances included in the AWS public documentation using a combination of parameters of the Instance construct, as shown here:
nat = ec2.Instance(self, "NATInstanceInLZ", vpc=vpc, security_group=self.create_nat_SG(vpc), instance_type=ec2.InstanceType.of(ec2.InstanceClass.T3, ec2.InstanceSize.MEDIUM), machine_image=ec2.MachineImage.latest_amazon_linux(), user_data=ec2.UserData.custom(user_data), vpc_subnets=ec2.SubnetSelection(availability_zones=[“us-east-1-atl-1a”], subnet_type=ec2.SubnetType.PUBLIC), source_dest_check=False )
In the previous code example, we specify the following as parameters:
- vpc – the VPC object created before.
- security group – the Security Group containing the rules to allow HTTP and HTTPS traffic. The Security Group is created in
create_nat_SGfunction provided in the code that we copied from the repository. - instance_type – the instance type, in our case a T3 Medium.
- user_data – it contains the required OS configuration for the NAT instance that will be performed at instance start up.
- vpc_subnets – the public subnet.
- source_dest_check – False to disable the source/destination check.
The final required step is to update the route table of the private subnet with the following:
priv_subnet.add_route("DefRouteToNAT",
router_id=nat_instance.instance_id,
router_type=ec2.RouterType.INSTANCE,
destination_cidr_block="0.0.0.0/0",
enables_internet_connectivity=True)
The application stack
The other resources, including the front-end instance managed by AutoScaling, the back-end instance, and ALB are deployed using the standard AWS CDK constructs. Note that the ALB service is only available in some Local Zones. If you plan to use a Local Zone where ALB isn’t supported, then you must deploy a load balancer on a self-managed EC2 instance, or use a load balancer available in AWS Marketplace.
Stack deployment
Next, let’s go through the AWS CDK bootstrapping process. This is required only for the first time that we use AWS CDK in a specific AWS environment (an AWS environment is a combination of an AWS account and Region).
$ cdk bootstrap
Now we can deploy the stack with the following:
$ cdk deploy
After the deployment is completed, we can connect to the application with a browser using the URL returned in the output of the cdk deploy command:
The WordPress install wizard will be displayed in the browser, thereby confirming that the deployment worked as expected:
Note that in this post we use the Local Zone in Atlanta. Therefore, we must deploy the stack in its parent Region, US East (N. Virginia). To select the Region used by the stack, configure the AWS CLI default profile.
Cleanup
To terminate the resources that we created in this post, you can simply run the following:
$ cdk destroy
Conclusion
In this post, we demonstrated how to interact programmatically with the different AWS APIs available for Local Zones. Furthermore, we deployed a simple WordPress application in the Atlanta Local Zone after analyzing the AWS CDK code used for the deployment.
We encourage you to try the examples provided in this post and get familiar with the programmatic configuration and deployment of resources in a Local Zone.