Post Syndicated from Borja Prado Miguelez original https://aws.amazon.com/blogs/devops/standardizing-cicd-pipelines-net-web-applications-aws-service-catalog/
As companies implement DevOps practices, standardizing the deployment of continuous integration and continuous deployment (CI/CD) pipelines is increasingly important. Your developer team may not have the ability or time to create your own CI/CD pipelines and processes from scratch for each new project. Additionally, creating a standardized DevOps process can help your entire company ensure that all development teams are following security and governance best practices.
Another challenge that large enterprise and small organization IT departments deal with is managing their software portfolio. This becomes even harder in agile scenarios working with mobile and web applications where you need to not only provision the cloud resources for hosting the application, but also have a proper DevOps process in place.
Having a standardized portfolio of products for your development teams enables you to provision the infrastructure resources needed to create development environments, and helps reduce the operation overhead and accelerate the overall development process.
This post shows you how to provide your end-users a catalog of resources with all the functionality a development team needs to check in code and run it in a highly scalable load balanced cloud compute environment.
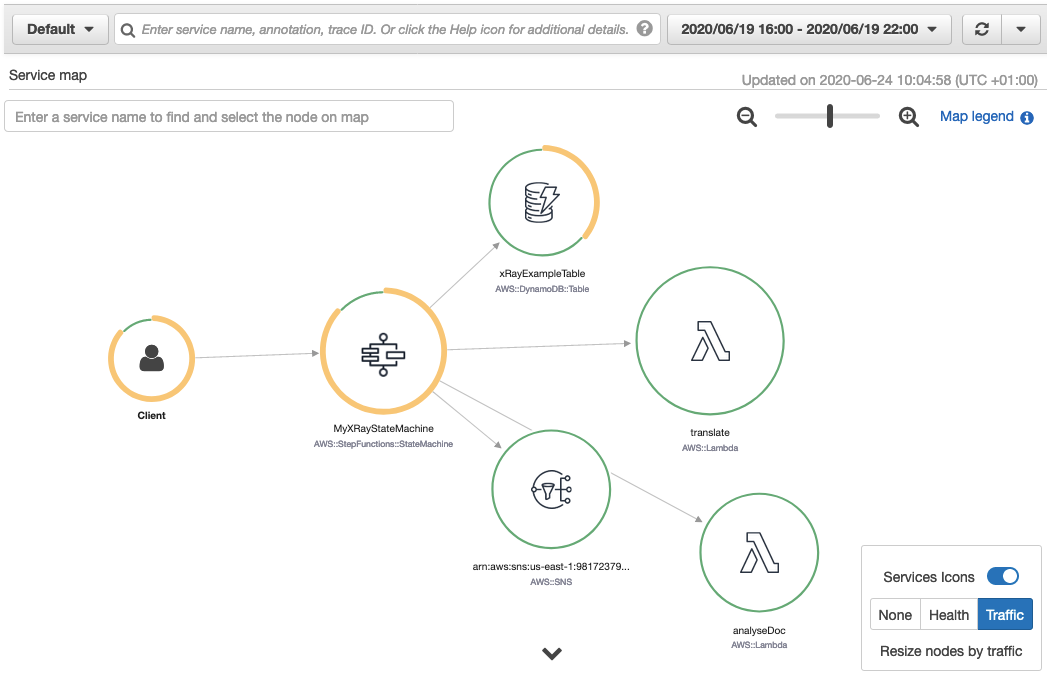
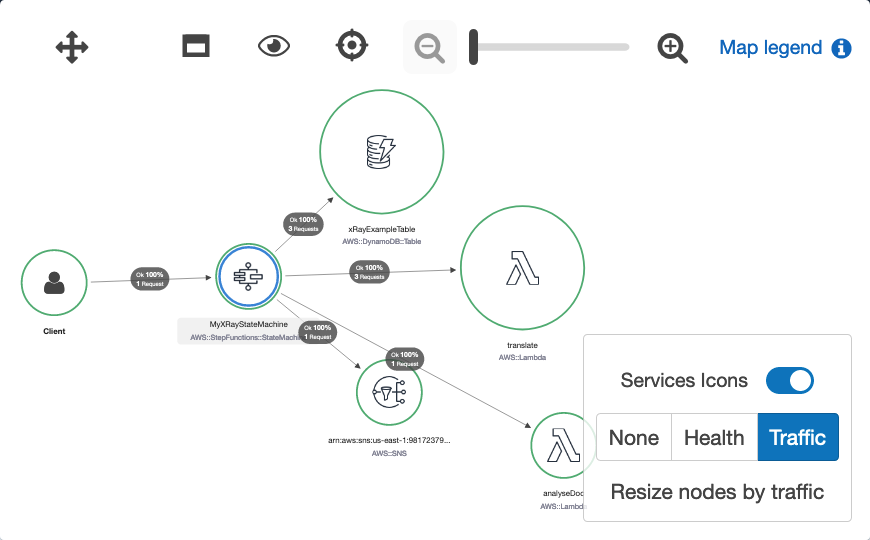
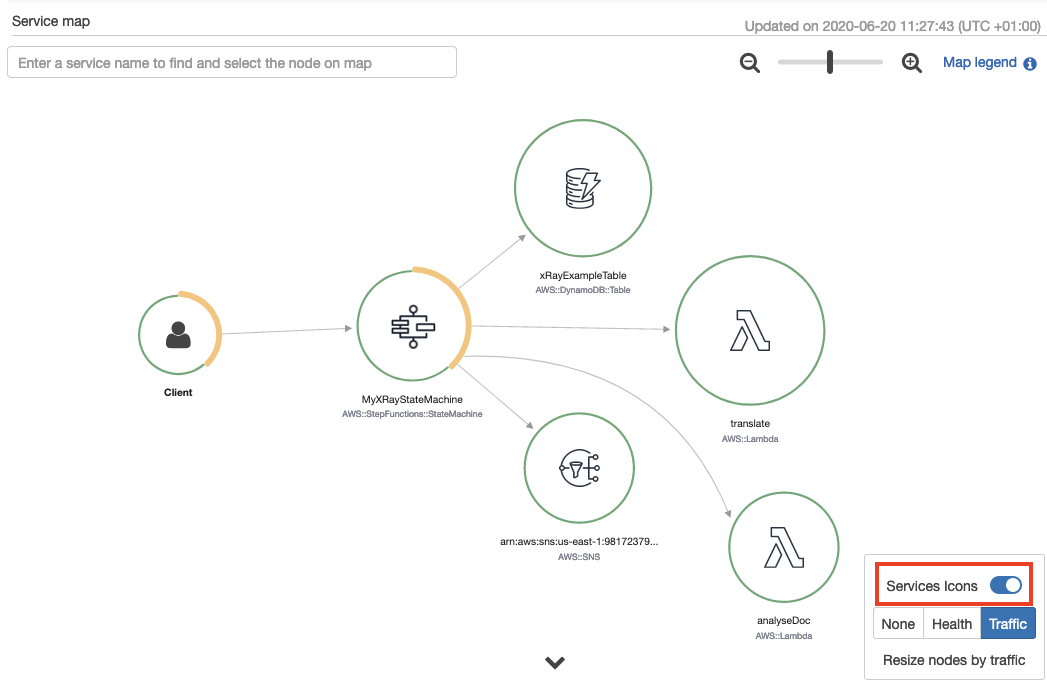
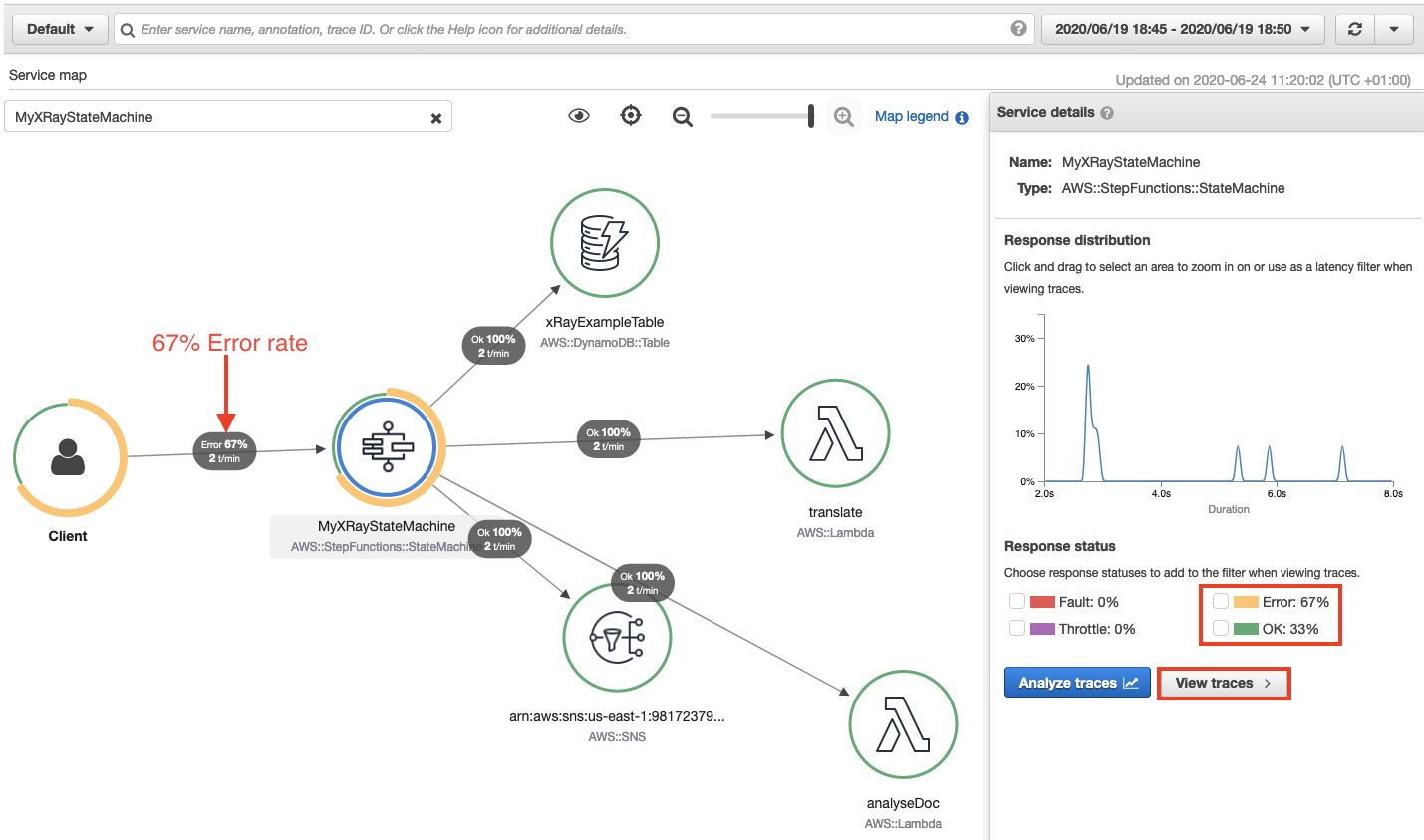
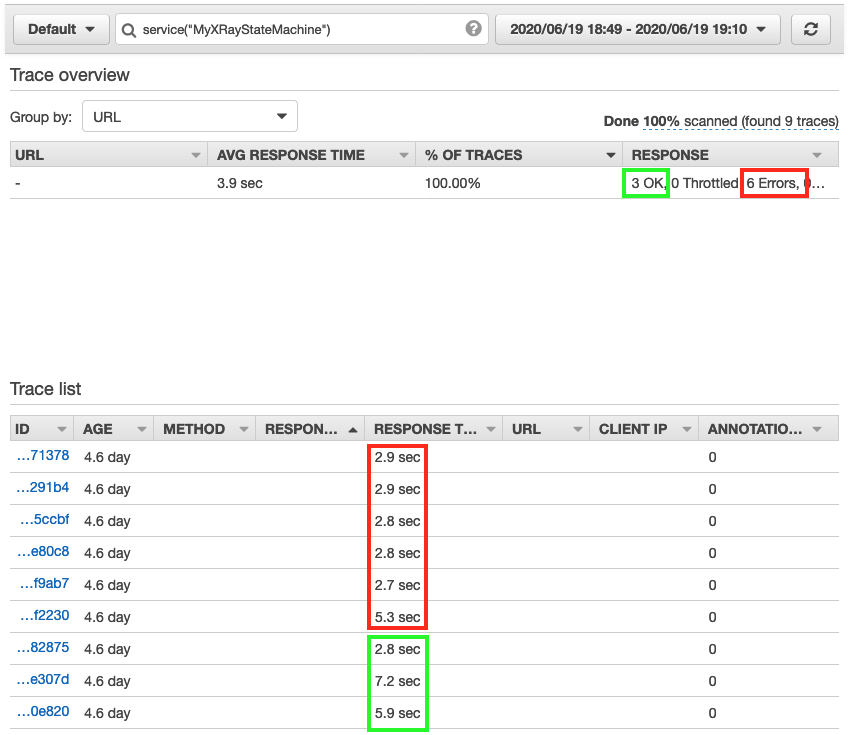
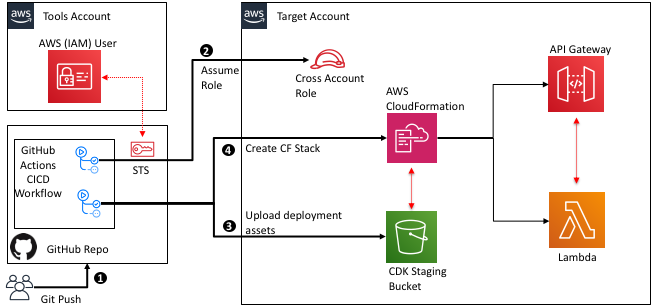
We use AWS Service Catalog to provision a cloud-based AWS Cloud9 IDE, a CI/CD pipeline using AWS CodePipeline, and the AWS Elastic Beanstalk compute service to run the website. AWS Service Catalog allows organizations to keep control of the services and products that can be provisioned across the organization’s AWS account, and there’s an effective software delivery process in place by using CodePipeline to orchestrate the application deployment. The following diagram illustrates this architecture.

You can find all the templates we use in this post on the AWS Service Catalog Elastic Beanstalk Reference architecture GitHub repo.
Provisioning the AWS Service Catalog portfolio
To get started, you must provision the AWS Service Catalog portfolio with AWS CloudFormation.
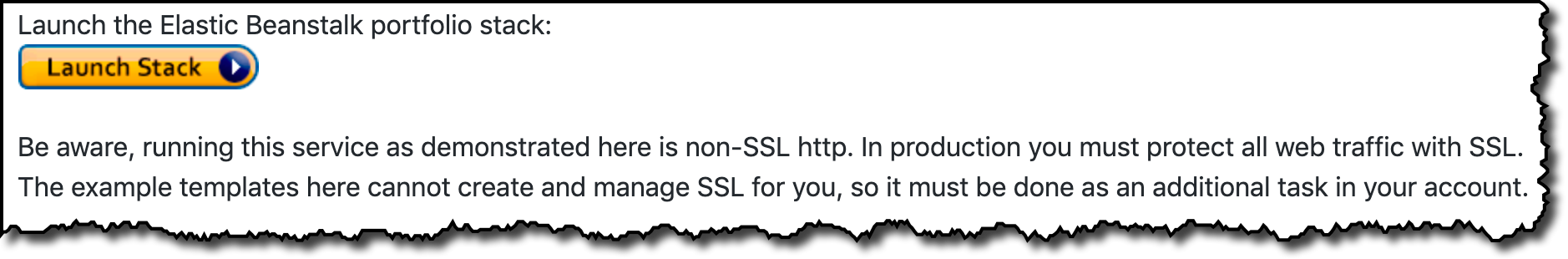
- Choose Launch Stack, which creates the AWS Service Catalog portfolio in your AWS account.

- If you’re signed into AWS as an AWS Identity and Access Management (IAM) role, add your role name in the
LinkedRole1parameter. - Continue through the stack launch screens using the defaults and choosing Next.
- Select the acknowledgements in the Capabilities box on the third screen.
When the stack is complete, a top-level CloudFormation stack with the default name SC-RA-Beanstalk-Portfolio, which contains five nested stacks, has created the AWS Service Catalog products with the services the development team needs to implement a CI/CD pipeline and host the web application. This AWS Service Catalog reference architecture provisions the AWS Service Catalog products needed to set up the DevOps pipeline and the application environment.

When the portfolio has been created, you have completed the administrator setup. As an end-user (any roles you added to the LinkedRole1 or LinkedRole2 parameters), you can access the portfolio section on the AWS Service Catalog console and review the product list, which now includes the AWS Cloud9 IDE, Elastic Beanstalk application, and CodePipeline project that we will use for continuous delivery.

On the AWS Service Catalog administrator section, inside the Elastic Beanstalk reference architecture portfolio, we can add and remove groups, roles, and users by choosing Add groups, roles, users on the Group, roles, and users tab. This lets us enable developers or other users to deploy the products from this portfolio.

Solution overview
The rest of this post walks you through how to provision the resources you need for CI/CD and web application deployment. You complete the following steps:
- Deploy the CI/CD pipeline.
- Provision the AWS Cloud9 IDE.
- Create the Elastic Beanstalk environment.
Deploying the CI/CD pipeline
The first product you need is the CI/CD pipeline, which manages the code and deployment process.
- Sign in to the AWS Service Catalog console in the same Region where you launched the CloudFormation stack earlier.
- On the Products list page, locate the CodePipeline product you created earlier.

- Choose Launch product.
You now provision the CI/CI pipeline. For this post, we use some name examples for the pipeline name, Elastic Beanstalk application name, and code repository, which you can of course modify.
- Enter a name for the provisioned Codepipeline product.
- Select the Windows version and click Next.
- For the application and repository name, enter
dotnetapp. - Leave all other settings at their default and click Next.
- Choose Launch to start the provisioning of the CodePipeline product.
When you’re finished, the provisioned pipeline should appear on the Provisioned products list.

- Copy the
CloneUrlHttpoutput to use in a later step.
You now have the CI/CD pipeline ready, with the code repository and the continuous integration service that compiles the code, runs tests, and generates the software bundle stored in Amazon Simple Storage Service (Amazon S3) ready to be deployed. The following diagram illustrates this architecture.

When the Elastic Beanstalk environment is provisioned, the deploy stage takes care of deploying the bundle application stored in Amazon S3, so the DevOps pipeline takes care of the full software delivery as shown in the earlier architecture diagram.
The Region we use should support the WINDOWS_SERVER_2019_CONTAINER build image that AWS CodeBuild uses. You can modify the environment type or create a custom one by editing the CloudFormation template used for the CodePipeline for Windows.
Provisioning the AWS Cloud9 IDE
To show the full lifecycle of the deployment of a web application with Elastic Beanstalk, we use a .NET web application, but this reference architecture also supports Linux. To provision an AWS Cloud9 environment, complete the following steps:
- From the AWS Service Catalog product list, choose the AWS Cloud9 IDE.
- Click Launch product.
- Enter a name for the provisioned Cloud9 product and click Next.
- Enter an EnvironmentName and select the InstanceType.
- Set LinkedRepoPath to
/dotnetapp. - For LinkedRepoCloneUrl, enter the
CloneUrlHttpfrom the previous step. - Leave the default parameters for tagOptions and Notifications, and click Launch.

Now we download a sample ASP.NET MVC application in the AWS Cloud9 IDE, move it under the folder we specified in the previous step, and push the code.
- Open the IDE with the
Cloud9Urllink from AWS Service Catalog output. - Get the sample .NET web application and move it under the
dotnetapp. See the following code: -
cp -R aws-service-catalog-reference-architectures/labs/SampleDotNetApplication/* dotnetapp/
- Check in to the sample application to the CodeCommit repo:
-
cd dotnetapp git add --all git commit -m "initial commit" git push
Now that we have committed the application to the code repository, it’s time to review the DevOps pipeline.
- On the CodePipeline console, choose Pipelines.
You should see the pipeline ElasticBeanstalk-ProductPipeline-dotnetapp running.

- Wait until the three pipeline stages are complete, this may take several minutes.
The code commitment and web application build stages are successful, but the code deployment stage fails because we haven’t provisioned the Elastic Beanstalk environment yet.
If you want to deploy your own sample or custom ASP.NET web application, CodeBuild requires the build specification file buildspec-build-dotnet.yml for the .NET Framework, which is located under the elasticbeanstalk/codepipeline folder in the GitHub repo. See the following example code:
version: 0.2
env:
variables:
DOTNET_FRAMEWORK: 4.6.1
phases:
build:
commands:
- nuget restore
- msbuild /p:TargetFrameworkVersion=v$env:DOTNET_FRAMEWORK /p:Configuration=Release /p:DeployIisAppPath="Default Web Site" /t:Package
- dir obj\Release\Package
artifacts:
files:
- 'obj/**/*'
- 'codepipeline/*'Creating the Elastic Beanstalk environment
Finally, it’s time to provision the hosting system, an Elastic Beanstalk Windows-based environment, where the .NET sample web application runs. For this, we follow the same approach from the previous steps and provision the Elastic Beanstalk AWS Service Catalog product.
- On the AWS Service Catalog console, on the Product list page, choose the Elastic Beanstalk application product.
- Choose Launch product.
- Enter an environment name and click Next.
- Enter the application name.
- Enter the S3Bucket and S3SourceBundle that were generated (you can retrieve them from the Amazon S3 console).
- Set the SolutionStackName to
64bit Windows Server Core 2019 v2.5.8 running IIS 10.0. Follow this link for up to date platform names. 
- Launch the product.
- To verify that you followed the steps correctly, review that the provisioned products are all available (AWS Cloud9 IDE, Elastic Beanstalk CodePipeline project, and Elastic Beanstalk application) and the recently created Elastic Beanstalk environment is healthy.
As in the previous step, if you’re planning to deploy your own sample or custom ASP.NET web application, AWS CodeDeploy requires the deploy specification file buildspec-deploy-dotnet.yml for the .NET Framework, which should be located under the codepipeline folder in the GitHub repo. See the following code:
version: 0.2
phases:
pre_build:
commands:
- echo application deploy started on `date`
- ls -l
- ls -l obj/Release/Package
- aws s3 cp ./obj/Release/Package/SampleWebApplication.zip s3://$ARTIFACT_BUCKET/$EB_APPLICATION_NAME-$CODEBUILD_BUILD_NUMBER.zip
build:
commands:
- echo Pushing package to Elastic Beanstalk...
- aws elasticbeanstalk create-application-version --application-name $EB_APPLICATION_NAME --version-label v$CODEBUILD_BUILD_NUMBER --description "Auto deployed from CodeCommit build $CODEBUILD_BUILD_NUMBER" --source-bundle S3Bucket="$ARTIFACT_BUCKET",S3Key="$EB_APPLICATION_NAME-$CODEBUILD_BUILD_NUMBER.zip"
- aws elasticbeanstalk update-environment --environment-name "EB-ENV-$EB_APPLICATION_NAME" --version-label v$CODEBUILD_BUILD_NUMBER
The same codepipeline folder contains some build and deploy specification files besides the .NET ones, which you could use if you prefer to use a different framework like Python to deploy a web application with Elastic Beanstalk.
- To complete the application deployment, go to the application pipeline and release the change, which triggers the pipeline with the application environment now ready.

When you create the environment through the AWS Service Catalog, you can access the provisioned Elastic Beanstalk environment.
- In the Events section, locate the
LoadBalancerURL, which is the public endpoint that we use to access the website.

- In our preferred browser, we can check that the website has been successfully deployed.

Cleaning up
When you’re finished, you should complete the following steps to delete the resources you provisioned to avoid incurring further charges and keep the account free of unused resources.
- The CodePipeline product creates an S3 bucket which you must empty from the S3 console.
- On the AWS Service Catalog console, end the provisioned resources from the Provisioned products list.
- As administrator, in the CloudFormation console, delete the stack
SC-RA-Beanstalk-Portfolio.
Conclusions
This post has shown you how to deploy a standardized DevOps pipeline which was then used to manage and deploy a sample .NET application on Elastic Beanstalk using the Service Catalog Elastic Beanstalk reference architecture. AWS Service Catalog is the ideal service for administrators who need to centrally provision and manage the AWS services needed with a consistent governance model. Deploying web applications to Elastic Beanstalk is very simple for developers and provides built in scalability, patch maintenance, and self-healing for your applications.
The post includes the information and references on how to extend the solution with other programming languages and operating systems supported by Elastic Beanstalk.











































 Ease of development
Ease of development